Attackers are more and more making use of “networkless” assault strategies focusing on cloud apps and identities. This is how attackers can (and are) compromising organizations – with out ever needing to the touch the endpoint or typical networked programs and companies.
Earlier than stepping into the small print of the assault strategies getting used, let’s focus on why these assaults have gotten extra prevalent.
SaaS adoption is altering the make-up of firm IT
The SaaS revolution and product-led development have had a huge effect on the construction of firm networks, and the place core enterprise programs and information reside.
Most organizations at present are utilizing tens to tons of of SaaS purposes throughout enterprise features. Some are solely SaaS-native, with no conventional community to talk of, however most have adopted a hybrid mannequin with a mix of on-premise, cloud, and SaaS companies forming the spine of enterprise purposes getting used.
The majority of SaaS adoption is user-driven, versus centrally managed by IT, as bottom-up adoption is inherent to product-led development. The newest information from Push Safety signifies that just one in 5 SaaS apps have been sanctioned by the enterprise. The bulk is just unknown and, due to this fact, has not been reviewed in any respect.
Cloud and SaaS apps are designed to be interconnected, functioning just like the closed networks of inside enterprise purposes you may need used prior to now. The car for this interconnectedness is identification.
Digital identities are more and more difficult and arduous to safe
Essentially the most fundamental type of identification is a consumer account created for companies you signal as much as with a username/e-mail and password. To scale back the chance of account takeover and complexity of managing an ever-increasing variety of accounts, organizations are utilizing the companies of identification suppliers (IdPs) to centralize entry to apps inside a single platform and identification, utilizing protocols like single signal on (SSO) and OAuth to handle authentication and authorization respectively.
The actual make-up of an identification can fluctuate rather a lot. Relying on the app, it is potential to have a number of authentication mechanisms for a similar account – for instance, by way of SAML, social logins (OIDC), and username and password. While SAML requires that admins set it up upfront for a given app tenant, customers can join an app utilizing OIDC just by utilizing the “sign up with Google” characteristic.
In impact this creates a number of identities tied to a single account, which might introduce quite a lot of confusion and complexity – for instance, simply because an IdP admin deletes that account, does not imply the app/account cannot then be accessed by utilizing one of many different login strategies that is been created. This will make it arduous to know what apps are in use, and what identities exist within the group.
So, in apply, it is potential to finish up with a mix of the next:
- Identification suppliers (usually 3 per group on common) (e.g., Okta, Entra/Microsoft, Google)
- Apps performing as an SSO platform for related apps (e.g., Atlassian Entry, Adobe Inventive Cloud)
- SaaS apps utilizing completely different authentication (SAML, OIDC) and authorization (OAuth) protocols
- SaaS apps with a neighborhood username and password
- Credentials and secrets and techniques saved in password supervisor and authenticator apps (which could be in browsers, on native OS, and in third occasion apps)
It will possibly get fairly difficult – with most organizations having 100+ apps of their stock, leading to 1000’s of sprawled identities.
Then, relying on the OAuth scopes permitted for a given app, permissions and workflows in a single app can affect different apps the place approval is granted for them to speak to at least one one other.
Identification is the glue that holds this ecosystem collectively. Nevertheless, the controls that exist to safe identification have severe limitations. Corporations usually suppose that every one their apps and identities have MFA rolled out or all apps are behind SSO. However the actuality is that just one/3 of apps truly help SSO (and lots of of those solely on the premium tier, with a hefty value improve). Additional, round 60% of distinctive identities (i.e., not utilizing SSO) don’t have MFA registered.
So in actuality, there are vital gaps within the safety controls defending cloud identities, whereas identities and cloud apps have gotten extra prevalent.
Attackers are focusing on cloud identification vulnerabilities
Attackers are paying attention to this. In accordance with Verizon’s 2024 DBIR, 74% of all breaches concerned the human factor, focusing on compromised consumer accounts by way of human error, privilege misuse, use of compromised credentials, or social engineering.
Whereas that is nothing new (some description of identification/phishing assaults have been the highest assault vector since a minimum of 2013), Crowdstrike’s newest international risk report goes additional, noting that 75% of assaults to achieve entry had been malware-free, and that “cloud-conscious” assaults (deliberate reasonably than opportunistic focusing on of cloud companies to compromise particular performance) elevated 110%. Microsoft additionally notes round 4,000 password assaults per second particularly focusing on cloud identities, whereas there are options from Google staff that assaults trying to steal session cookies (and due to this fact bypass MFA) occur at roughly the identical order of magnitude as password-based assaults.
