Final yr ESET printed a blogpost about AceCryptor – one of the vital in style and prevalent cryptors-as-a-service (CaaS) working since 2016. For H1 2023 we printed statistics from our telemetry, based on which traits from earlier intervals continued with out drastic adjustments.
Nonetheless, in H2 2023 we registered a major change in how AceCryptor is used. Not solely we’ve seen and blocked over double the assaults in H2 2023 compared with H1 2023, however we additionally observed that Rescoms (also called Remcos) began utilizing AceCryptor, which was not the case beforehand.
The overwhelming majority of AceCryptor-packed Rescoms RAT samples had been used as an preliminary compromise vector in a number of spam campaigns concentrating on European nations together with Poland, Slovakia, Bulgaria, and Serbia.
Key factors of this blogpost:
- AceCryptor continued to offer packing companies to tens of very well-known malware households in H2 2023.
- Despite the fact that well-known by safety merchandise, AceCryptor’s prevalence is just not displaying indications of decline: quite the opposite, the variety of assaults considerably elevated as a result of Rescoms campaigns.
- AceCryptor is a cryptor of selection of menace actors concentrating on particular nations and targets (e.g., firms in a selected nation).
- In H2 2023, ESET detected a number of AceCryptor+Rescoms campaigns in European nations, primarily Poland, Bulgaria, Spain, and Serbia.
- The menace actor behind these campaigns in some circumstances abused compromised accounts to ship spam emails with a view to make them look as credible as attainable.
- The purpose of the spam campaigns was to acquire credentials saved in browsers or electronic mail shoppers, which in case of a profitable compromise would open potentialities for additional assaults.
AceCryptor in H2 2023
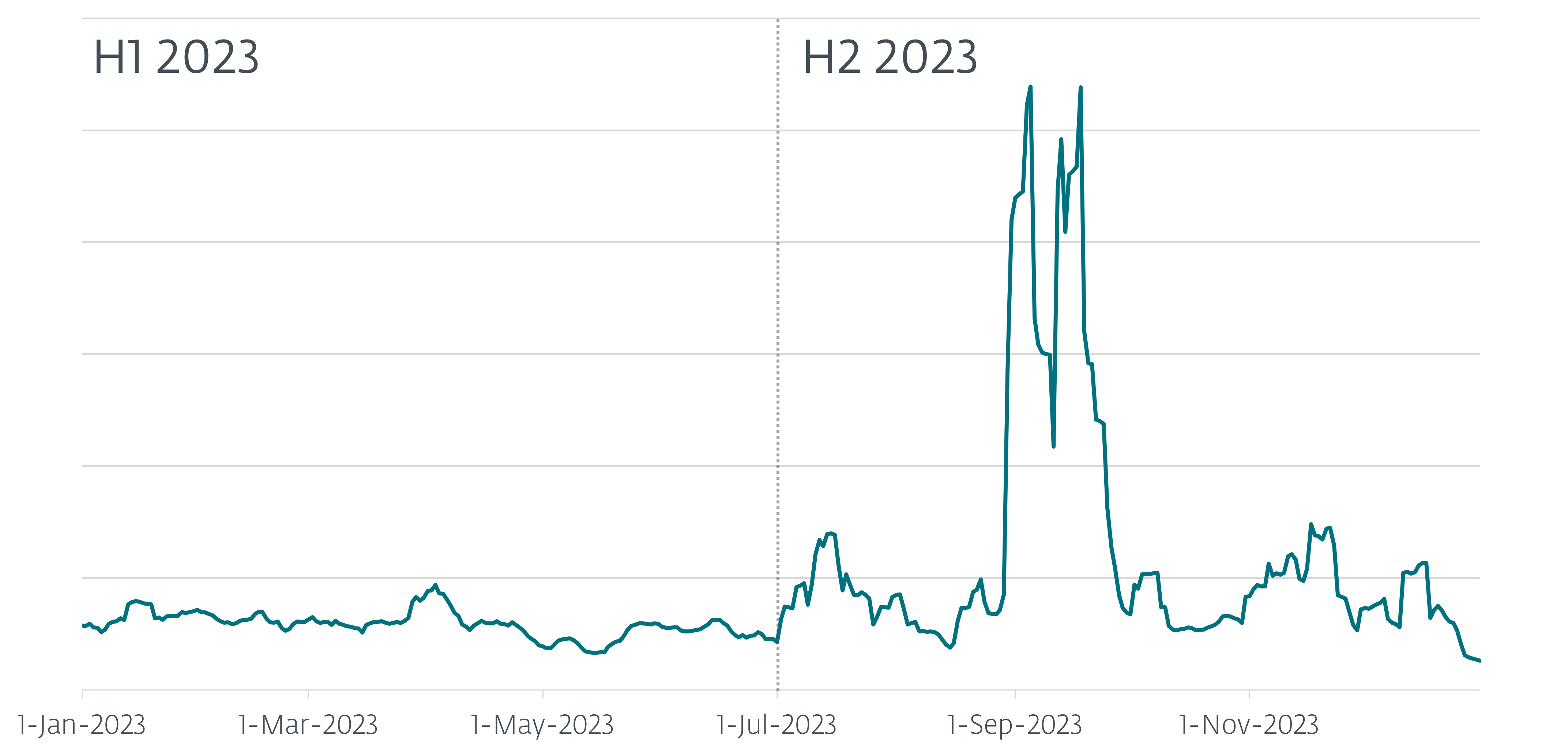
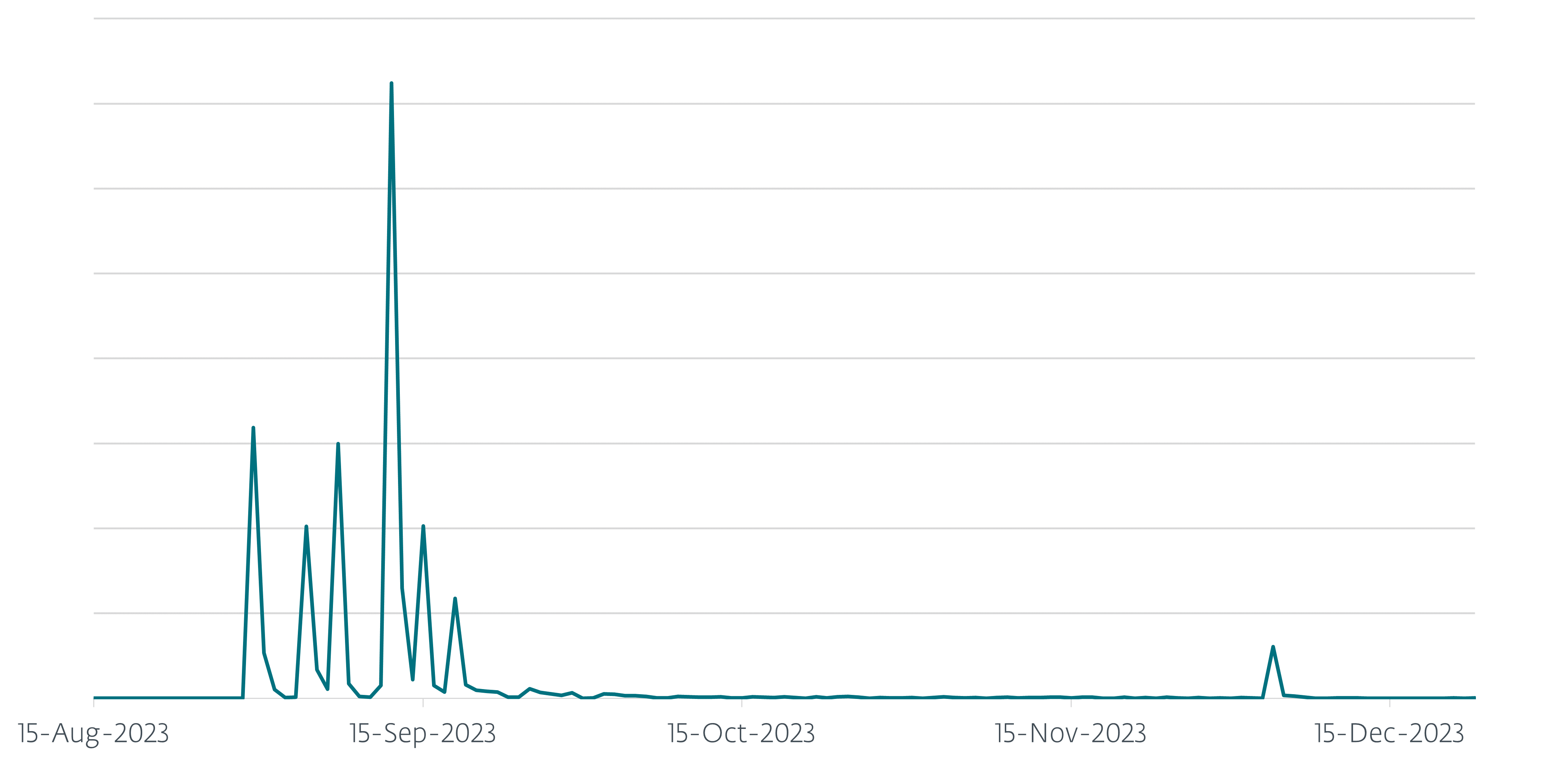
Within the first half of 2023 ESET protected round 13,000 customers from AceCryptor-packed malware. Within the second half of the yr, there was a large improve of AceCryptor-packed malware spreading within the wild, with our detections tripling, leading to over 42,000 protected ESET customers worldwide. As will be noticed in Determine 1, we detected a number of sudden waves of malware spreading. These spikes present a number of spam campaigns focused at European nations the place AceCryptor packed a Rescoms RAT (mentioned extra within the Rescoms campaigns part).
