WordPress safety scanner WPScan’s 2024 WordPress vulnerability report calls consideration to WordPress vulnerability tendencies and suggests the sorts of issues web site publishers (and SEOs) needs to be searching for.
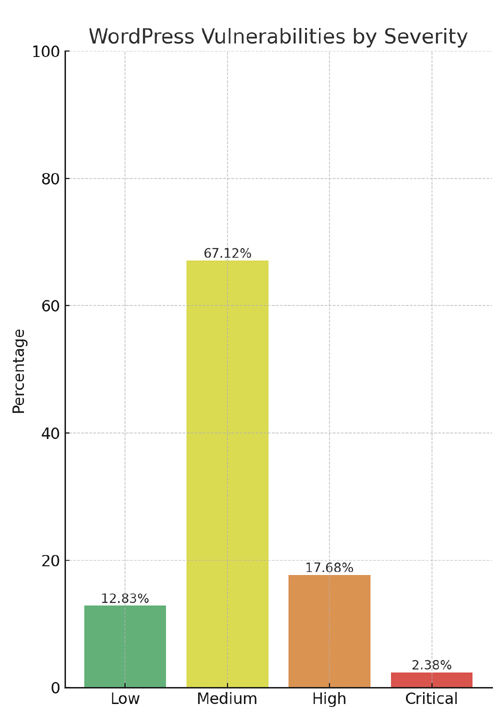
A few of the key findings from the report have been that simply over 20% of vulnerabilities have been rated as excessive or vital stage threats, with medium severity threats, at 67% of reported vulnerabilities, making up the bulk. Many regard medium stage vulnerabilities as if they’re low-level threats and that’s a mistake as a result of they’re not low stage and needs to be considered deserving consideration.
The report doesn’t blame customers for the malware and web site vulnerabilities. However errors made by publishers can amplify the success of hackers exploiting vulnerabilities.
The WPScan report suggested:
“Whereas severity doesn’t translate on to the chance of exploitation, it’s an vital guideline for web site homeowners to make an informed resolution about when to disable or replace the extension.”
WordPress Vulnerability Severity Distribution
Vital stage vulnerabilities, the best stage of risk, represented solely 2.38% of vulnerabilities, which is basically excellent news for WordPress publishers. But as talked about earlier, when mixed with the odds of excessive stage threats (17.68%) the quantity or regarding vulnerabilities rises to nearly 20%.
Listed below are the odds by severity rankings:
- Vital 2.38%
- Low 12.83%
- Excessive 17.68%
- Medium 67.12%
Authenticated Versus Unauthenticated
Authenticated vulnerabilities are people who require an attacker to first attain consumer credentials and their accompanying permission ranges with the intention to exploit a selected vulnerability. Exploits that require subscriber-level authentication are essentially the most exploitable of the authenticated exploits and people who require administrator stage entry current the least danger (though not all the time a low danger for a wide range of causes).
Unauthenticated assaults are typically the simplest to take advantage of as a result of anybody can launch an assault with out having to first purchase a consumer credential.
The WPScan vulnerability report discovered that about 22% of reported vulnerabilities required subscriber stage or no authentication in any respect, representing essentially the most exploitable vulnerabilities. On the opposite finish of the size of the exploitability are vulnerabilities requiring admin permission ranges representing a complete of 30.71% of reported vulnerabilities.
Nulled Software program And Weak Passwords
Weak passwords and nulled plugins have been two frequent causes for malware discovered by way of the Jetpack Scan. Nulled software program are pirated plugins that had their capacity to validate in the event that they have been paid for blocked. These plugins tended to have backdoors that enabled infections with malware. Weak passwords will be guessed by way of brute-force assaults.
The WPScan report explains:
“Authentication bypass assaults may contain a wide range of methods, reminiscent of exploiting weaknesses in weak passwords, guessing credentials, utilizing brute drive assaults to guess passwords, utilizing social engineering techniques reminiscent of phishing or pretexting, utilizing privilege escalation methods reminiscent of exploiting recognized vulnerabilities in software program and {hardware} gadgets or attempting default account logins.”
