Authored by Dexter Shin
MoqHao is a widely known Android malware household related to the Roaming Mantis menace actor group first found in 2015. McAfee Cellular Analysis Group has additionally posted a number of articles associated to this malware household that historically targets Asian international locations resembling Korea and Japan.
Not too long ago McAfee Cellular Analysis Group discovered that MoqHao started distributing variants utilizing very harmful approach. Principally, the distribution methodology is identical. They ship a hyperlink to obtain the malicious app by way of the SMS message. Typical MoqHao requires customers to put in and launch the app to get their desired objective, however this new variant requires no execution. Whereas the app is put in, their malicious exercise begins mechanically. This method was launched in a earlier put up however the distinction is that this harmful approach is now being abused by different well-known lively malware campaigns like MoqHao. We’ve already reported this method to Google and they’re already engaged on the implementation of mitigations to stop one of these auto-execution in a future Android model. Android customers are at present protected by Google Play Defend, which is on by default on Android gadgets with Google Play Companies. Google Play Defend can warn customers or block apps identified to exhibit malicious conduct, even when these apps come from sources outdoors of Play. McAfee Cellular Safety detects this menace as Android/MoqHao.
How it’s distributed
MoqHao is distributed by way of phishing SMS messages (also called Smishing). When a person receives an SMS message containing a malicious hyperlink and clicks it, the gadget downloads the malicious software. Phishing messages are nearly the identical as in earlier campaigns:
Determine 1. Smishing message impersonating a notification from a courier service.
Japanese message: I went to the supply tackle, however nobody was there. So, I introduced it again.
One noticeable change is that they now use URL shortener providers. If the malware authors use their very own area, it may be shortly blocked but when they use official URL shortener providers, it’s troublesome to dam the quick area as a result of it might have an effect on all of the URLs utilized by that service. When a person clicks on the hyperlink within the message, it will likely be redirected to the precise malicious website by the URL shortener service.
What’s new on this variant
As talked about in the beginning, this variant behaves in another way from earlier ones. Typical MoqHao should be launched manually by the person after it’s put in however this variant launches mechanically after set up with out person interplay:
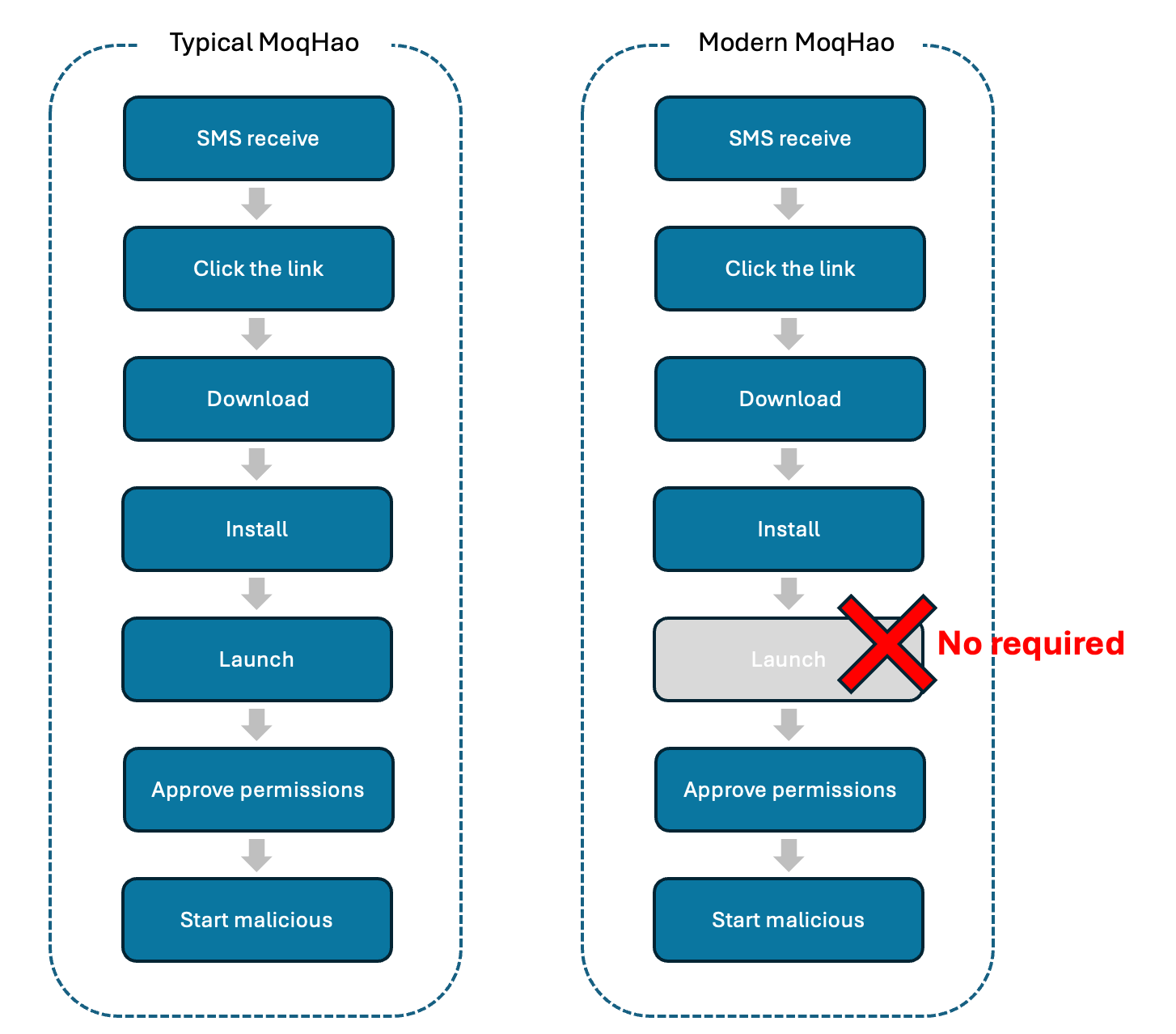
Determine 2. Variations between typical MoqHao and Fashionable MoqHao
We defined this auto-execution approach intimately in a earlier put up however to briefly summarize it right here, Android is designed so when an app is put in and a particular worth utilized by the app is ready to be distinctive, the code runs to verify whether or not the worth is exclusive upon set up. This function is the one that’s being abused by the extremely lively Trojan household MoqHao to auto-execute itself with out person interplay. The distribution, set up, and auto-execution of this current MoqHao variant could be seen within the following video:
