Expertise, analysis, and authorities sectors within the Asia-Pacific area have been focused by a menace actor known as BlackTech as a part of a latest cyber assault wave.
The intrusions pave the best way for an up to date model of modular backdoor dubbed Waterbear in addition to its enhanced successor known as Deuterbear.
“Waterbear is understood for its complexity, because it makes use of numerous evasion mechanisms to attenuate the possibility of detection and evaluation,” Pattern Micro researchers Cyris Tseng and Pierre Lee stated in an evaluation final week.
“In 2022, Earth Hundun started utilizing the most recent model of Waterbear — often known as Deuterbear — which has a number of adjustments, together with anti-memory scanning and decryption routines, that make us contemplate it a special malware entity from the unique Waterbear.”
The cybersecurity agency is monitoring the menace actor underneath the moniker Earth Hundun, which is understood to be lively since not less than 2007. It additionally goes by different names reminiscent of Circuit Panda, HUAPI, Manga Taurus, Palmerworm, Crimson Djinn, and Temp.Overboard.
In a joint advisory revealed final September, cybersecurity and intelligence companies from Japan and the U.S. attributed the adversary to China, describing its potential to change router firmware and exploit routers’ domain-trust relationships to pivot from worldwide subsidiaries to their company headquarters based mostly within the two nations.
“BlackTech actors use customized malware, dual-use instruments, and living-off-the-land techniques, reminiscent of disabling logging on routers, to hide their operations,” the governments stated.
“Upon gaining an preliminary foothold right into a goal community and gaining administrator entry to community edge units, BlackTech cyber actors usually modify the firmware to cover their exercise throughout the sting units to additional keep persistence within the community.”
One of many essential instruments in its multifaceted arsenal is Waterbear (aka DBGPRINT), which has been put to make use of since 2009 and has been constantly up to date through the years with improved protection evasion options.
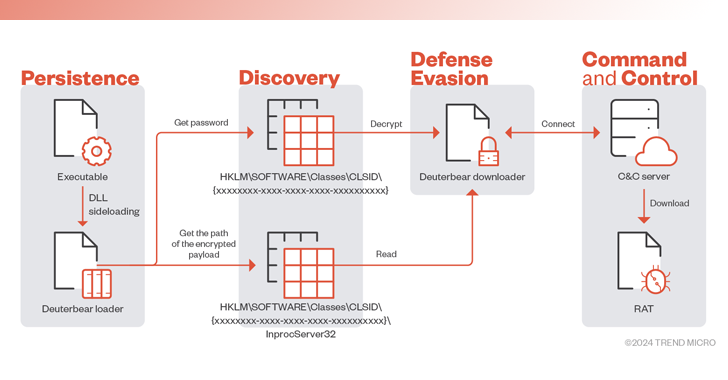
The core distant entry trojan is fetched from a command-and-control (C2) server via a downloader, which is launched utilizing a loader that, in flip, is executed through a identified method known as DLL side-loading.
The latest model of the implant helps practically 50 instructions, enabling it to carry out a variety of actions, together with course of enumeration and termination, file operations, window administration, begin and exit distant shell, screenshot seize, and Home windows Registry modification, amongst others.
Additionally delivered utilizing the same an infection circulation since 2022 is Deuterbear, whose downloader implements an array of obfuscation strategies to withstand anti-analysis and makes use of HTTPS for C2 communications.
“Since 2009, Earth Hundun has repeatedly advanced and refined the Waterbear backdoor, in addition to its many variants and branches,” the researchers stated.
“The Deuterbear downloader employs HTTPS encryption for community site visitors safety and implements varied updates in malware execution, reminiscent of altering the perform decryption, checking for debuggers or sandboxes, and modifying site visitors protocols.”