Moreover, after we evaluate the uncooked variety of samples: within the first half of 2023, ESET detected over 23,000 distinctive malicious samples of AceCryptor; within the second half of 2023, we noticed and detected “solely” over 17,000 distinctive samples. Despite the fact that this is likely to be sudden, after a better have a look at the information there’s a affordable clarification. The Rescoms spam campaigns used the identical malicious file(s) in electronic mail campaigns despatched to a larger variety of customers, thus rising the quantity of people that encountered the malware, however nonetheless retaining the variety of totally different recordsdata low. This didn’t occur in earlier intervals as Rescoms was virtually by no means utilized in mixture with AceCryptor. One more reason for the decrement within the variety of distinctive samples is as a result of some in style households apparently stopped (or virtually stopped) utilizing AceCryptor as their go-to CaaS. An instance is Danabot malware which stopped utilizing AceCryptor; additionally, the distinguished RedLine Stealer whose customers stopped utilizing AceCryptor as a lot, based mostly on a larger than 60% lower in AceCryptor samples containing that malware.
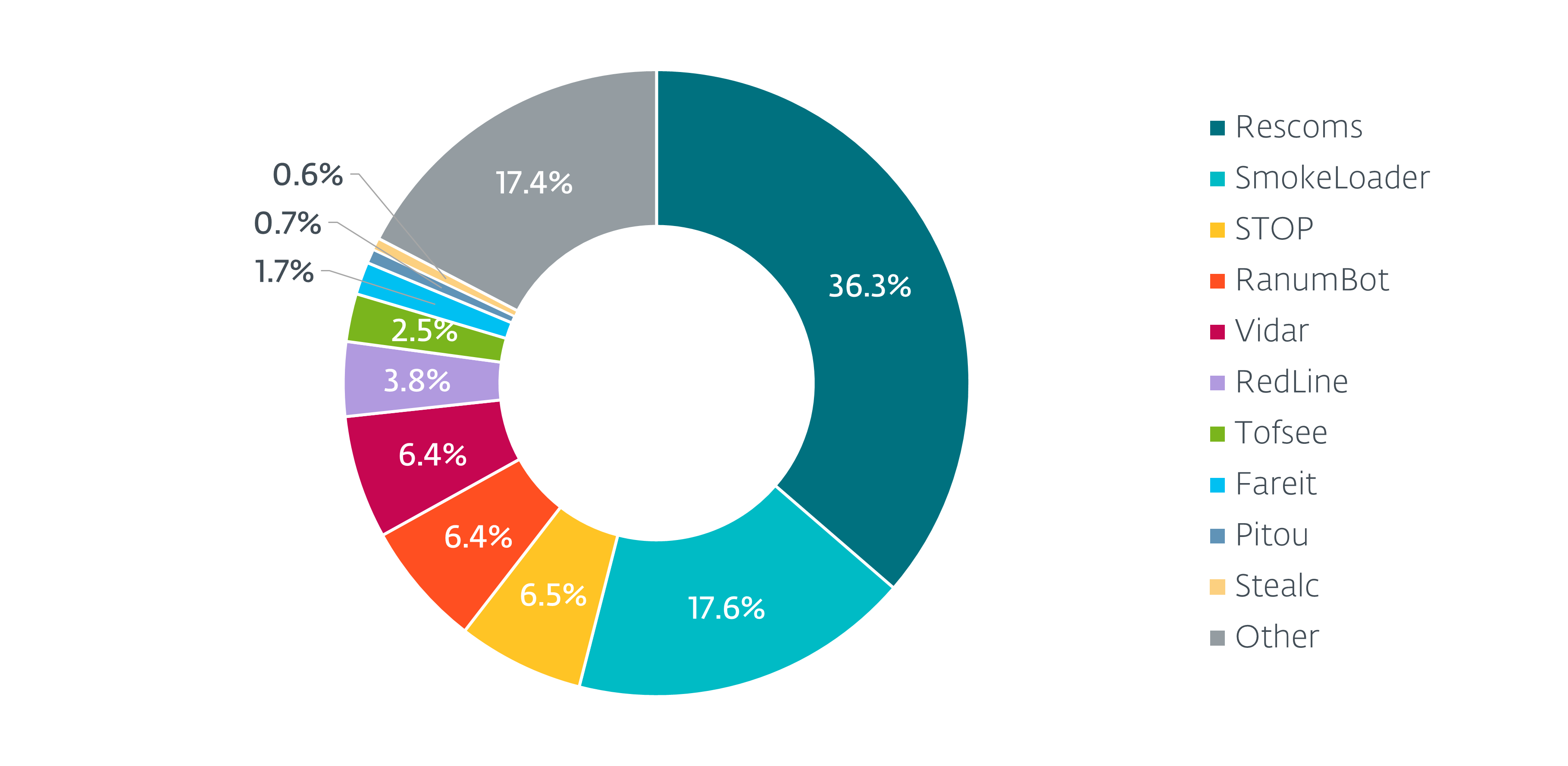
As seen in Determine 2, AceCryptor nonetheless distributes, other than Rescoms, samples from many alternative malware households, equivalent to SmokeLoader, STOP ransomware, and Vidar stealer.
