Cyber menace looking is a proactive safety measure taken to detect and neutralize potential threats on a community earlier than they trigger important harm. To hunt out this kind of menace, safety professionals use cyber threat-hunting instruments. These are software program options pushed by superior analytics, machine studying and synthetic intelligence to detect irregular patterns in a system’s community and endpoints. They use methods like behavioral analytics, sample matching, statistical evaluation and AI/ML modeling.
With stories indicating that 72% of companies worldwide had been affected by ransomware assaults in 2023, extra organizations are searching for cyber menace looking options this 12 months.
On this information, we discover the highest cyber threat-hunting instruments for 2024, and evaluate their options, advantages and downsides.
Prime menace looking options comparability
The desk under lists prime menace looking options and the way their options evaluate.
| Deployment mannequin | Centralized Log Assortment | Automated Risk Detection | Superior Risk Looking | 24/7 Monitoring | Pricing | |
|---|---|---|---|---|---|---|
| VMware Carbon Black Endpoint | On-premises, Cloud-based, Hybrid | Sure | Sure | Sure | Sure | Contact vendor for a quote. |
| CrowdStrike Falcon Overwatch | On-premises, Cloud-based | Sure | Sure | Sure | Sure | Contact vendor for a quote. |
| Splunk | On-premises, Cloud-based, Hybrid | Sure | Sure | Sure | Sure | Contact vendor for a quote. |
| SolarWinds Safety Occasion Supervisor | On-premises, cloud-based | Sure | Sure | Sure | Sure | Contact vendor for a quote. |
| Pattern Micro Managed XDR | Cloud-based | Sure | Sure | Supplied as a managed service. | Sure | Contact vendor for a quote. |
| Heimdal Risk Looking and Motion Middle | On-premises, Cloud-based, Hybrid | Sure | Sure | Sure | Sure | Contact vendor for a quote. |
| Cynet 360 AutoXDR | On-premises, IAAS, SAAS and hybrid | Sure | Sure | Sure | Sure + 360-degree safety. | Contact vendor for a quote. |