Wanting past the numbers, proof from breaches within the public eye tells the identical story. Menace teams like APT29/Cozy Bear/The Dukes and Scattered Spider/0ktapus present how attackers are actively focusing on IdP companies, SaaS apps, and SSO/OAuth to hold out high-profile assaults in opposition to corporations like Microsoft and Okta.
If you wish to learn extra about this, you possibly can try this weblog submit monitoring identification assaults seen within the wild.
Cloud apps and identities are the brand new land of alternative for attackers. Due to the shift to cloud companies, they provide the identical worth as a standard assault designed to breach a community perimeter by way of the endpoint. In some ways, identification itself is the brand new assault floor. Opposite to different safety boundaries just like the community or endpoint, it additionally presents a lot much less of an impediment when it comes to the controls that at the moment exist to defend this new perimeter.
Identification-based assaults was localized to the endpoint or adjoining “identification programs” like Energetic Listing. The aim for the attacker was to breach this perimeter and transfer inside the group. Now, identification is way more dispersed – the gateway to an ecosystem of interconnected cloud apps and companies, all accessed over the web. This has considerably shifted the magnitude of the problem going through safety groups. In spite of everything, it is a lot more durable to cease credential-stuffing assaults in opposition to 100 SaaS apps than the only centralized exterior VPN/webmail endpoint of yesteryear.
Cloud identities are the brand new perimeter
It appears fairly clear that cloud identities are the brand new digital perimeter. This is not the long run, it is now. The one piece that’s nonetheless to be decided is what offensive strategies and tradecraft will emerge, and what the business response can be to be able to cease them.
| Safety period | Methods of the day | Trade response |
| 2000s Conventional perimeter hacking | Port scanners, vuln scanners, buffer overflows, net app assaults, WiFi hacking, consumer/server backdoors | Firewalls, DMZs, patch administration, safe coding, WPA, penetration testing |
| 2010s Endpoint is the brand new perimeter | Phishing, workplace macros, file format bugs, browser exploits, reminiscence resident implants, C2 frameworks | Endpoint hardening, EDR, SIEMS, crimson teaming, risk looking |
| 2020s Cloud identities are the new perimeter | ??? | ??? |
Final 12 months, Push Safety launched a matrix of SaaS assault strategies on GitHub (impressed by the extra endpoint-focused MITRE ATT&CK Framework) that demonstrates how attackers can goal a enterprise with out touching conventional surfaces such because the community or endpoints.
When chained collectively, these strategies allow an attacker to finish an end-to-end assault within the cloud.
Push has additionally launched a variety of weblog posts overlaying how these strategies can be utilized – the preferred strategies are summarized under:
| Approach | Overview |
| AiTM phishing | AiTM phishing makes use of devoted tooling to behave as an internet proxy between the sufferer and a official login portal for an software the sufferer has entry to, principally to make it simpler to defeat MFA safety. By proxying in real-time to the goal login portal, the adversary is given entry to each a sound password and legitimate session cookies they’ll steal and use to hijack the session. As soon as logged-in, a sufferer consumer will see all the true information they’d anticipate to see ordinarily (e.g. their very own emails/recordsdata and many others) as it’s a proxy of the true software. This reduces their possibilities of realizing they’ve been compromised as a result of genuine working nature of the proxied software. |
| IM phishing | IM apps like Groups and Slack are an effective way for attackers to evade extra stringent email-based phishing protections round malicious hyperlinks and attachments. The immediacy and real-time nature of IM makes it a helpful vector for phishing assaults as customers are much less acquainted with these apps as supply vectors for phishing assaults. Utilizing IM, it’s potential to spoof/impersonate customers, use bot accounts to create plausible dialogue, abuse hyperlink preview performance, and retrospectively edit messages and accounts to scrub up your tracks. |
