Excessive-profile people engaged on Center Jap affairs at universities and analysis organizations in Belgium, France, Gaza, Israel, the U.Okay., and the U.S. have been focused by an Iranian cyber espionage group referred to as Thoughts Sandstorm since November 2023.
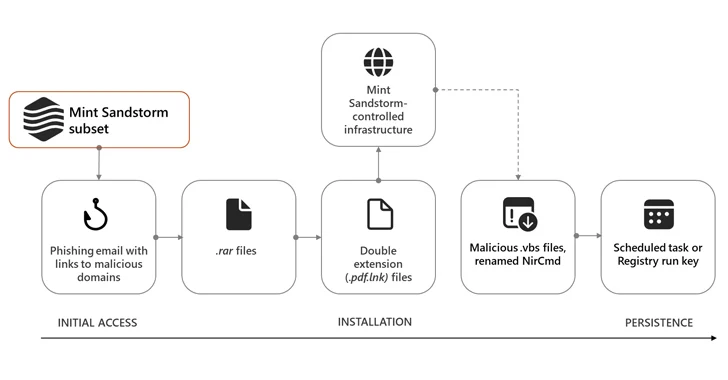
The risk actor “used bespoke phishing lures in an try and socially engineer targets into downloading malicious recordsdata,” the Microsoft Menace Intelligence group stated in a Wednesday evaluation, describing it as a “technically and operationally mature subgroup of Thoughts Sandstorm.”
The assaults, in choose instances, contain using a beforehand undocumented backdoor dubbed MediaPl, indicating ongoing endeavors by Iranian risk actors to refine their post-intrusion tradecraft.
Mint Sandstorm, often known as APT35, Charming Kitten, TA453, and Yellow Garuda, is recognized for its adept social engineering campaigns, even resorting to official however compromised accounts to ship bespoke phishing emails to potential targets. It is assessed to be affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC).
The sub-cluster, per Redmond, engages in resource-intensive social engineering to single out journalists, researchers, professors, and different people with insights on safety and coverage problems with curiosity to Tehran.
The most recent intrusion set is characterised by way of lures pertaining to the Israel-Hamas conflict, sending innocuous emails below the guise of journalists and different high-profile people to construct rapport with targets and set up a degree of belief earlier than making an attempt to ship malware to targets.
Microsoft stated it is possible the marketing campaign is an effort undertaken by the nation-state risk actor to gather views on occasions associated to the conflict.
Using breached accounts belonging to the folks they sought to impersonate in an effort to ship the e-mail messages is a brand new Thoughts Sandstorm tactic not seen earlier than, as is its use of the curl command to connect with the command-and-control (C2) infrastructure.
Ought to the targets interact with the risk actor, they’re despatched a follow-up electronic mail containing a malicious hyperlink that factors to a RAR archive file, which, when opened, results in the retrieval of Visible Primary scripts from the C2 server to persist inside the targets’ environments.
The assault chains additional pave the best way for customized implants like MischiefTut or MediaPl, the previous of which was first disclosed by Microsoft in October 2023.
Carried out in PowerShell, MischiefTut is a primary backdoor that may run reconnaissance instructions, write outputs to a textual content file, and obtain further instruments on a compromised system. The primary recorded use of the malware dates again to late 2022.
MediaPl, then again, masquerades as Home windows Media Participant and is designed to transmit encrypted communications to its C2 server and launch command(s) it has obtained from the server.
“Mint Sandstorm continues to enhance and modify the tooling utilized in targets’ environments, exercise which may assist the group persist in a compromised surroundings and higher evade detection,” Microsoft stated.
“The power to acquire and preserve distant entry to a goal’s system can allow Mint Sandstorm to conduct a variety of actions that may adversely affect the confidentiality of a system.”
The disclosure comes as Dutch newspaper De Volkskrant revealed earlier this month that Erik van Sabben, a Dutch engineer recruited by Israel and U.S. intelligence companies, might have used a water pump to deploy an early variant of the now-infamous Stuxnet malware in an Iranian nuclear facility someday in 2007.