VMware Carbon Black Endpoint: Finest for offline and hybrid environments

VMware Carbon Black Endpoint, developed by VMware is a threat-hunting device outfitted with behavioral endpoint detection and response (EDR), prolonged detection and response (XDR) and a next-generation antivirus (NGAV). These options mix with its machine studying functionality to ship superior menace looking. The answer repeatedly data and analyzes endpoint exercise and behaviors to detect superior threats.
Leveraging unsupervised machine studying fashions, Carbon Black Endpoint can detect anomalies and suspicious occasions that will point out malicious exercise throughout the cyber kill chain. With the answer, organizations can achieve EDR visibility in offline, hybrid and disconnected environments.
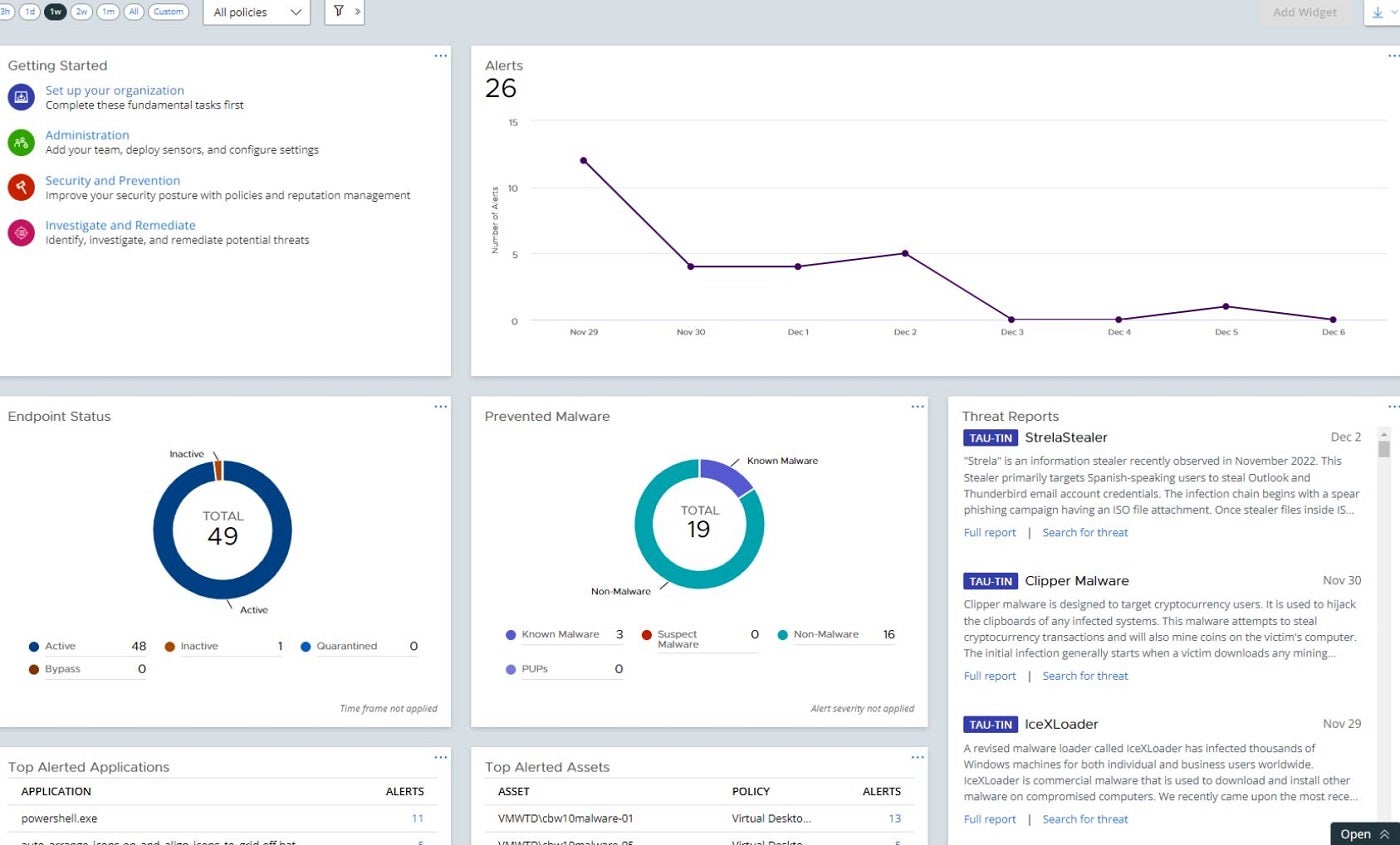
Why we selected VMware Carbon Black Endpoint
VMware Carbon Black Endpoint made it to our listing attributable to its EDR visibility that covers offline, air-gapped and disconnected environments.
Pricing
Attain out to the seller for pricing.
Options
- Subsequent-gen antivirus.
- Behavioral Endpoint Detection and Response (EDR).
- Anomaly detection.
- Elevated endpoint and container visibility.
- Automated menace looking.
Execs
- Integration with widespread safety instruments like Splunk, LogRhythm and Proofpoint.
- Helps compliance and audit options.
- Endpoint visibility inside and outdoors of the company community.
- Superior Predictive Cloud Safety.
- Mutual menace alternate between shoppers.
Cons
- No audit and remediation in the usual model.
CrowdStrike Falcon Overwatch: Finest for superior menace looking

This next-gen SIEM and menace looking resolution from CrowdStrike is built-in with superior EDR and XDR capabilities. CrowdStrike’s Overwatch makes use of its SEARCH methodology to hunt and cease threats. By this technique, CrowdStrike’s Overwatch leverages cloud-scale knowledge, insights from in-house analysts and menace intelligence to mine massive quantities of information for indicators of intrusion or assault. Additionally, its light-weight sensor watches and collects knowledge from an unlimited vary of endpoint occasions uploaded to its cloud storage for evaluation.
