The content material of this submit is solely the accountability of the writer. AT&T doesn’t undertake or endorse any of the views, positions, or info offered by the writer on this article.
Past its elementary port scanning capabilities, Nmap affords a set of superior methods designed to uncover vulnerabilities, bypass safety measures, and collect invaluable insights about goal programs. Let’s check out these methods:
1. Vulnerability Detection
Syntax: nmap -sV –script=vulners
Nmap’s vulnerability detection characteristic, facilitated by the ‘vulners’ script, allows customers to establish outdated companies inclined to recognized safety vulnerabilities. By querying a complete vulnerability database, Nmap gives invaluable insights into potential weaknesses inside goal programs.
2. Idle Scanning
Syntax: nmap -sI
Idle scanning represents a stealthy strategy to port scanning, leveraging a “zombie” host to obfuscate the origin of scan requests. By monitoring modifications within the zombie host’s IP identification quantity (IP ID) in response to packets despatched to the goal, Nmap infers the state of the goal’s ports with out direct interplay.
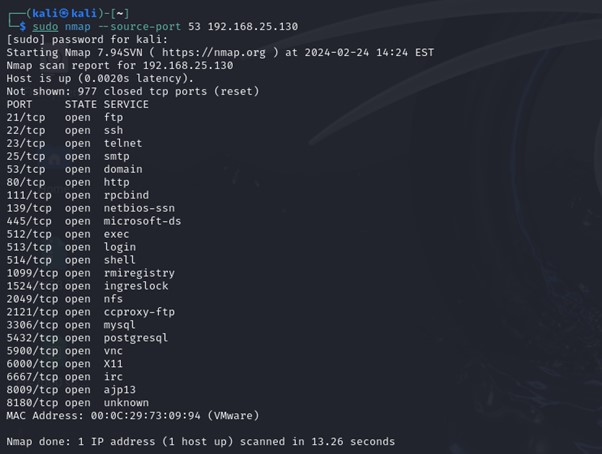
3. Firewall Testing (Supply Port Spoofing)
Syntax: nmap –source-port
This system entails testing firewall guidelines by sending packets with uncommon supply ports. By spoofing the supply port, safety professionals can consider the effectiveness of firewall configurations and establish potential weaknesses in community defenses.
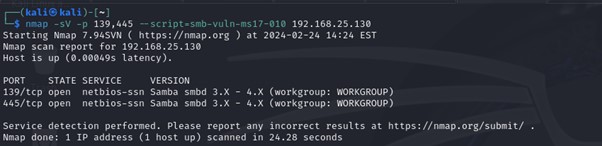
4. Service-Particular Probes (SMB Instance)
Syntax: nmap -sV -p 139,445 –script=smb-vuln*
Nmap’s service-specific probes allow detailed examination of companies, such because the Server Message Block (SMB) protocol generally utilized in Home windows environments. By leveraging specialised scripts, analysts can establish vulnerabilities and assess the safety posture of goal programs.
5. Net Software Scanning (HTTP title seize)
Syntax: nmap -sV -p 80 –script=http-title
Net software scanning with Nmap permits customers to collect details about internet servers, probably aiding in vulnerability identification and exploitation.
By analyzing HTTP response headers, Nmap extracts invaluable insights about goal internet purposes and server configurations.
Nmap Scripting Engine:
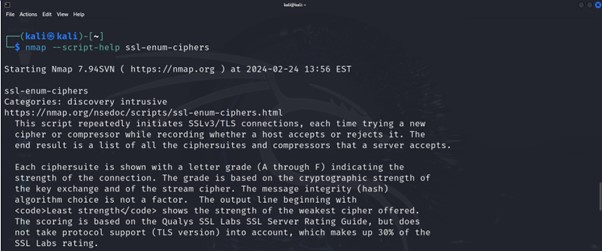
One of many standout options of Nmap is its strong scripting engine (NSE), which permits customers to increase the software’s performance by customized scripts and plugins. NSE scripts allow customers to automate duties, carry out specialised scans, collect further info, and even exploit vulnerabilities in goal programs.
nmap –script-help scriptname Exhibits assist about scripts. For every script matching the given specification, Nmap prints the script title, its classes, and its description. The specs are the identical as these accepted by –script; so, for instance if you would like assist concerning the ssl-enum-ciphers script, you’d run nmap –script-help ssl-enum-ciphers
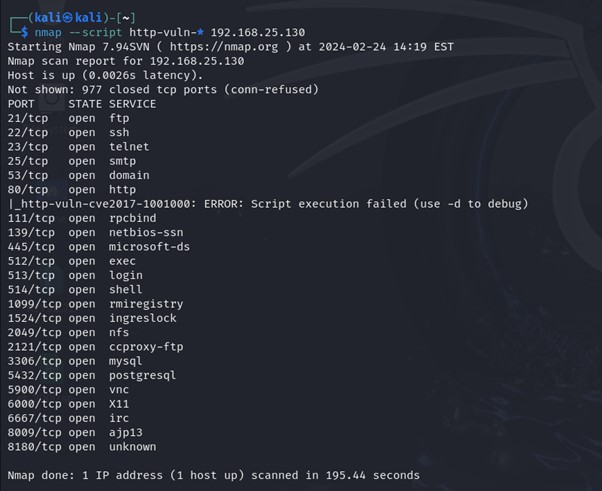
Customers can leverage current NSE scripts or develop customized scripts tailor-made to their particular necessities. For instance, to carry out an online vulnerability scan utilizing Nmap’s NSE, one would possibly use the next command:
Syntax: nmap –script http-vuln-* target_ip
Nmap’s superior methods signify a complicated toolkit for community reconnaissance and vulnerability evaluation. From uncovering outdated companies to bypassing safety measures, these methods empower safety professionals to evaluate and shield community infrastructures successfully. Nevertheless, it’s crucial to make use of these methods responsibly and ethically, guaranteeing compliance with authorized and moral pointers. By mastering Nmap’s superior capabilities, safety professionals can improve their skill to detect and mitigate potential threats, thereby strengthening the general safety posture of networked environments. Because the cybersecurity panorama continues to evolve, Nmap stays a steadfast companion within the ongoing battle towards rising threats and vulnerabilities.