On the opposite hand, this current MoqHao variant makes use of Unicode strings in app names in another way than earlier than. This approach makes some characters seem daring, however customers visually acknowledge it as “Chrome”. This may occasionally have an effect on app name-based detection methods that examine app identify (Chrome) and package deal identify (com.android.chrome):

Determine 3. App identify utilizing Unicode strings.
Moreover, in addition they use social engineering methods to set malicious apps because the default SMS app. Earlier than the settings window seems, they present a message telling you to arrange the app to stop spam, but this message is pretend:

Determine 4. Faux message utilizing social engineering methods.
Additionally, the totally different languages used within the textual content related to this conduct means that, along with Japan, they are additionally focusing on South Korea, France, Germany, and India:
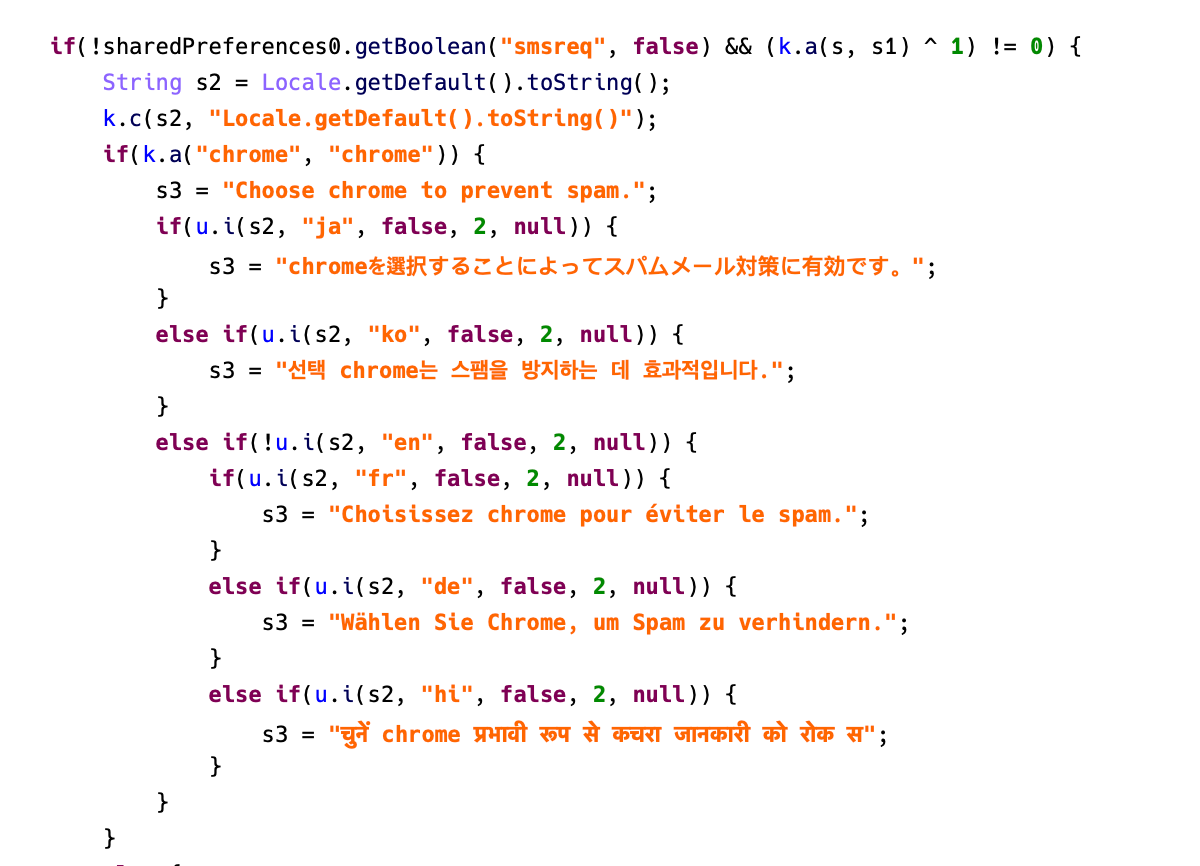
Determine 5. Faux messages designed to focus on totally different international locations.
After the initialization of the malware is accomplished, it will create a notification channel that can be used to show phishing messages:
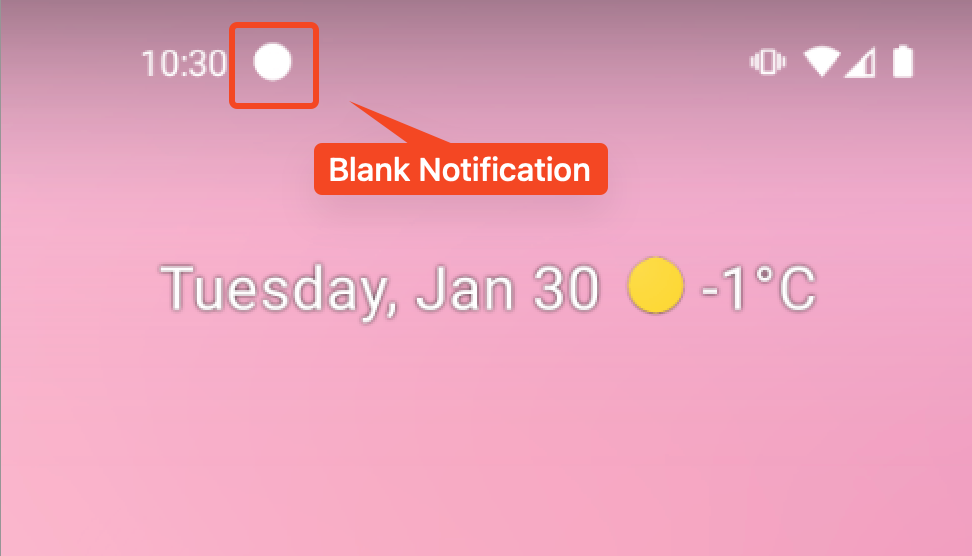
Determine 6. Create a notification channel for the following phishing assault.
The malware checks the gadget’s provider and makes use of this notification to ship phishing messages accordingly to trick customers into click oning on them. MoqHao will get the phishing message and the phishing URL from Pinterest profiles.