| SAMLjacking | SAMLjacking is the place an attacker makes use of SAML SSO configuration settings for a SaaS tenant they management to be able to redirect customers to a malicious hyperlink of their selecting in the course of the authentication course of. This may be extremely efficient for phishing as the unique URL can be a official SaaS URL and customers expect to offer credentials. It will also be used for lateral motion if an admin account for a SaaS app is compromised, by modifying or enabling SAML, pointing the URL to a credential phishing web page that appears like or proxies a official authentication service (e.g. Google or Microsoft). The adversary can then goal customers by sending seemingly official hyperlinks to the app login web page to the tenant, which then features within the method of a watering gap assault. |
| Oktajacking | An attacker can set-up their very own Okta tenant for use in extremely convincing phishing assaults. This assault works as a result of Okta forwards credentials from logins for accounts tied to AD to its personal AD agent that runs on the goal community. Then, Okta permits the agent to report again to them about whether or not the login must be profitable or not. This permits an attacker who has compromised an AD agent, or is ready to emulate one, to each monitor login credentials for Okta customers and supply skeleton key-like performance to authenticate to Okta as any consumer they like. It will also be used equally to SAMLjacking for lateral motion – besides you need not redirect to a separate malicious area. |
| Shadow workflows | A shadow workflow is a method for utilizing SaaS automation apps to offer a code execution-like technique for conducting malicious actions from a official supply utilizing OAuth integrations. This could possibly be a every day export of recordsdata from shared cloud drives, automated forwarding and deleting of emails, cloning immediate messages, exporting consumer directories — mainly something that’s potential utilizing the goal app’s API. |
Networkless assault strategies in motion
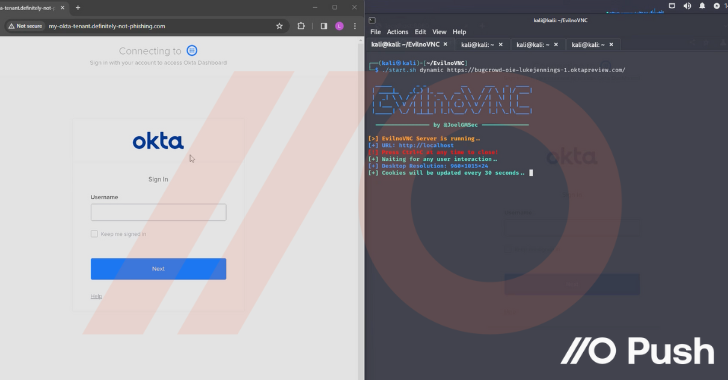
However there’s nothing fairly like seeing them in motion to grasp simply how impactful these strategies could be. So try the clip under from Luke Jennings, VP of R&D at Push. On this video, he covers:
- Preliminary entry by way of AiTM phishing utilizing EvilNoVNC, a Browser within the Browser (BitB) phishing framework, to hijack a consumer Okta session
- Stealing credentials from the browser session and accessing additional apps by way of Okta SSO, configuring these apps to create persistent entry and backdoor the apps
- Performing additional credential theft for different customers of these apps inside the company tenant by abusing SAML and SWA logins
- Straight accessing delicate information and performance inside compromised apps
May you detect and reply to this assault?
After seeing what’s potential, it is essential to ask – might you detect and reply to this assault state of affairs?
- Would you detect the preliminary AiTM phish?
- What number of customers could be compromised by way of the SAMLjacking assault?
- Would you discover all of the completely different backdoors in a number of SaaS apps?
- …or simply reset the password and MFA tokens for the Okta account?
- …and what concerning the passwords for all of the non-SAML apps?
Most organizations have a safety hole in terms of identity-based assaults. That is largely as a result of the controls round identification safety are usually centered on securing central identification programs (suppose Energetic Listing/Entra ID) versus the bigger identification infrastructure because it pertains to cloud apps and companies.
Equally, the controls that organizations have invested in are largely bypassed by these assaults. EDR instruments used to safe underlying working programs have minimal presence right here as a result of these apps are accessed within the browser – more and more touted as the brand new working system. As mentioned right here, securing the identification is completely important to defending companies within the cloud. And a good portion of the assault chain – for instance, phishing makes an attempt on the whole, together with AiTM and BitB strategies designed to bypass MFA, or password sharing throughout apps and companies, are merely not coated by endpoint safety instruments, IdP logs, or SaaS logs from particular person apps and companies.
These kinds of assaults are an actual problem for a lot of organizations proper now as a result of they fall by the cracks of current safety instruments and companies.
Involved in studying extra?
If you wish to discover out extra about identification assaults within the cloud and how you can cease them, try Push Safety – you possibly can check out their browser-based agent totally free!