A risk actor tracked as TA547 has focused dozens of German organizations with an info stealer referred to as Rhadamanthys as a part of an invoice-themed phishing marketing campaign.
“That is the primary time researchers noticed TA547 use Rhadamanthys, an info stealer that’s utilized by a number of cybercriminal risk actors,” Proofpoint stated. “Moreover, the actor appeared to make use of a PowerShell script that researchers suspect was generated by a big language mannequin (LLM).”
TA547 is a prolific, financially motivated risk actor that is identified to be lively since not less than November 2017, utilizing e mail phishing lures to ship a wide range of Android and Home windows malware similar to ZLoader, Gootkit, DanaBot, Ursnif, and even Adhubllka ransomware.
In recent times, the group has developed into an preliminary entry dealer (IAB) for ransomware assaults. It has additionally been noticed using geofencing methods to limit payloads to particular areas.
The e-mail messages noticed as a part of the newest marketing campaign impersonate the German firm Metro AG and comprise a password-protected ZIP file containing a ZIP archive that, when opened, initiates the execution of a distant PowerShell script to launch the Rhadamanthys stealer instantly in reminiscence.
Apparently, the PowerShell script used to load Rhadamanthys contains “grammatically right and hyper particular feedback” for every instruction in this system, elevating the likelihood that it could have been generated (or rewritten) utilizing an LLM.
The alternate speculation is that TA547 copied the script from one other supply that had used generative AI expertise to create it.
“This marketing campaign represents an instance of some method shifts from TA547 together with using compressed LNKs and beforehand unobserved Rhadamanthys stealer,” Proofpoint stated. “It additionally offers perception into how risk actors are leveraging doubtless LLM-generated content material in malware campaigns.”
The event comes as phishing campaigns have additionally been banking on unusual ways to facilitate credential-harvesting assaults. In these emails, recipients are notified of a voice message and are directed to click on on a hyperlink to entry it.
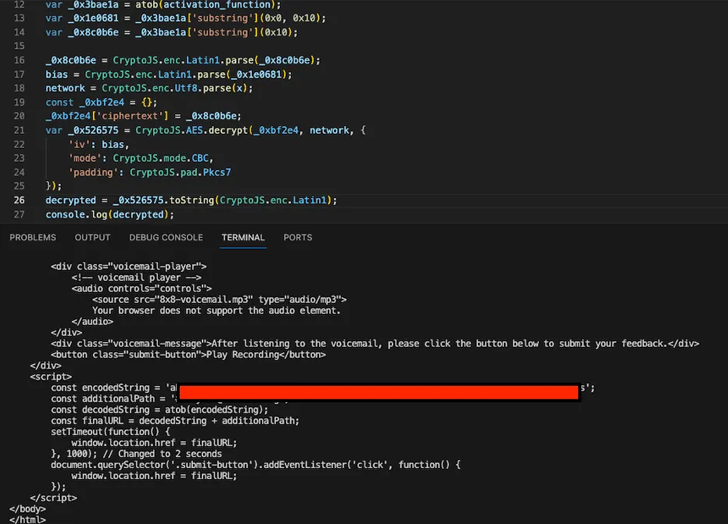
The payload retrieved from the URL is closely obfuscated HTML content material that runs JavaScript code embedded inside an SVG picture when the web page is rendered on the goal system.
Current throughout the SVG knowledge is “encrypted knowledge containing a second stage web page prompting the goal to enter their credentials to entry the voice message,” Binary Protection stated, including the web page is encrypted utilizing CryptoJS.
Different email-based assaults have paved the best way for Agent Tesla, which has emerged as a horny choice for risk actors attributable to it “being an reasonably priced malware service with a number of capabilities to exfiltrate and steal customers’ knowledge,” based on Cofense.
Social engineering campaigns have additionally taken the type of malicious adverts served on serps like Google that lure unsuspecting customers into downloading bogus installers for in style software program like PuTTY, FileZilla, and Room Planner to in the end deploy Nitrogen and IDAT Loader.
The an infection chain related to IDAT Loader is noteworthy for the truth that the MSIX installer is used to launch a PowerShell script that, in flip, contacts a Telegram bot to fetch a second PowerShell script hosted on the bot.
This PowerShell script then acts as a conduit to ship one other PowerShell script that is used to bypass Home windows Antimalware Scan Interface (AMSI) protections in addition to set off the execution of the loader, which subsequently proceeds to load the SectopRAT trojan.
“Endpoints might be protected against malicious adverts by way of group insurance policies that prohibit site visitors coming from the principle and lesser identified advert networks,” Jérôme Segura, principal risk researcher at Malwarebytes, stated.