One other spectacular function inside Overwatch is the menace graph, which helps cyber analysts decide the origins of threats and the way they might unfold.
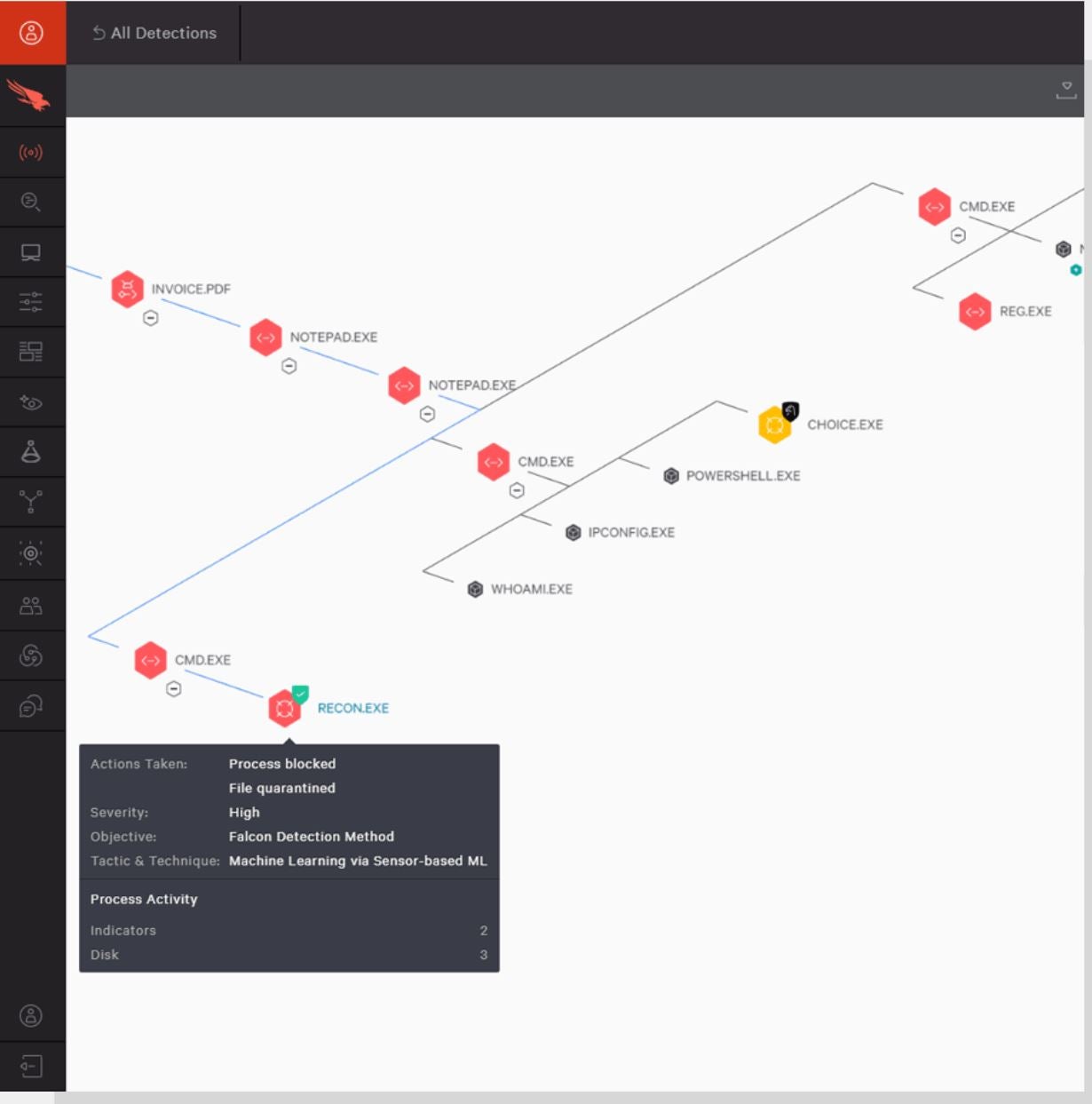
Why we selected CrowdStrike Falcon Overwatch
We selected this resolution for its devoted method to superior menace looking and automatic response to threats, which is achieved by a mix of superior EDR, XDR and proprietary options.
Pricing
The CrowdStrike Falcon Overwatch presents a 15-day free trial and options two plans: the Falcon Overwatch and Falcon Overwatch Elite. Contact the seller for a quote
Options
- Superior EDR and XDR.
- Visibility with Falcon USB System management.
- Automated menace intelligence.
- Risk Graph.
- Firewall administration.
Execs
- Risk alerts are augmented with context.
- Contains choices for managed service.
- Provides a 15-day free trial.
- XDR capabilities for superior menace detection and response.
- Quarterly menace looking stories.
Cons
- Risk looking and investigation teaching are unique to Falcon Overwatch Elite customers.
Splunk: Finest for big enterprises

Splunk presents a cloud, on-premises or hybrid resolution with threat-hunting capabilities. The device integrates insights into the core of its safety info and occasion administration (SIEM) to detect and reply to safety threats. Contemplating its value and capabilities, it’s extra appropriate for bigger enterprises.
With Splunk, customers can create their very own threat-hunting queries, evaluation routines and automatic defensive guidelines. It additionally boasts superior menace detection with about 1,400 detection frameworks and an open, extensible knowledge monitoring platform.