Permission Ranges Required For Exploits
Vulnerabilities requiring administrator stage credentials represented the best share of exploits, adopted by Cross Web site Request Forgery (CSRF) with 24.74% of vulnerabilities. That is fascinating as a result of CSRF is an assault that makes use of social engineering to get a sufferer to click on a hyperlink from which the consumer’s permission ranges are acquired. It is a mistake that WordPress publishers ought to concentrate on as a result of all it takes is for an admin stage consumer to observe a hyperlink which then allows the hacker to imagine admin stage privileges to the WordPress web site.
The next is the odds of exploits ordered by roles essential to launch an assault.
Ascending Order Of Person Roles For Vulnerabilities
- Creator 2.19%
- Subscriber 10.4%
- Unauthenticated 12.35%
- Contributor 19.62%
- CSRF 24.74%
- Admin 30.71%
Most Frequent Vulnerability Sorts Requiring Minimal Authentication
Damaged Entry Management within the context of WordPress refers to a safety failure that may permit an attacker with out crucial permission credentials to achieve entry to larger credential permissions.
Within the part of the report that appears on the occurrences and vulnerabilities underlying unauthenticated or subscriber stage vulnerabilities reported (Prevalence vs Vulnerability on Unauthenticated or Subscriber+ stories), WPScan breaks down the odds for every vulnerability sort that’s commonest for exploits which are the simplest to launch (as a result of they require minimal to no consumer credential authentication).
The WPScan risk report famous that Damaged Entry Management represents a whopping 84.99% adopted by SQL injection (20.64%).
The Open Worldwide Software Safety Venture (OWASP) defines Damaged Entry Management as:
“Entry management, generally known as authorization, is how an online software grants entry to content material and features to some customers and never others. These checks are carried out after authentication, and govern what ‘approved’ customers are allowed to do.
Entry management appears like a easy drawback however is insidiously tough to implement accurately. An internet software’s entry management mannequin is carefully tied to the content material and features that the location gives. As well as, the customers could fall into quite a few teams or roles with totally different talents or privileges.”
SQL injection, at 20.64% represents the second most prevalent sort of vulnerability, which WPScan known as each “excessive severity and danger” within the context of vulnerabilities requiring minimal authentication ranges as a result of attackers can entry and/or tamper with the database which is the guts of each WordPress web site.
These are the odds:
- Damaged Entry Management 84.99%
- SQL Injection 20.64%
- Cross-Web site Scripting 9.4%
- Unauthenticated Arbitrary File Add 5.28%
- Delicate Information Disclosure 4.59%
- Insecure Direct Object Reference (IDOR) 3.67%
- Distant Code Execution 2.52%
- Different 14.45%
Vulnerabilities In The WordPress Core Itself
The overwhelming majority of vulnerability points have been reported in third-party plugins and themes. Nonetheless, there have been in 2023 a complete of 13 vulnerabilities reported within the WordPress core itself. Out of the 13 vulnerabilities solely one in all them was rated as a excessive severity risk, which is the second highest stage, with Vital being the best stage vulnerability risk, a score scoring system maintained by the Frequent Vulnerability Scoring System (CVSS).
The WordPress core platform itself is held to the best requirements and advantages from a worldwide neighborhood that’s vigilant in discovering and patching vulnerabilities.
Web site Safety Ought to Be Thought of As Technical search engine optimization
Web site audits don’t usually cowl web site safety however for my part each accountable audit ought to at the very least speak about safety headers. As I’ve been saying for years, web site safety rapidly turns into an search engine optimization concern as soon as a web site’s rating begin disappearing from the search engine outcomes pages (SERPs) attributable to being compromised by a vulnerability. That’s why it’s vital to be proactive about web site safety.
In line with the WPScan report, the principle level of entry for hacked web sites have been leaked credentials and weak passwords. Making certain robust password requirements plus two-factor authentication is a crucial a part of each web site’s safety stance.
Utilizing safety headers is one other approach to assist defend in opposition to Cross-Web site Scripting and different kinds of vulnerabilities.
Lastly, a WordPress firewall and web site hardening are additionally helpful proactive approaches to web site safety. I as soon as added a discussion board to a model new web site I created and it was instantly beneath assault inside minutes. Imagine it or not, nearly each web site worldwide is beneath assault 24 hours a day by bots scanning for vulnerabilities.
Learn the WPScan Report:
WPScan 2024 Web site Menace Report
Featured Picture by Shutterstock/Ljupco Smokovski