Within the first half of 2023, the nations most affected by malware packed by AceCryptor had been Peru, Mexico, Egypt, and Türkiye, the place Peru, at 4,700, had the best variety of assaults. Rescoms spam campaigns modified these statistics dramatically within the second half of the yr. As will be seen in Determine 3, AceCryptor-packed malware affected principally European nations. By far probably the most affected nation is Poland, the place ESET prevented over 26,000 assaults; that is adopted by Ukraine, Spain, and Serbia. And, it’s price mentioning that in every of these nations ESET merchandise prevented extra assaults than in probably the most affected nation in H1 2023, Peru.
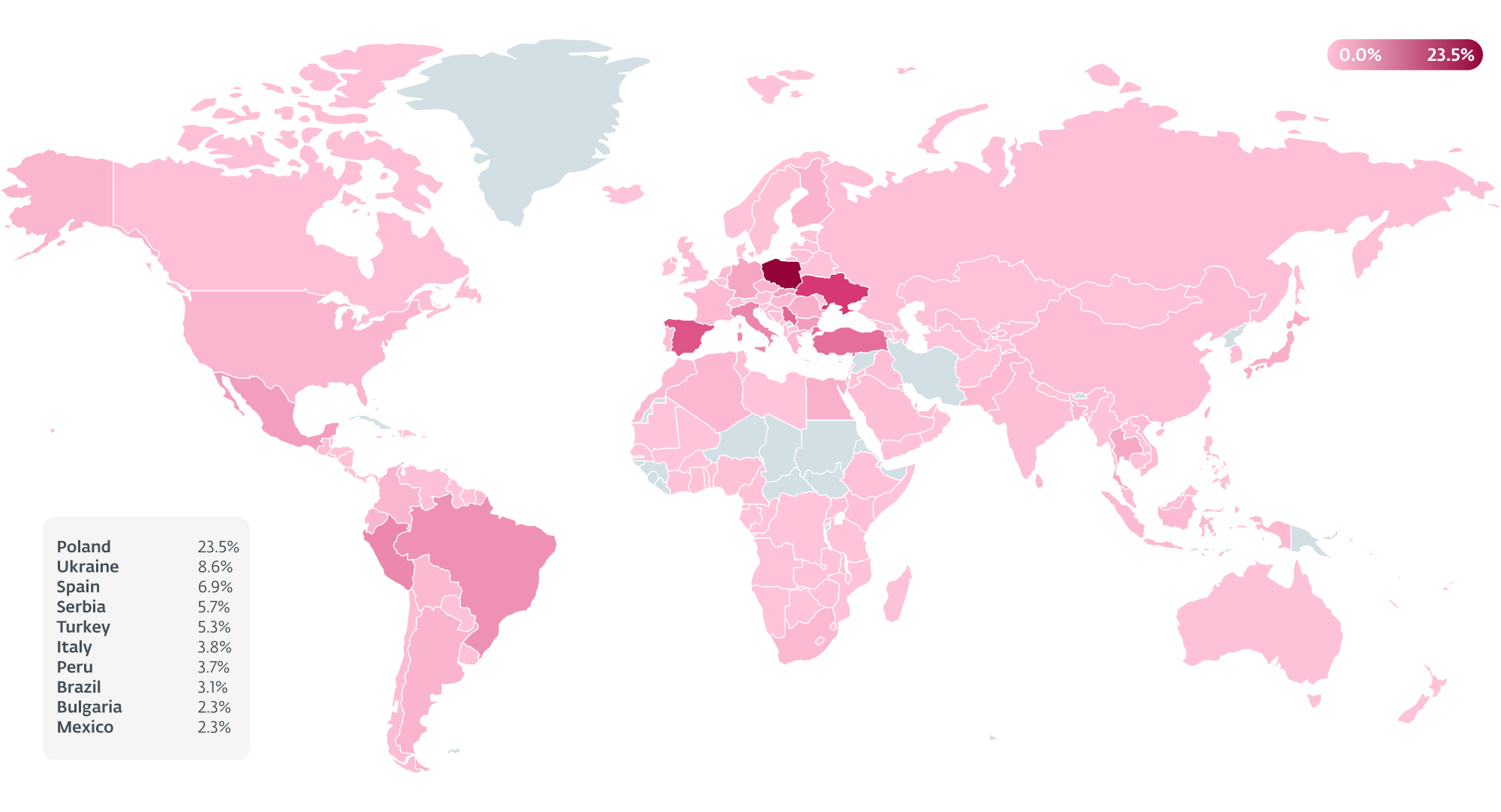
AceCryptor samples that we’ve noticed in H2 usually contained two malware households as their payload: Rescoms and SmokeLoader. A spike in Ukraine was attributable to SmokeLoader. This reality was already talked about by Ukraine’s NSDC. Alternatively, in Poland, Slovakia, Bulgaria, and Serbia the elevated exercise was attributable to AceCryptor containing Rescoms as a ultimate payload.