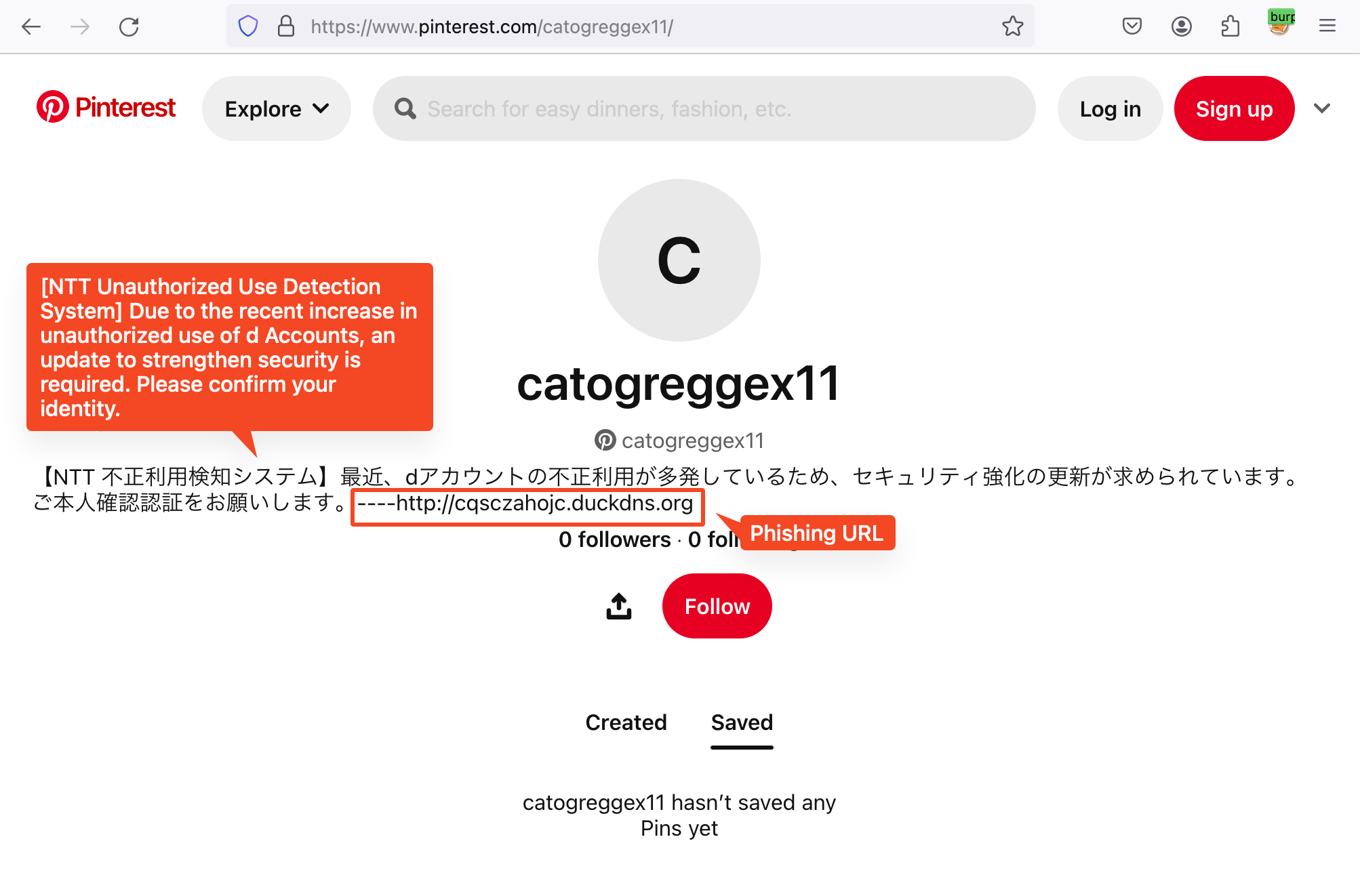
Determine 7. Phishing message and URL in Pinterest profile
If the phishing string is empty, MoqHao will use the phishing message within the code:
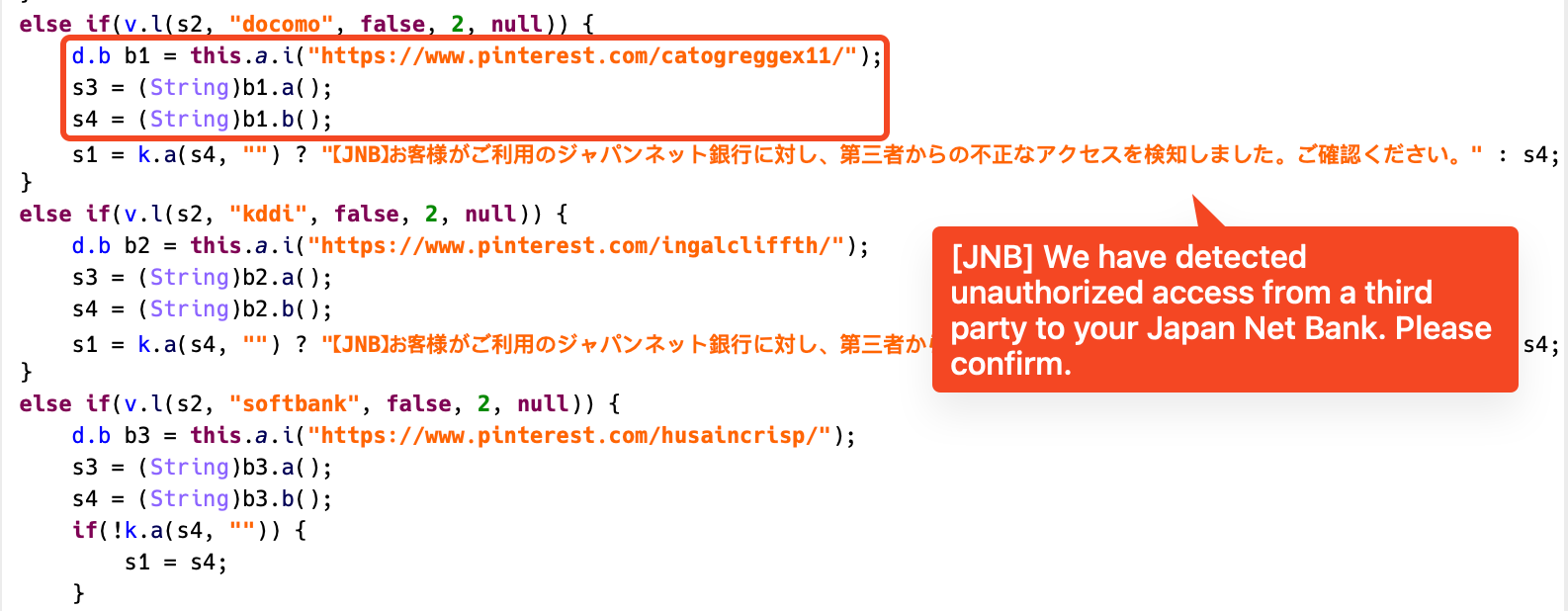
Determine 8. Phishing notification code for every provider
This variant additionally connects to the C2 server by way of WebSocket. Nonetheless, it has been confirmed that a number of different instructions have been added along with the instructions launched in the earlier put up:
| Command | Description |
| getSmsKW | Ship all SMS messages to C2 server |
| sendSms | Ship SMS messages to somebody |
| setWifi | Allow/disable Wifi |
| gcont | Ship complete contacts to C2 server |
| lock | Retailer Boolean worth in “lock” key in SharedPreferences |
| bc | Verify SIM state |
| setForward | Retailer String worth in “fs” key in SharedPreferences |
| getForward | Get String worth in “fs” key in SharedPreferences |
| hasPkg | Verify particular package deal put in on gadget |
| setRingerMode | Set Sound/Vibrate/Silent mode |
| setRecEnable | Set Vibrate/Silent mode in keeping with SDK model |
| reqState | Ship gadget info (Community, Energy, MAC, Permission) to C2 server |
| showHome | Emulate Dwelling button click on |
| getnpki | Ship Korean Public Certificates (NPKI) to C2 server |
| http | Ship HTTP requests |
| name | Name a particular quantity with Silent mode |
| get_apps | Get listing of put in packages |
| ping | Verify C2 server standing |
| getPhoneState | Get distinctive info resembling IMEI, SIM quantity, Android ID, and serial quantity |