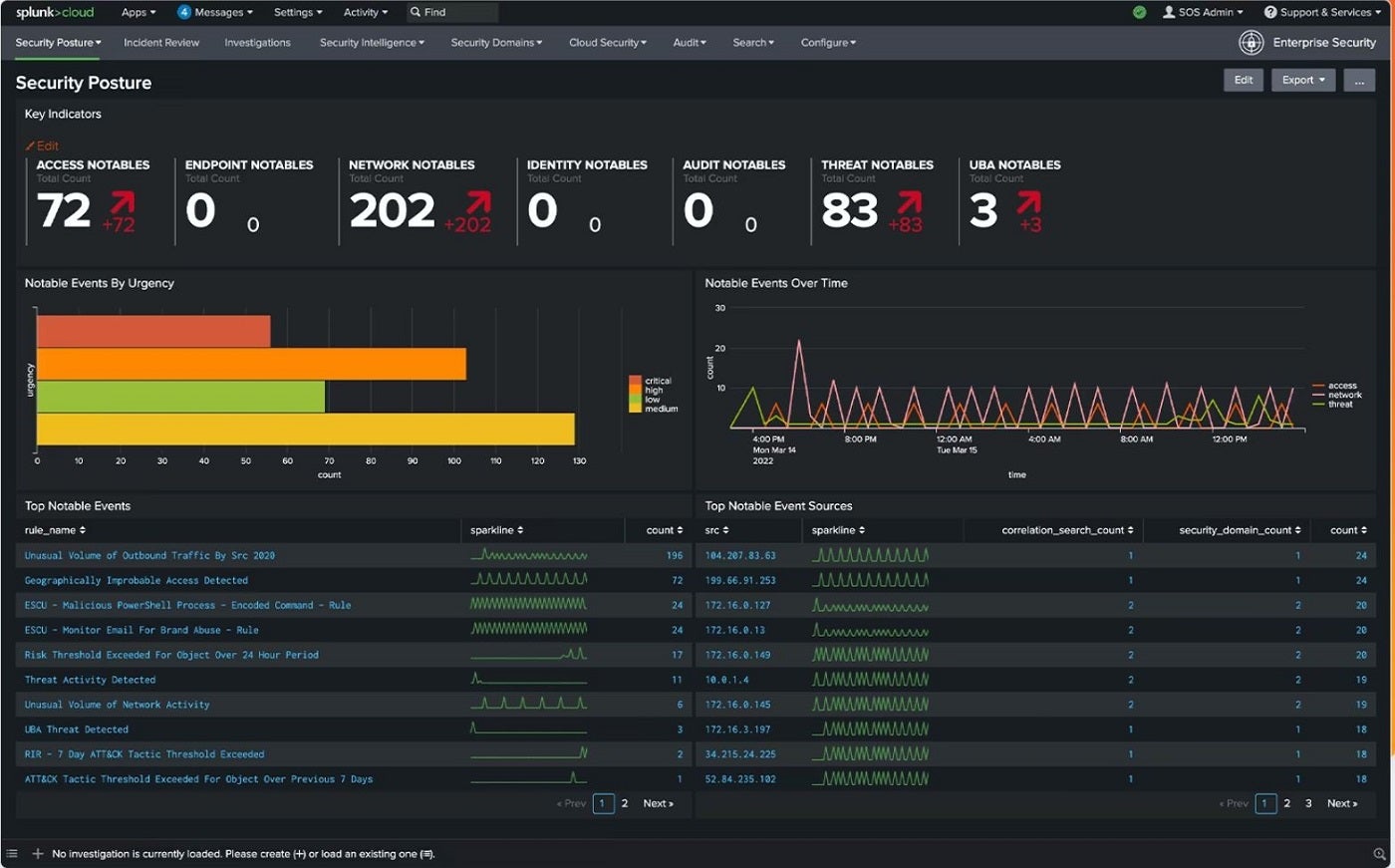
Why we selected Splunk
Splunk was chosen for its variety in cloud, on-premises or hybrid menace looking and in depth detection framework.
Pricing
This resolution presents a 14-day trial interval. For pricing, contact the seller.
Options
- Multi-platform integration.
- Open, extensible knowledge monitoring platform.
- Safety posture dashboard and menace topology.
- Superior menace detection.
- Threat-based alerting.
Execs
- Provides menace intelligence administration.
- Customizable occasion prioritization.
- Versatile deployment choices.
- Speedy and responsive safety content material updates.
- Scalable enterprise-focused menace detection and evaluation.
Cons
SolarWinds Safety Occasion Supervisor: Finest for centralized menace administration

SolarWinds Safety Occasion Supervisor (SEM) delivers its menace looking capabilities by way of a mix of real-time community efficiency statistics and knowledge derived from numerous sources, such because the Easy Community Administration Protocol (SNMP) and log entries. The data derived from SNMP permits the system to collect knowledge about community units, efficiency metrics and different vital facets in real-time.
By parsing and decoding log knowledge, SEM can determine patterns, anomalies and potential threats. This device additionally has a central hub for gathering, analyzing and responding to safety occasions produced by numerous safety applied sciences, similar to firewalls, intrusion detection programs and endpoint safety options.
