Menace actors are focusing on misconfigured and susceptible servers working Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis providers as a part of an rising malware marketing campaign designed to ship a cryptocurrency miner and spawn a reverse shell for persistent distant entry.
“The attackers leverage these instruments to challenge exploit code, profiting from widespread misconfigurations and exploiting an N-day vulnerability, to conduct Distant Code Execution (RCE) assaults and infect new hosts,” Cado safety researcher Matt Muir stated in a report shared with The Hacker Information.
The exercise has been codenamed Spinning YARN by the cloud safety firm, with overlaps to cloud assaults attributed to TeamTNT, WatchDog, and a cluster dubbed Kiss-a-dog.
All of it begins with deploying 4 novel Golang payloads which can be able to automating the identification and exploitation of vulnerable Confluence, Docker, Hadoop YARN, and Redis hosts. The spreader utilities leverage masscan or pnscan to hunt for these providers.
“For the Docker compromise, the attackers spawn a container and escape from it onto the underlying host,” Muir defined.
The preliminary entry then paves the best way for the deployment of extra instruments to put in rootkits like libprocesshider and diamorphine to hide malicious processes, drop the Platypus open-source reverse shell utility, and finally launch the XMRig miner.
“It is clear that attackers are investing important time into understanding the varieties of web-facing providers deployed in cloud environments, preserving abreast of reported vulnerabilities in these providers and utilizing this information to realize a foothold in goal environments,” the corporate stated.
The event comes as Uptycs revealed 8220 Gang’s exploitation of recognized safety flaws in Apache Log4j (CVE-2021-44228) and Atlassian Confluence Server and Information Heart (CVE-2022-26134) as a part of a wave of assaults focusing on cloud infrastructure from Might 2023 by way of February 2024.
“By leveraging web scans for susceptible functions, the group identifies potential entry factors into cloud methods, exploiting unpatched vulnerabilities to realize unauthorized entry,” safety researchers Tejaswini Sandapolla and Shilpesh Trivedi stated.
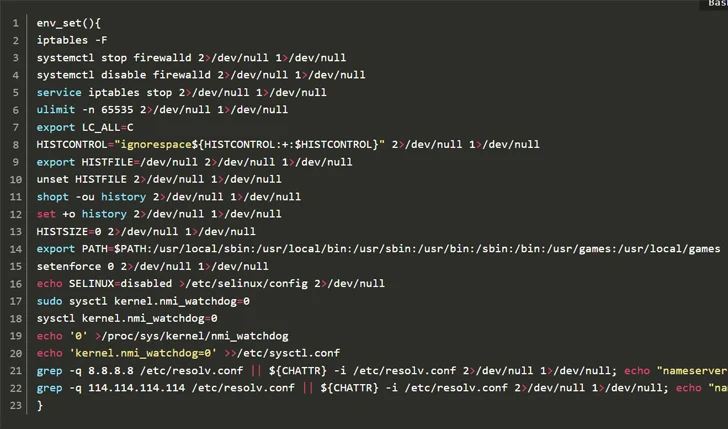
“As soon as inside, they deploy a sequence of superior evasion strategies, demonstrating a profound understanding of methods to navigate and manipulate cloud environments to their benefit. This consists of disabling safety enforcement, modifying firewall guidelines, and eradicating cloud safety providers, thereby guaranteeing their malicious actions stay undetected.”
The assaults, which single out each Home windows and Linux hosts, goal to deploy a cryptocurrency miner, however not earlier than taking a sequence of steps that prioritize stealth and evasion.
It additionally follows the abuse of cloud providers primarily meant for synthetic intelligence (AI) options to drop cryptocurrency miners in addition to host malware.
“With each mining and AI requiring entry to giant quantities of GPU processing energy, there is a sure diploma of transferability to their base {hardware} environments,” HiddenLayer famous final yr.
Cado, in its H2 2023 Cloud Menace Findings Report, famous that menace actors are more and more focusing on cloud providers that require specialist technical data to use, and that cryptojacking is not the one motive.
“With the invention of recent Linux variants of ransomware households, equivalent to Abyss Locker, there’s a worrying development of ransomware on Linux and ESXi methods,” it stated. “Cloud and Linux infrastructure is now topic to a broader number of assaults.”