| get_photo | Ship all images to C2 server |
MoqHao malware household is an lively malware that has been round for years. Though a few years have handed, they’re utilizing an increasing number of other ways to cover and attain customers. We’re seeing a a lot greater variety of C2 instructions than in earlier, the lively use of official websites like Pinterest to retailer and replace phishing information, and code with the potential to focus on Asian international locations like Japan and South Korea, in addition to international locations like France, Germany, and India. Furthermore, we count on this new variant to be extremely impactful as a result of it infects gadgets just by being put in with out execution.
It’s troublesome for common customers to seek out pretend apps utilizing official icons and software names, so we advocate customers to put in safe software program to guard their gadgets. For extra info, go to McAfee Cellular Safety.
Indicators of Compromise (IOCs)
| SHA256 | Software Identify | Package deal Identify |
| 2576a166d3b18eafc2e35a7de3e5549419d10ce62e0eeb24bad5a1daaa257528 | chom | gb.pi.xcxr.xd |
| 61b4cca67762a4cf31209056ea17b6fb212e175ca330015d804122ee6481688e | hm | malmkb.zdbd.ivakf.lrhrgf |
| b044804cf731cd7dd79000b7c6abce7b642402b275c1eb25712607fc1e5e3d2b | cm | vfqhqd.msk.xux.njs |
| bf102125a6fca5e96aed855b45bbed9aa0bc964198ce207f2e63a71487ad793a | chro | hohoj.vlcwu.lm.ext |
| e72f46f15e50ce7cee5c4c0c5a5277e8be4bb3dd23d08ea79e1deacb8f004136 | hroe | enech.hg.rrfy.wrlpp |
| f6323f8d8cfa4b5053c65f8c1862a8e6844b35b260f61735b3cf8d19990fef42 | chre | gqjoyp.cixq.zbh.llr |