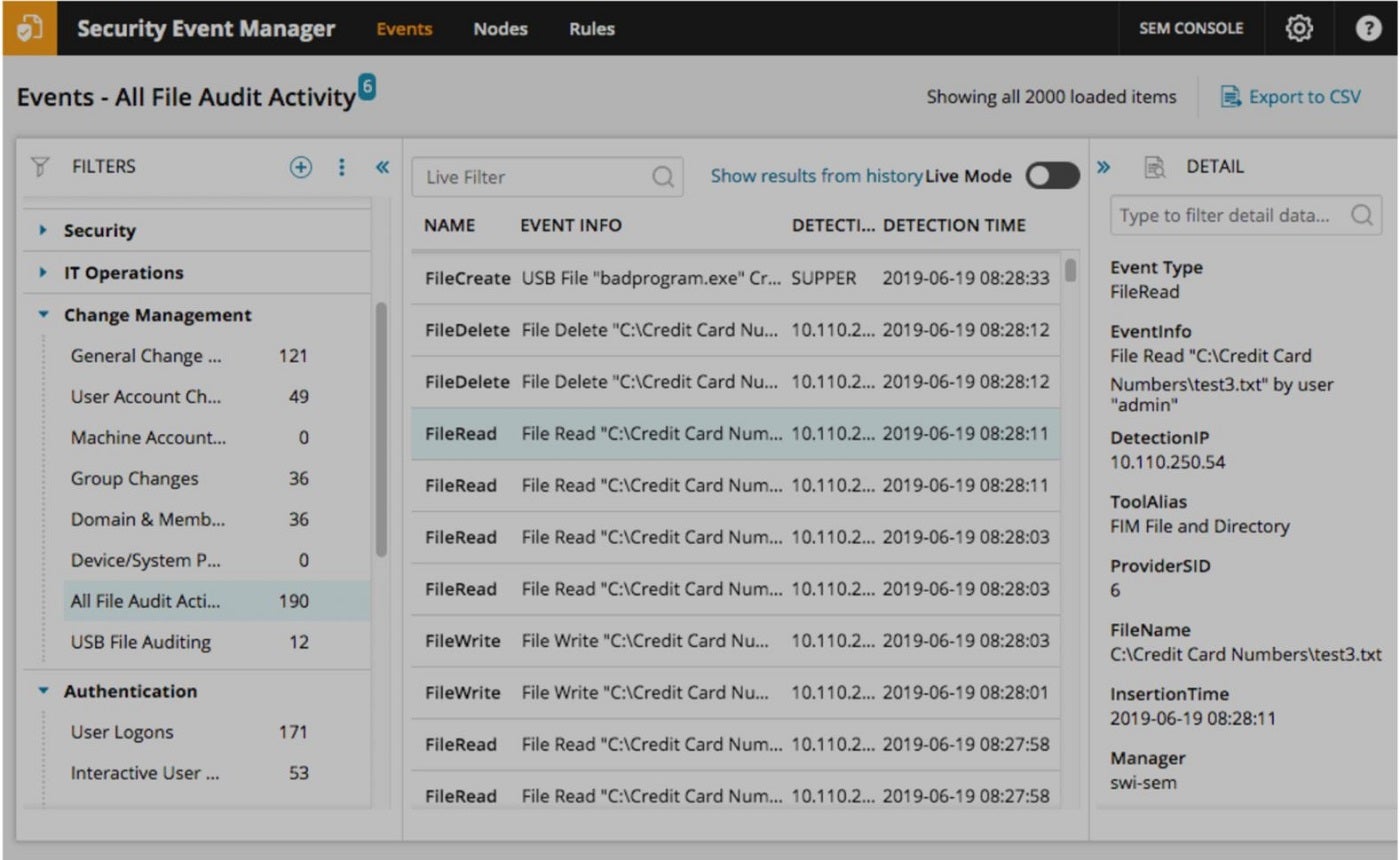
Why we selected SolarWinds Safety Occasion Supervisor
This device was chosen attributable to its centralized platform and seamless integration with numerous safety applied sciences, providing streamlined safety administration.
Pricing
SolarWinds Occasion Supervisor presents subscription and perpetual licensing plans. Contact the seller for a customized quote.
Options
- Constructed-in file integrity monitoring.
- Centralized log assortment and normalization.
- Built-in compliance reporting instruments.
- Superior pfSense firewall log analyzer.
- Superior persistent menace (APT) safety software program.
Execs
- Provides real-time community efficiency statistics.
- Centralized logon audit occasions monitor for monitoring of safety occasions.
- Improved safety, real-time monitoring and troubleshooting with superior pfSense firewall log analyzer.
- Integrates with numerous safety applied sciences for higher visibility.
- Supplies in-depth evaluation of log entries to reinforce menace detection.
Cons
- Absence of cloud model.