Rescoms campaigns
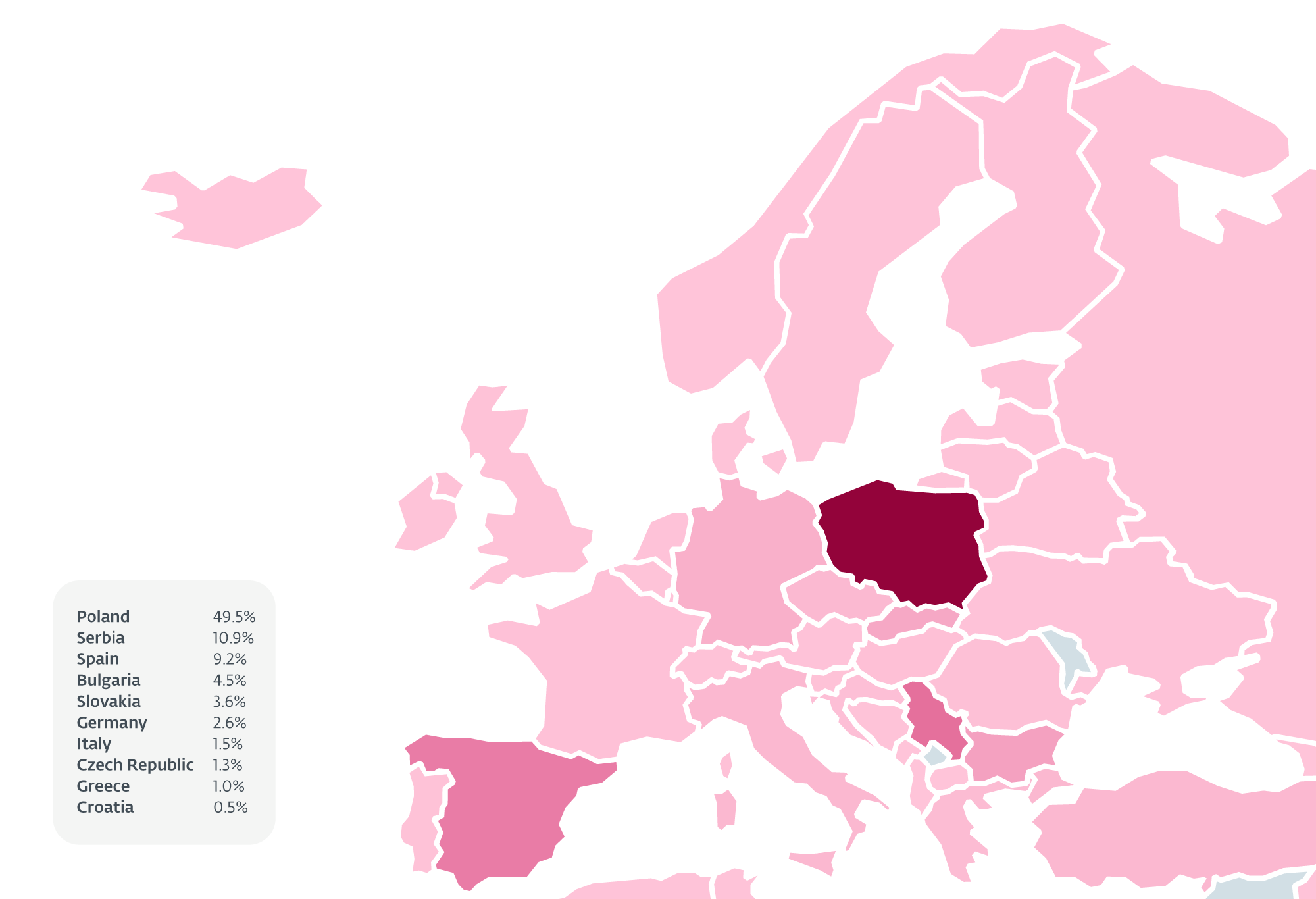
Within the first half of 2023, we noticed in our telemetry fewer than 100 incidents of AceCryptor samples with Rescoms inside. In the course of the second half of the yr, Rescoms grew to become probably the most prevalent malware household packed by AceCryptor, with over 32,000 hits. Over half of those makes an attempt occurred in Poland, adopted by Serbia, Spain, Bulgaria, and Slovakia (Determine 4).
Campaigns in Poland
Because of ESET telemetry we’ve been capable of observe eight vital spam campaigns concentrating on Poland in H2 2023. As will be seen in Determine 5, the vast majority of them occurred in September, however there have been additionally campaigns in August and December.
