There are indications that U.S. healthcare big Change Healthcare has made a $22 million extortion fee to the notorious BlackCat ransomware group (a.okay.a. “ALPHV“) as the corporate struggles to convey providers again on-line amid a cyberattack that has disrupted prescription drug providers nationwide for weeks. Nonetheless, the cybercriminal who claims to have given BlackCat entry to Change’s community says the crime gang cheated them out of their share of the ransom, and that they nonetheless have the delicate knowledge Change reportedly paid the group to destroy. In the meantime, the affiliate’s disclosure seems to have prompted BlackCat to stop operations solely.

Picture: Varonis.
Within the third week of February, a cyber intrusion at Change Healthcare started shutting down vital healthcare providers as firm methods had been taken offline. It quickly emerged that BlackCat was behind the assault, which has disrupted the supply of prescribed drugs for hospitals and pharmacies nationwide for almost two weeks.
On March 1, a cryptocurrency deal with that safety researchers had already mapped to BlackCat acquired a single transaction price roughly $22 million. On March 3, a BlackCat affiliate posted a grievance to the unique Russian-language ransomware discussion board Ramp saying that Change Healthcare had paid a $22 million ransom for a decryption key, and to forestall 4 terabytes of stolen knowledge from being printed on-line.
The affiliate claimed BlackCat/ALPHV took the $22 million fee however by no means paid him his share of the ransom. BlackCat is named a “ransomware-as-service” collective, that means they depend on freelancers or associates to contaminate new networks with their ransomware. And people associates in flip earn commissions starting from 60 to 90 % of any ransom quantity paid.
“However after receiving the fee ALPHV staff determine to droop our account and preserve mendacity and delaying once we contacted ALPHV admin,” the affiliate “Notchy” wrote. “Sadly for Change Healthcare, their knowledge [is] nonetheless with us.”
Change Healthcare has neither confirmed nor denied paying, and has responded to a number of media shops with an analogous non-denial assertion — that the corporate is concentrated on its investigation and on restoring providers.
Assuming Change Healthcare did pay to maintain their knowledge from being printed, that technique appears to have gone awry: Notchy stated the listing of affected Change Healthcare companions they’d stolen delicate knowledge from included Medicare and a bunch of different main insurance coverage and pharmacy networks.
On the intense aspect, Notchy’s grievance appears to have been the ultimate nail within the coffin for the BlackCat ransomware group, which was infiltrated by the FBI and overseas regulation enforcement companions in late December 2023. As a part of that motion, the federal government seized the BlackCat web site and launched a decryption device to assist victims get better their methods.
BlackCat responded by re-forming, and growing affiliate commissions to as a lot as 90 %. The ransomware group additionally declared it was formally eradicating any restrictions or discouragement in opposition to focusing on hospitals and healthcare suppliers.
Nonetheless, as a substitute of responding that they might compensate and placate Notchy, a consultant for BlackCat stated at present the group was shutting down and that it had already discovered a purchaser for its ransomware supply code.
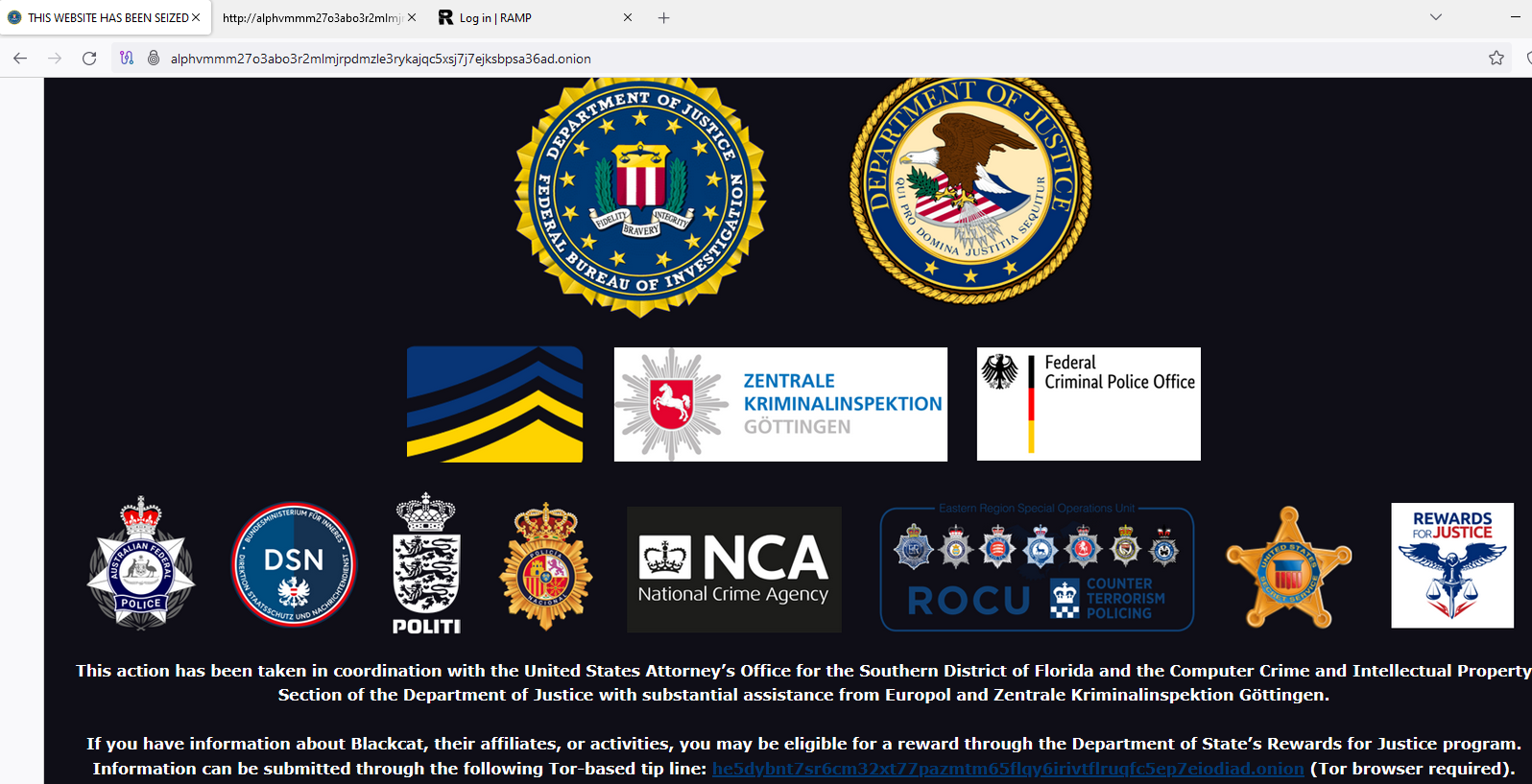
The seizure discover now displayed on the BlackCat darknet web site.