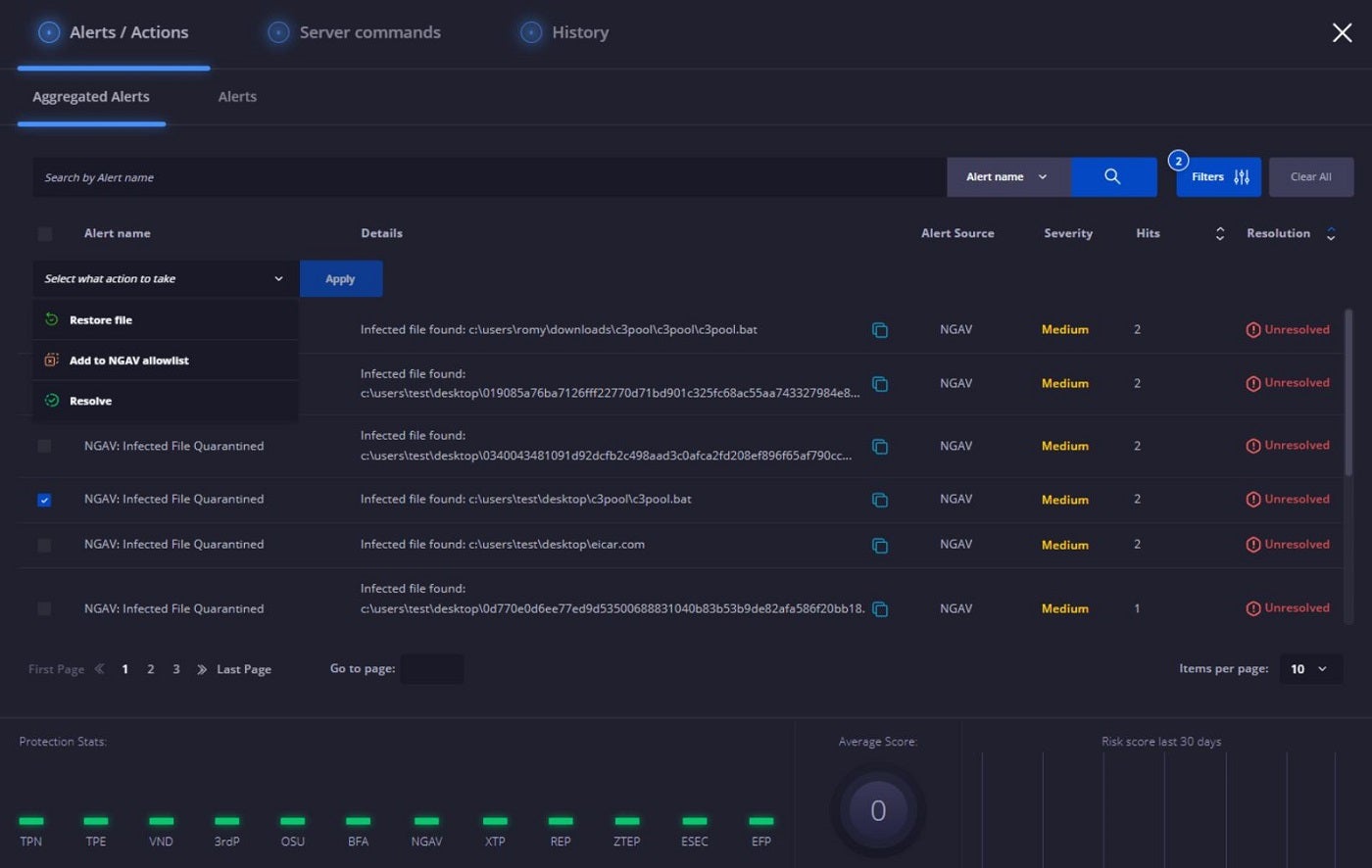
Pattern Micro Managed XDR: Finest for devoted SOC assist

Pattern Micro Managed XDR is a safety service that gives 24/7 monitoring and evaluation. It stands out for its capacity to correlate knowledge from a variety of sources, together with electronic mail, endpoint, server, cloud, workload and community. This cross-layered method enhances menace looking and supplies larger perception into the supply and unfold of focused assaults. The answer repeatedly scans for indicators of compromise or assault, together with these shared by way of US-CERT and third-party disclosures, making certain a proactive method to menace looking.
Along with the above options, Managed XDR supplies devoted assist for Safety Operations Middle (SOC) groups, decreasing the time to determine, examine and reply to threats. As a part of Pattern Service One, it contains premium assist and incident response companies, extending its worth throughout the product.
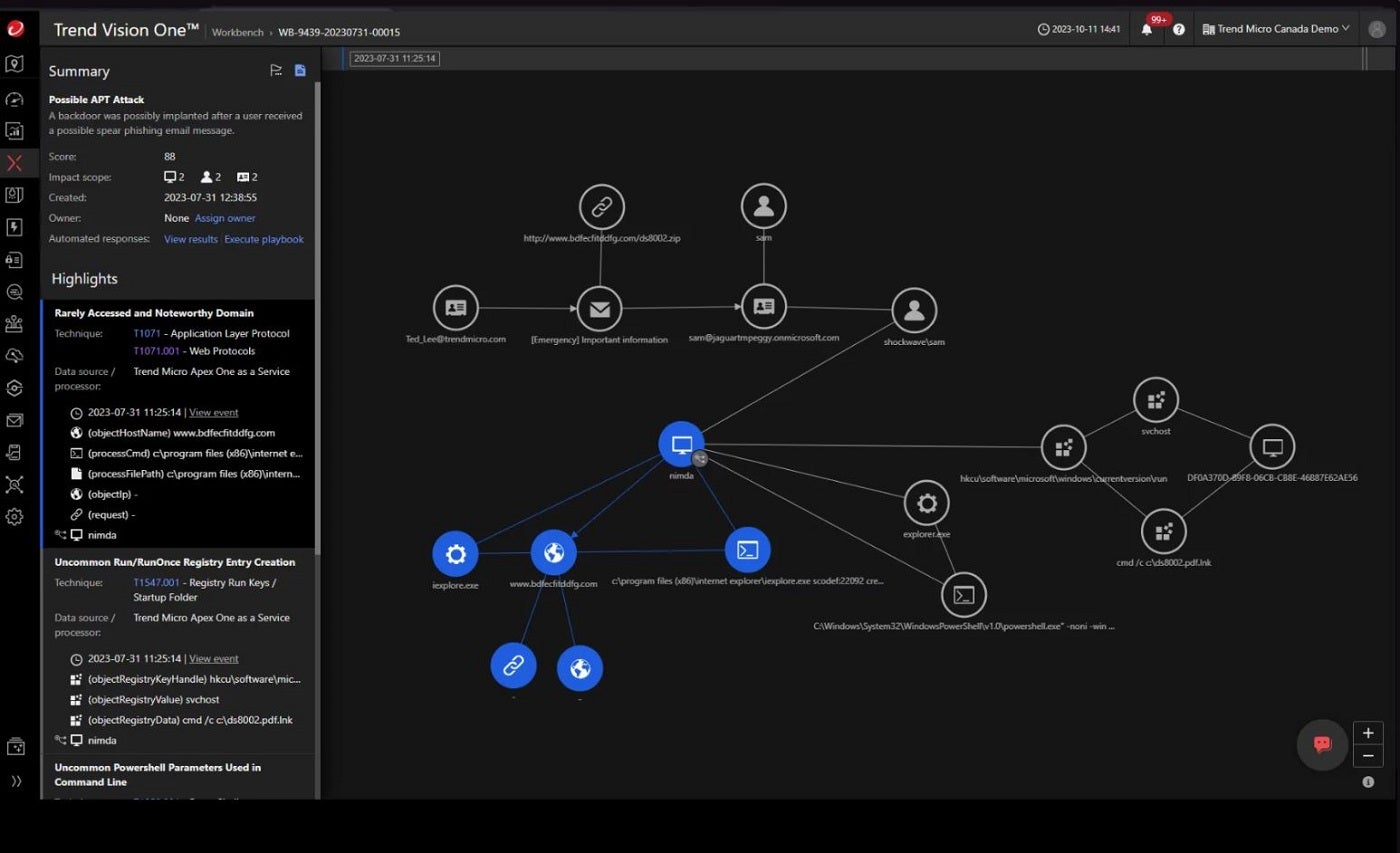
Why we selected Pattern Micro Managed XDR
We selected Pattern Micro Managed XDR for its 24/7 assist for Safety Operations Middle (SOC) groups, and its threat-hunting capabilities that improve time-to-detect and time-to-respond efficiency.
Pricing
Pattern Micro Managed XDR presents a 30-day free trial. Contact the seller for pricing.
Options
- Endpoint detection and response.
- 24/7 evaluation and monitoring.
- Superior menace intelligence.
- Cross-layered detection and response.
- Optimized safety analytics.
Execs
- Devoted assist for SOC and IT safety groups.
- Provides server and electronic mail safety.
- Proactive menace attempting to find superior threats.
- Incorporates threats and robotically generates IoCs to stop future assaults.
- Generates menace alerts and detailed incident stories.
Cons
- Lack of on-premises resolution.
Heimdal Risk Looking and Motion Middle: Finest for single-command menace mitigation