In whole, ESET registered over 26,000 of those assaults in Poland for this era. All spam campaigns focused companies in Poland and all emails had very related topic traces about B2B affords for the sufferer firms. To look as plausible as attainable, the attackers included the next methods into the spam emails:
- E-mail addresses they had been sending spam emails from imitated domains of different firms. Attackers used a special TLD, modified a letter in an organization title or the phrase order within the case of a multi-word firm title (this system is called typosquatting).
- Essentially the most noteworthy is that a number of campaigns concerned enterprise electronic mail compromise – attackers abused beforehand compromised electronic mail accounts of different firm staff to ship spam emails. On this approach even when the potential sufferer regarded for the standard purple flags, they had been simply not there, and the e-mail regarded as reliable because it may have.
Attackers did their analysis and used present Polish firm names and even present worker/proprietor names and call data when signing these emails. This was finished in order that within the case the place a sufferer tries to Google the sender’s title, the search would achieve success, which could make them open the malicious attachment.
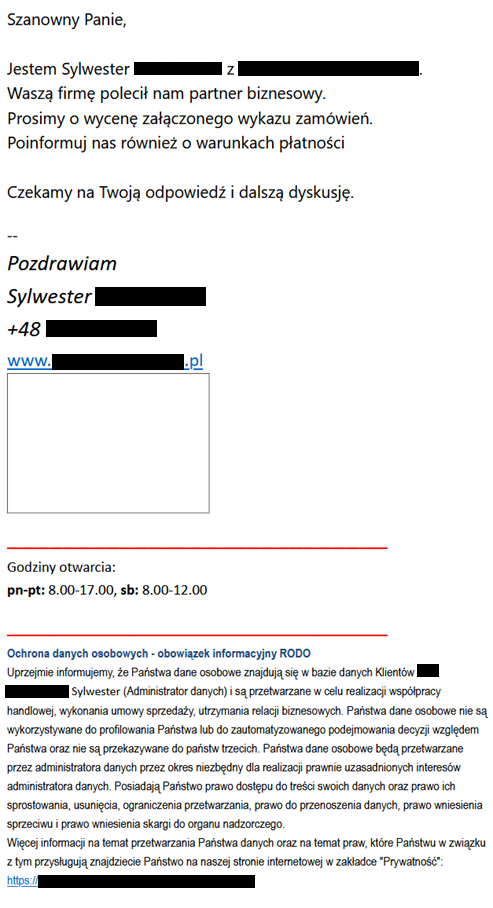
- The content material of spam emails was in some circumstances less complicated however in lots of circumstances (like the instance in Determine 6) fairly elaborate. Particularly these extra elaborate variations must be thought-about harmful as they deviate from the usual sample of generic textual content, which is usually riddled with grammatical errors.
The e-mail proven in Determine 6 accommodates a message adopted by details about the processing of non-public data finished by the alleged sender and the likelihood to “entry the content material of your knowledge and the appropriate to rectify, delete, restrict processing restrictions, proper to knowledge switch, proper to lift an objection, and the appropriate to lodge a criticism with the supervisory authority”. The message itself will be translated thus:
Expensive Sir,
I’m Sylwester [redacted] from [redacted]. Your organization was really useful to us by a enterprise accomplice. Please quote the connected order record. Please additionally inform us in regards to the cost phrases.
We look ahead to your response and additional dialogue.
—
Finest Regards,
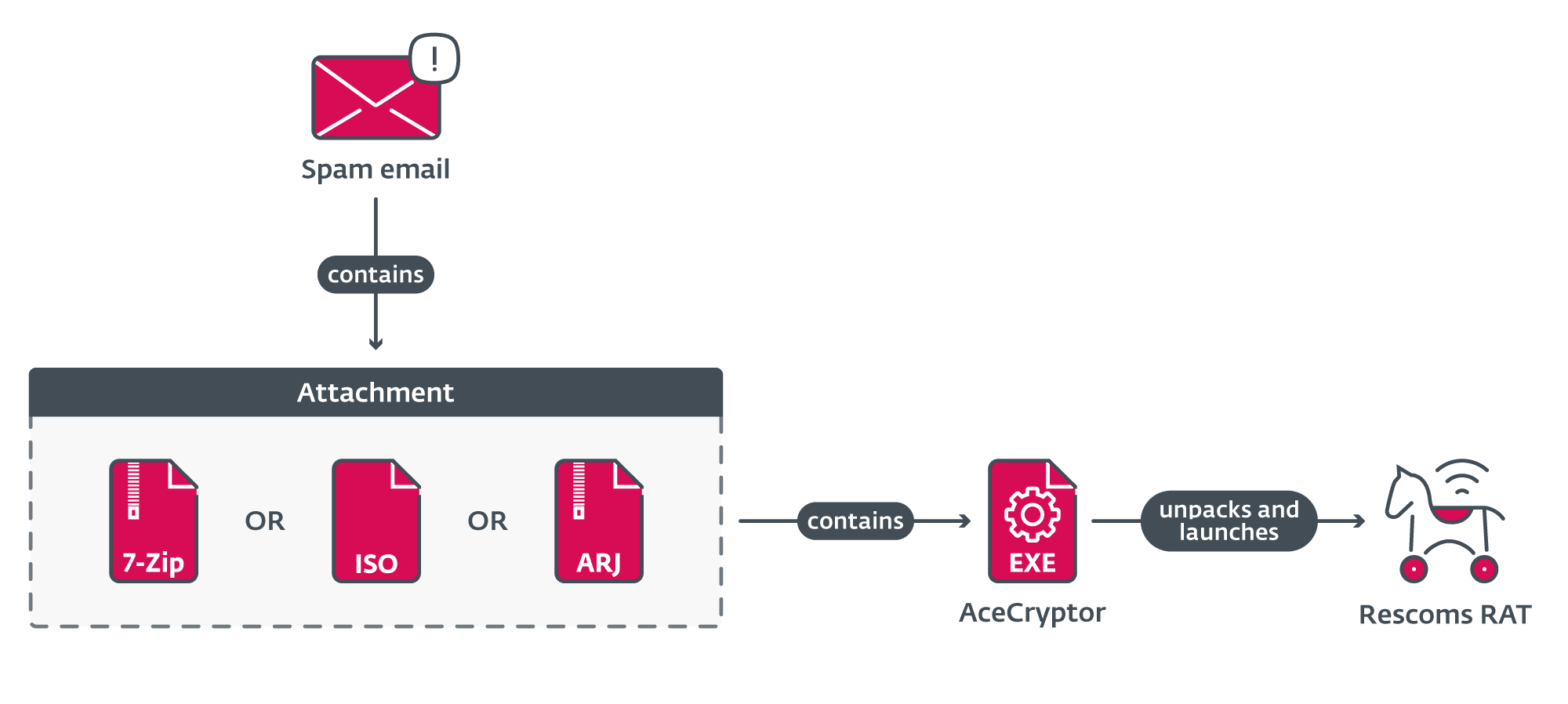
Attachments in all campaigns regarded fairly related (Determine 7). Emails contained an connected archive or ISO file named provide/inquiry (in fact in Polish), in some circumstances additionally accompanied with an order quantity. That file contained an AceCryptor executable that unpacked and launched Rescoms.
Based mostly on the habits of the malware, we assume that the purpose of those campaigns was to acquire electronic mail and browser credentials, and thus acquire preliminary entry to the focused firms. Whereas it’s unknown whether or not the credentials had been gathered for the group that carried out these assaults or if these stolen credentials could be later bought to different menace actors, it’s sure that profitable compromise opens the likelihood for additional assaults, particularly from, at present in style, ransomware assaults.
