
Getty Pictures
Researchers have unearthed never-before-seen wiper malware tied to the Kremlin and an operation two years in the past that took out greater than 10,000 satellite tv for pc modems situated primarily in Ukraine on the eve of Russia’s invasion of its neighboring nation.
AcidPour, as researchers from safety agency Sentinel One have named the brand new malware, has stark similarities to AcidRain, a wiper found in March 2022 that Viasat has confirmed was used within the assault on its modems earlier that month. Wipers are malicious purposes designed to destroy saved information or render units inoperable. Viasat mentioned AcidRain was put in on greater than 10,000 Eutelsat KA-SAT modems utilized by the broadband supplier seven days previous to the March 2022 discovery of the wiper. AcidRain was put in on the units after attackers gained entry to the corporate’s non-public community.
Sentinel One, which additionally found AcidRain, mentioned on the time that the sooner wiper had sufficient technical overlaps with malware the US authorities attributed to the Russian authorities in 2018 to make it doubtless that AcidRain and the 2018 malware, often called VPNFilter, had been intently linked to the identical crew of builders. In flip, Sentinel One’s report Thursday noting the similarities between AcidRain and AcidPour, gives proof that AcidPour was additionally created by builders engaged on behalf of the Kremlin.
Technical similarities embrace:
- Use of the identical reboot mechanism
- The precise logic of recursive listing wiping
- The identical IOCTL-based wiping mechanism.
AcidPour additionally shares programming similarities with two different items of malware attributed to Sandworm: Industroyer2, which focused high-voltage electrical substations in Ukraine in 2022, and CaddyWiper, which was used towards numerous targets in Ukraine.
“AcidPour is programmed in C with out counting on statically compiled libraries or imports,” Thursday’s report famous. “Most performance is applied through direct syscalls, many known as by means of the usage of inline meeting and opcodes.” Builders of CaddyWiper and Industroyer used the identical strategy.
Bolstering the speculation that AcidPour was created by the identical Russian risk group behind earlier assaults on Ukraine, a consultant with Ukraine’s State Service of Particular Communications and Info Safety informed Cyberscoop that AcidPour was linked to UAC-0165, a splinter group related to Sandworm (a a lot bigger risk group run by Russia’s army intelligence unit, GRU). Representatives with the State Service of Particular Communications and Info Safety of Ukraine didn’t instantly reply an e mail in search of remark for this publish.
Sandworm has an extended historical past of concentrating on Ukrainian essential infrastructure. Ukrainian officers mentioned final September that UAC-0165 commonly props up pretend hacktivist personas to take credit score for assaults the group carries out.
Sentinel One researchers Juan Andrés Guerrero-Saade and Tom Hegel went on to take a position that AcidPour was used to disrupt a number of Ukrainian telecommunications networks, which have been down since March 13, three days earlier than the researchers found the brand new wiper. They level to statements a persona often called SolntsepekZ made on Telegram that took accountability for hacks that took out Triangulum, a consortium offering phone and Web providers below the Triacom model, and Misto TV.
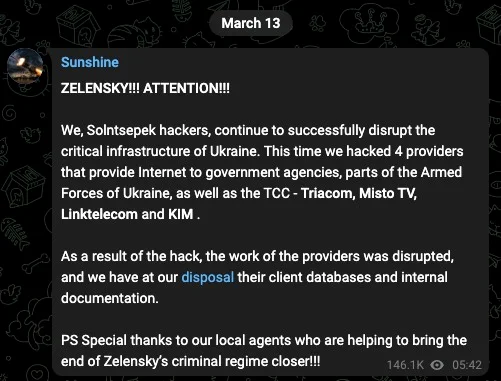
A message a persona often called SolntsepekZ posted to Telegram.
Sentinel One
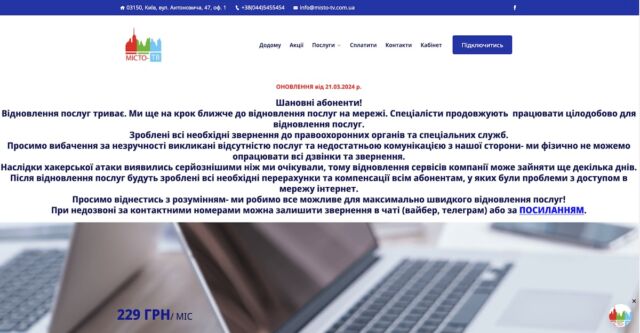
The week-long outage has been confirmed anecdotally and by Community intelligence agency Kentik and content material supply community Cloudflare, with the latter indicating the websites remained inoperable on the time this publish went stay on Ars. As of Thursday afternoon California time, Misto-TV’s web site displayed the next community outage discover:
“At the moment, we can’t affirm that AcidPour was used to disrupt these ISPs,” Guerrero-Saade and Hegel wrote in Thursday’s publish. “The longevity of the disruption suggests a extra advanced assault than a easy DDoS or nuisance disruption. AcidPour, uploaded 3 days after this disruption began, would match the invoice for the requisite toolkit. If that’s the case, it may function one other hyperlink between this hacktivist persona and particular GRU operations.”
The researchers added:
“The transition from AcidRain to AcidPour, with its expanded capabilities, underscores the strategic intent to inflict important operational influence. This development reveals not solely a refinement within the technical capabilities of those risk actors but additionally their calculated strategy to pick out targets that maximize follow-on results, disrupting essential infrastructure and communications.”