Heimdal’s menace looking and detection resolution equips SecOps groups and IT directors with instruments for figuring out and monitoring anomalous habits throughout units and networks. Leveraging its superior XTP engine, the Heimdal suite and the MITRE ATT&CK framework, this platform visualizes related info associated to endpoints for network-level menace detection.
Customers achieve insights by way of threat scores and forensic evaluation, which boosts their understanding of potential threats. The continual scanning by the XTP engine provides a strategic layer to menace identification and monitoring, permitting for immediate remediation with a single command wherever threats are recognized.
Why we selected Heimdal Risk Looking and Motion Middle
This resolution stands out due to its one-click execution of instructions like scanning, quarantine and isolation, together with in-depth incident investigation powered by its Motion Middle.
Pricing
Contact the seller for a quote.
Options
- Subsequent-gen antivirus, firewall and cellular system administration (MDM).
- Incident investigation and administration.
- Exercise monitoring and monitoring.
- XTP Engine and MITRE ATT&CK framework.
- Quarantine performance.
Execs
- Supplies a centralized listing of the threats detected.
- Actual-time menace monitoring and alerts are supplied.
- Makes for immediate reporting and statistics.
- Single-command remediation is feasible with the motion heart.
- Supplies a unified view for intelligence, looking and response.
Cons
- No pricing info accessible on-line.
Cynet 360 AutoXDR: Finest for modern menace looking

Cynet 360 is an enterprise-level threat-hunting resolution that makes use of machine studying and behavioral evaluation to determine suspicious habits/anomalies inside a community. It natively consolidates important safety applied sciences right into a unified XDR platform and presents MDR companies, together with monitoring, investigation, on-demand evaluation and incident response.