You will need to state that Rescoms RAT will be purchased; thus many menace actors use it of their operations. These campaigns should not solely related by goal similarity, attachment construction, electronic mail textual content, or methods and methods used to deceive potential victims, but additionally by some much less apparent properties. Within the malware itself, we had been capable of finding artifacts (e.g., the license ID for Rescoms) that tie these campaigns collectively, revealing that many of those assaults had been carried out by one menace actor.
Campaigns in Slovakia, Bulgaria, and Serbia
Throughout the identical time intervals because the campaigns in Poland, ESET telemetry additionally registered ongoing campaigns in Slovakia, Bulgaria, and Serbia. These campaigns additionally primarily focused native firms and we will even discover artifacts within the malware itself tying these campaigns to the identical menace actor that carried out the campaigns in Poland. The one vital factor that modified was, in fact, the language used within the spam emails to be appropriate for these particular nations.
Campaigns in Spain
Other than beforehand talked about campaigns, Spain additionally skilled a surge of spam emails with Rescoms as the ultimate payload. Despite the fact that we will affirm that at the very least one of many campaigns was carried out by the identical menace actor as in these earlier circumstances, different campaigns adopted a considerably totally different sample. Moreover, even artifacts that had been the identical in earlier circumstances differed in these and, due to that, we can’t conclude that the campaigns in Spain originated from the identical place.
Conclusion
In the course of the second half of 2023 we detected a shift within the utilization of AceCryptor – a well-liked cryptor utilized by a number of menace actors to pack many malware households. Despite the fact that the prevalence of some malware households like RedLine Stealer dropped, different menace actors began utilizing it or used it much more for his or her actions and AceCryptor continues to be going robust.In these campaigns AceCryptor was used to focus on a number of European nations, and to extract data or acquire preliminary entry to a number of firms. Malware in these assaults was distributed in spam emails, which had been in some circumstances fairly convincing; generally the spam was even despatched from reliable, however abused electronic mail accounts. As a result of opening attachments from such emails can have extreme penalties for you or your organization, we advise that you simply bear in mind about what you might be opening and use dependable endpoint safety software program capable of detect the malware.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis affords personal APT intelligence experiences and knowledge feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
A complete record of Indicators of Compromise (IoCs) will be present in our GitHub repository.