“There’s no sense in making excuses,” wrote the RAMP member “Ransom.” “Sure, we knew about the issue, and we had been attempting to unravel it. We advised the affiliate to attend. We may ship you our non-public chat logs the place we’re shocked by the whole lot that’s occurring and are attempting to unravel the problem with the transactions through the use of the next price, however there’s no sense in doing that as a result of we determined to totally shut the mission. We will formally state that we acquired screwed by the feds.”
BlackCat’s web site now incorporates a seizure discover from the FBI, however a number of researchers famous that this picture appears to have been merely minimize and pasted from the discover the FBI left in its December raid of BlackCat’s community. The FBI has not responded to requests for remark.
Fabian Wosar, head of ransomware analysis on the safety agency Emsisoft, stated it seems BlackCat leaders are attempting to drag an “exit rip-off” on associates by withholding many ransomware fee commissions without delay and shutting down the service.
“ALPHV/BlackCat didn’t get seized,” Wosar wrote on Twitter/X at present. “They’re exit scamming their associates. It’s blatantly apparent once you verify the supply code of their new takedown discover.”
Dmitry Smilyanets, a researcher for the safety agency Recorded Future, stated BlackCat’s exit rip-off was particularly harmful as a result of the affiliate nonetheless has all of the stolen knowledge, and will nonetheless demand extra fee or leak the data on his personal.
“The associates nonetheless have this knowledge, they usually’re mad they didn’t obtain this cash, Smilyanets advised Wired.com. “It’s an excellent lesson for everybody. You can not belief criminals; their phrase is price nothing.”

BlackCat’s obvious demise comes intently on the heels of the implosion of one other main ransomware group — LockBit, a ransomware gang estimated to have extorted over $120 million in funds from greater than 2,000 victims worldwide. On Feb. 20, LockBit’s web site was seized by the FBI and the U.Ok.’s Nationwide Crime Company (NCA) following a months-long infiltration of the group.
LockBit additionally tried to revive its popularity on the cybercrime boards by resurrecting itself at a brand new darknet web site, and by threatening to launch knowledge from numerous main firms that had been hacked by the group within the weeks and days previous to the FBI takedown.
However LockBit seems to have since misplaced any credibility the group could have as soon as had. After a much-promoted assault on the federal government of Fulton County, Ga., for instance, LockBit threatened to launch Fulton County’s knowledge except paid a ransom by Feb. 29. However when Feb. 29 rolled out, LockBit merely deleted the entry for Fulton County from its website, together with these of a number of monetary organizations that had beforehand been extorted by the group.
Fulton County held a press convention to say that it had not paid a ransom to LockBit, nor had anybody carried out so on their behalf, and that they had been simply as mystified as everybody else as to why LockBit by no means adopted by way of on its risk to publish the county’s knowledge. Exerts advised KrebsOnSecurity LockBit doubtless balked as a result of it was bluffing, and that the FBI doubtless relieved them of that knowledge of their raid.
Smilyanets’ feedback are pushed dwelling in revelations first printed final month by Recorded Future, which quoted an NCA official as saying LockBit by no means deleted the info after being paid a ransom, regardless that that’s the solely motive lots of its victims paid.
“If we don’t offer you decrypters, or we don’t delete your knowledge after fee, then no one pays us sooner or later,” LockBit’s extortion notes sometimes learn.
Hopefully, extra firms are beginning to get the memo that paying cybercrooks to delete stolen knowledge is a dropping proposition throughout.
