An lively Android malware marketing campaign dubbed eXotic Go to has been primarily concentrating on customers in South Asia, notably these in India and Pakistan, with malware distributed by way of devoted web sites and Google Play Retailer.
Slovak cybersecurity agency mentioned the exercise, ongoing since November 2021, shouldn’t be linked to any recognized risk actor or group. It is monitoring the group behind the operation beneath the title Digital Invaders.
“Downloaded apps present respectable performance, but additionally embrace code from the open-source Android XploitSPY RAT,” ESET safety researcher Lukáš Štefanko mentioned in a technical report launched at the moment.
The marketing campaign is claimed to be extremely focused in nature, with the apps obtainable on Google Play having negligible variety of installs starting from zero to 45. The apps have since been taken down.
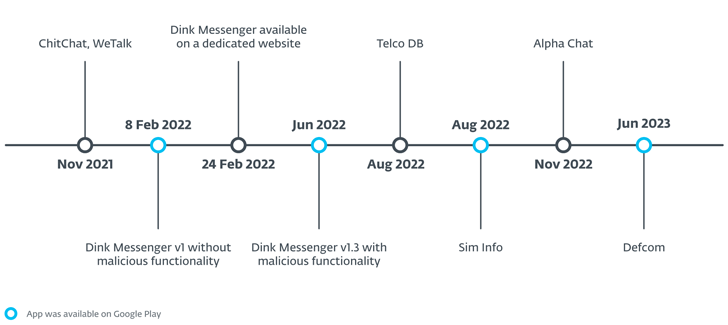
The fake-but-functional apps primarily masquerade as messaging companies like Alpha Chat, ChitChat, Defcom, Dink Messenger, Sign Lite, TalkU, WeTalk, Wicker Messenger, and Zaangi Chat. Roughly 380 victims are mentioned to have downloaded the apps and created accounts to make use of them for messaging functions.
Additionally employed as a part of eXotic Go to are apps resembling Sim Information and Telco DB, each of which declare to offer particulars about SIM homeowners just by coming into a Pakistan-based cellphone quantity. Different purposes move off as a meals ordering service in Pakistan in addition to a respectable Indian hospital referred to as Specialist Hospital (now rebranded as Trilife Hospital).
XploitSPY, uploaded to GitHub as early as April 2020 by a consumer named RaoMK, is related to an Indian cyber safety options firm referred to as XploitWizer. It has additionally been described as a fork of one other open-source Android trojan referred to as L3MON, which, in flip, attracts inspiration from AhMyth.
It comes with a large gamut of options that enables it to collect delicate knowledge from contaminated gadgets, resembling GPS places, microphone recordings, contacts, SMS messages, name logs, and clipboard content material; extract notification particulars from apps like WhatsApp, Fb, Instagram, and Gmail; obtain and add information; view put in apps; and queue instructions.
On prime of that, the malicious apps are designed to take footage and enumerate information in a number of directories associated to screenshots, WhatApp, WhatsApp Enterprise, Telegram, and an unofficial WhatsApp mod generally known as GBWhatsApp.
“All through the years, these risk actors have custom-made their malicious code by including obfuscation, emulator detection, hiding of [command-and-control] addresses, and use of a local library,” Štefanko mentioned.
The primary goal of the native library (“defcome-lib.so”) is to maintain the C2 server info encoded and hidden from static evaluation instruments. If an emulator is detected, the app makes use of a faux C2 server to evade detection.
Among the apps have been propagated by web sites particularly created for this goal (“chitchat.ngrok[.]io”) that present a hyperlink to an Android bundle file (“ChitChat.apk”) hosted on GitHub. It is presently not clear how victims are directed to those apps.
“Distribution began on devoted web sites after which even moved to the official Google Play retailer,” Štefanko concluded. “The aim of the marketing campaign is espionage and doubtless is concentrating on victims in Pakistan and India.”