Information
|
SHA-1 |
Filename |
Detection |
Description |
|
7D99E7AD21B54F07E857 |
PR18213.iso |
Win32/Kryptik.HVOB |
Malicious attachment from spam marketing campaign carried out in Serbia throughout December 2023. |
|
7DB6780A1E09AEC6146E |
zapytanie.7z |
Win32/Kryptik.HUNX |
Malicious attachment from spam marketing campaign carried out in Poland throughout September 2023. |
|
7ED3EFDA8FC446182792 |
20230904104100858.7z |
Win32/Kryptik.HUMX |
Malicious attachment from spam marketing campaign carried out in Poland and Bulgaria throughout September 2023. |
|
9A6C731E96572399B236 |
20230904114635180.iso |
Win32/Kryptik.HUMX |
Malicious attachment from spam marketing campaign carried out in Serbia throughout September 2023. |
|
57E4EB244F3450854E5B |
SA092300102.iso |
Win32/Kryptik.HUPK |
Malicious attachment from spam marketing campaign carried out in Bulgaria throughout September 2023. |
|
178C054C5370E0DC9DF8 |
zamowienie_135200.7z |
Win32/Kryptik.HUMI |
Malicious attachment from spam marketing campaign carried out in Poland throughout August 2023. |
|
394CFA4150E7D47BBDA1 |
PRV23_8401.iso |
Win32/Kryptik.HUMF |
Malicious attachment from spam marketing campaign carried out in Serbia throughout August 2023. |
|
3734BC2D9C321604FEA1 |
BP_50C55_20230 |
Win32/Kryptik.HUMF |
Malicious attachment from spam marketing campaign carried out in Bulgaria throughout August 2023. |
|
71076BD712C2E3BC8CA5 |
20_J402_MRO_EMS |
Win32/Rescoms.B |
Malicious attachment from spam marketing campaign carried out in Slovakia throughout August 2023. |
|
667133FEBA54801B0881 |
7360_37763.iso |
Win32/Rescoms.B |
Malicious attachment from spam marketing campaign carried out in Bulgaria throughout December 2023. |
|
AF021E767E68F6CE1D20 |
zapytanie ofertowe.7z |
Win32/Kryptik.HUQF |
Malicious attachment from spam marketing campaign carried out in Poland throughout September 2023. |
|
BB6A9FB0C5DA4972EFAB |
129550.7z |
Win32/Kryptik.HUNC |
Malicious attachment from spam marketing campaign carried out in Poland throughout September 2023. |
|
D2FF84892F3A4E4436BE |
Zamowienie_ andre.7z |
Win32/Kryptik.HUOZ |
Malicious attachment from spam marketing campaign carried out in Poland throughout September 2023. |
|
DB87AA88F358D9517EEB |
20030703_S1002.iso |
Win32/Kryptik.HUNI |
Malicious attachment from spam marketing campaign carried out in Serbia throughout September 2023. |
|
EF2106A0A40BB5C1A74A |
Zamowienie_830.iso |
Win32/Kryptik.HVOB |
Malicious attachment from spam marketing campaign carried out in Poland throughout December 2023. |
|
FAD97EC6447A699179B0 |
lista zamówień i szczegółowe zdjęcia.arj |
Win32/Kryptik.HUPK |
Malicious attachment from spam marketing campaign carried out in Poland throughout September 2023. |
|
FB8F64D2FEC152D2D135 |
Pedido.iso |
Win32/Kryptik.HUMF |
Malicious attachment from spam marketing campaign carried out in Spain throughout August 2023. |
MITRE ATT&CK methods
This desk was constructed utilizing model 14 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Title |
Description |
|
Reconnaissance |
Collect Sufferer Identification Info: E-mail Addresses |
E-mail addresses and call data (both purchased or gathered from publicly out there sources) had been utilized in phishing campaigns to focus on firms throughout a number of nations. |
|
|
Useful resource Improvement |
Compromise Accounts: E-mail Accounts |
Attackers used compromised electronic mail accounts to ship phishing emails in spam campaigns to extend spam electronic mail’s credibility. |
|
|
Get hold of Capabilities: Malware |
Attackers purchased and used AceCryptor and Rescoms for phishing campaigns. |
||
|
Preliminary Entry |
Phishing |
Attackers used phishing messages with malicious attachments to compromise computer systems and steal data from firms in a number of European nations. |
|
|
Phishing: Spearphishing Attachment |
Attackers used spearphishing messages to compromise computer systems and steal data from firms in a number of European nations. |
||
|
Execution |
Person Execution: Malicious File |
Attackers relied on customers opening and launching malicious recordsdata with malware packed by AceCryptor. |
|
|
Credential Entry |
Credentials from Password Shops: Credentials from Internet Browsers |
Attackers tried to steal credential data from browsers and electronic mail shoppers. |