Moreover, the device presents a Cynet Deception function that makes use of several types of decoys — like faux knowledge recordsdata, credentials and community connections — to hunt threats at totally different ranges of a system. When an intruder interacts with these decoys, like logging in with a faux password or opening a faux knowledge file, it units off an alert on the potential menace. The deception function lets customers arrange faux recordsdata, customers, hosts and networks to uncover intruders within the system.

Why we selected Cynet 360 AutoXDR
Cynet 360 made it to our listing following its modern method to menace looking executed by way of its deception function that units up decoy tokens for menace detection.
Pricing
This resolution presents a 14-day free trial interval with no pricing choice. Contact the seller for pricing.
Options
- Centralized menace administration dashboard.
- Subsequent-generation antivirus.
- Devoted menace response group.
- Deployment and configuration managed service.
- Cynet deception.
Execs
- Provides menace detection and alerts.
- Provides modern menace looking and mitigation with Cynet Deception.
- Supplies superior reporting and evaluation.
- CyOps MDR Staff assists in figuring out malicious recordsdata and processes.
- Provides automated menace evaluation and remediation.
Cons
- No displayed log supervisor.
Key Options of Cyber Risk Looking Instruments
From log evaluation and proactive menace identification to intelligence sharing, menace looking options could be outfitted with a number of options that separate them from conventional safety monitoring instruments. Under are some key options each threat-hunting device ought to possess.
Information assortment and evaluation
Risk looking instruments collect and mixture huge quantities of information from numerous sources, similar to logs, occasions, endpoint telemetry and community site visitors. Leveraging superior analytics and machine studying, uncommon patterns and anomalies are decided. These options improve their understanding of potential threats by reviewing or scrutinizing alerts from SIEM programs and Intrusion detection programs (IDS). They analyze the information gathered from firewalls, IDS, DNS, file and person knowledge, antivirus options and different safety units for higher perception on what to categorize as potential threats and greatest remediation channels.
Proactive search and identification of threats
This function helps safety analysts discover and examine in depth knowledge collected from numerous sources. The superior search and question language assist permits them to go looking, filter and question the information. To do that, safety groups can customise and streamline their searches based mostly on sure organizational necessities to extract info like time ranges, particular IP addresses, person accounts or kinds of actions. Probably the most essential facets of this function is that not solely does it carry out real-time evaluation by querying dwell knowledge streams to determine ongoing threats promptly, however it additionally performs historic knowledge evaluation that identifies previous incidents or patterns that may have gone unnoticed initially.
Collaboration and intelligence sharing
Risk looking goes past particular person initiatives, as the information collected and processed individually can be restricted. Efficient collaboration and intelligence sharing amongst organizations, safety groups, and trade companions are important, and this will solely be achieved by integrating sharable menace intelligence feeds in menace looking instruments. The alternate of menace intelligence, techniques, methods and procedures (TTPs) facilitates menace looking and remediation throughout numerous organizations.
Behavioral evaluation
Risk-hunting instruments depend on behavioral evaluation to study and perceive regular patterns of person and system habits. They then make the most of methods similar to person and entity habits analytics (UEBA), machine studying algorithms and steady monitoring to determine anomalies, present context and allow early menace detection. This function additionally helps cut back false positives and enhances proactive identification and response to safety dangers.
Automated response
This function prioritizes alerts based mostly on predefined standards, making certain that vital or recognized threats obtain speedy consideration. It contains dynamic playbooks, integration with safety orchestration platforms and actions similar to incident containment and isolation, person account remediation and alert prioritization. With automated responses, organizations can cut back dwell time, make incident response extra environment friendly and obtain compliance with safety insurance policies whereas making certain that their community and programs are protected in opposition to safety dangers and threats.
How do I select one of the best cyber threat-hunting device for my enterprise?
Selecting one of the best cyber threat-hunting device to your particular person or enterprise wants borders on many elements, together with your private or enterprise goals, how the device matches into your present safety infrastructure and your price range. These seven instruments are nice threat-hunting instruments, relying in your private/enterprise wants.
For instance, in the event you want an modern threat-hunting device that makes use of a singular method to menace looking, the Cynet 360 is your greatest wager. If a single motion remediation that encompasses scanning, quarantine and isolation together with an in-depth incident investigation is your purpose, then the Heimdal Risk Looking and Motion Middle is the best choice. The identical applies to different instruments, as they every have a singular method to menace looking and remediation.
Nevertheless, as with all device, its effectiveness will rely on how properly it’s built-in into a corporation’s present infrastructure and safety protocols. It’s at all times beneficial to guage these instruments within the context of your group’s particular wants and challenges.
Evaluation methodology
For this overview, I thought-about essential options of threat-hunting options, the various approaches every device makes use of to detect threats, their remediation processes, integration capabilities with present programs and whether or not the distributors provided personalised assist. I gathered info from the totally different distributors’ web sites and overview websites like Gartner to realize extra perception on every device. I additionally thought-about the builders’ reputations and the place they stand within the trade.
