A brand new Mirai-based botnet referred to as NoaBot is being utilized by menace actors as a part of a crypto mining marketing campaign for the reason that starting of 2023.
“The capabilities of the brand new botnet, NoaBot, embody a wormable self-spreader and an SSH key backdoor to obtain and execute further binaries or unfold itself to new victims,” Akamai safety researcher Stiv Kupchik stated in a report shared with The Hacker Information.
Mirai, which had its supply code leaked in 2016, has been the progenitor of a variety of botnets, the latest being InfectedSlurs, which is able to mounting distributed denial-of-service (DDoS) assaults.
There are indications that NoaBot might be linked to a different botnet marketing campaign involving a Rust-based malware household referred to as P2PInfect, which just lately acquired an replace to focus on routers and IoT units.
That is primarily based on the truth that menace actors have additionally experimented with dropping P2PInfect instead of NoaBot in latest assaults concentrating on SSH servers, indicating probably makes an attempt to pivot to customized malware.
Regardless of NaoBot’s Mirai foundations, its spreader module leverages an SSH scanner to seek for servers inclined to dictionary assault in an effort to brute-force them and add an SSH public key within the .ssh/authorized_keys file for distant entry. Optionally, it could possibly additionally obtain and execute further binaries put up profitable exploitation or propagate itself to new victims.
“NoaBot is compiled with uClibc, which appears to vary how antivirus engines detect the malware,” Kupchik famous. “Whereas different Mirai variants are often detected with a Mirai signature, NoaBot’s antivirus signatures are of an SSH scanner or a generic trojan.”
Apart from incorporating obfuscation ways to render evaluation difficult, the assault chain in the end ends in the deployment of a modified model of the XMRig coin miner.
What makes the brand new variant a minimize above different comparable Mirai botnet-based campaigns is that it doesn’t comprise any details about the mining pool or the pockets handle, thereby making it unimaginable to evaluate the profitability of the illicit cryptocurrency mining scheme.
“The miner obfuscates its configuration and in addition makes use of a customized mining pool to keep away from exposing the pockets handle utilized by the miner,” Kupchik stated, highlighting some stage of preparedness of the menace actors.
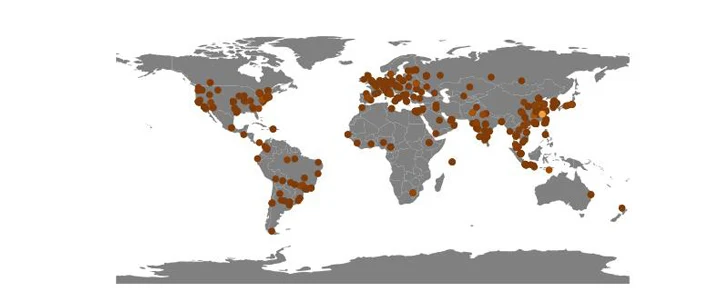
Akamai stated it recognized 849 sufferer IP addresses to this point which can be unfold geographically the world over, with excessive concentrations reported in China, a lot in order that it quantities to virtually 10% of all assaults in opposition to its honeypots in 2023.
“The malware’s methodology of lateral motion is through plain outdated SSH credentials dictionary assaults,” Kupchik stated. “Proscribing arbitrary web SSH entry to your community significantly diminishes the dangers of an infection. As well as, utilizing sturdy (not default or randomly generated) passwords additionally makes your community safer, because the malware makes use of a fundamental listing of guessable passwords.”