Tremendous Low RPO with Steady Information Safety:
Dial Again to Simply Seconds Earlier than an Assault
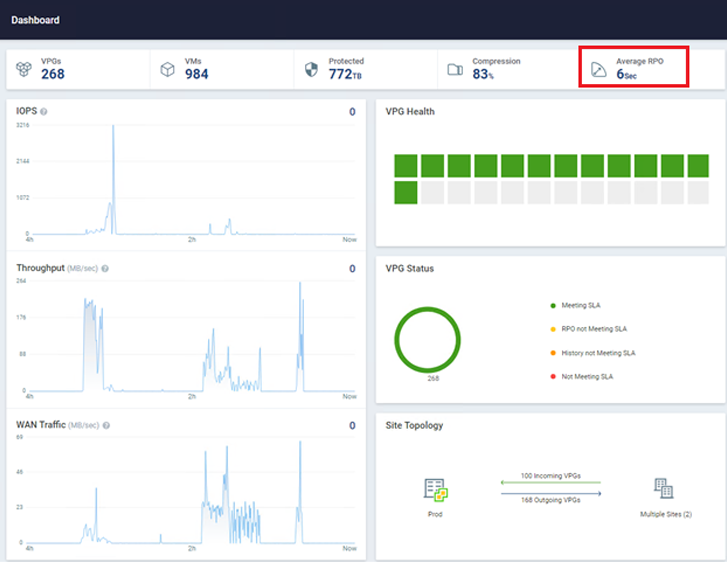
Zerto, a Hewlett Packard Enterprise firm, may help you detect and recuperate from ransomware in close to real-time. This answer leverages steady information safety (CDP) to make sure all workloads have the bottom restoration level goal (RPO) potential. Essentially the most beneficial factor about CDP is that it doesn’t use snapshots, brokers, or every other periodic information safety methodology. Zerto has no influence on manufacturing workloads and might obtain RPOs within the area of 5-15 seconds throughout hundreds of digital machines concurrently. For instance, the atmosphere within the picture beneath has practically 1,000 VMs being protected with a median RPO of simply six seconds!
Utility-Centric Safety:
Group Your VMs to Achieve Utility-Stage Management
You may defend your VMs with the Zerto application-centric strategy utilizing Digital Safety Teams (VPGs). This logical grouping of VMs ensures that your entire software stacks may be recovered in a single cohesive unit, with checkpoints taken solely seconds other than the very same time limit throughout a number of VMs within the group.
Actual-Time, In-Line Encryption Detection:
Obtain Early Warning When an Assault Happens
Zerto can detect potential ransomware assaults in real-time, in contrast to different merchandise that want to attend for a backup to finish earlier than scanning the info. Zerto scans information in-line in real-time as it’s being replicated, supplying you with the earliest warning signal of a possible cyberattack occurring inside your atmosphere.
Let’s check out what a ransomware assault and Zerto restoration appear to be.
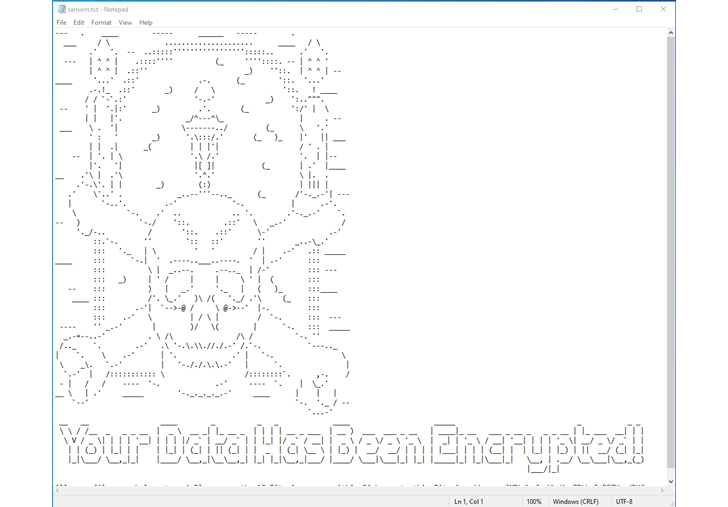
In a real-life cyberattack situation, you would not knowingly encrypt your information. It is obvious that the file server on this graphic has been contaminated with ransomware, which encrypted the information hosted inside it.
After a ransomware assault, information will all be encrypted and can’t be used.
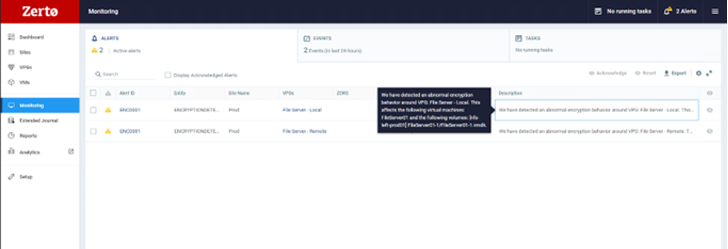
Utilizing Zerto, early in a cyberattack, you will see a triggered warning in your Zerto console, indicating potential suspicious exercise in your VM. You may drill all the way down to see the precise disk the anomalous exercise is being generated from, permitting you to shortly determine contaminated machines, restrict blast radius, and create a timeline of occasions to assist in investigations and forensics post-recovery, as proven on this picture.
On the spot File Stage Restoration:
Restore an Utility or a VM—or Even Drill Right down to a Single File
Upon an assault, you will obtain automated alerts by way of e-mail or notifications from the Zerto extensible APIs, enabling you to take motion shortly. You may restore information straight again into the VM in actual time, from solely seconds earlier than the encryption occasion, guaranteeing minimal information loss.
The graphic beneath reveals how. First, choose Restore, then Information.
Subsequent, select the VM you wish to restore from and to. As soon as you’ve got made these choices, you may browse Zerto’s distinctive journaling capabilities. You will discover there are over 700 cut-off dates, solely seconds aside, which you can recuperate from. This ensures your RPO is as little as potential. Then, you will evaluation these checkpoints, figuring out those Zerto has tagged as suspicious. Afterward, you may return slightly additional and look at those marked as clear. This course of means that you can recuperate straight earlier than suspicious exercise was detected.
Now, you may browse the information and folders you want to restore utilizing a easy wizard. Choose the information you wish to restore, select a set of credentials to authenticate into the VM, and hit Restore,
as proven beneath. Your information will now recuperate straight again into manufacturing with out the usage of any brokers contained in the OS and with solely seconds of information loss.
The restoration course of is easy and quick to realize, with minimal disruption to any group.
Now, let’s contemplate how we might recuperate within the occasion of a larger-scale assault that impacts a number of VMs and even lots of concurrently. By utilizing the failover perform inside Zerto, you may set off a full failover of all chosen VPGs and the VMs inside them to a secondary website. This secondary website may very well be one other VMware website, Hyper-V, or perhaps a public cloud. With full automation and orchestration, a Zerto failover can obtain advantages like these:
- 1000’s of VMs with an RTO of minutes
- Full re-IP of every VM, if required
- Restoring straight onto production-grade storage of your selection with no further migrations required (comparable to Storage vMotion)
- Restoring straight again onto production-grade compute with none additional steps comparable to vMotion
This sort of restoration is good for cyber restoration as a result of large-scale recoveries may be troublesome to realize with backup instruments that aren’t designed for restoration at scale.
Quick Failover to Secondary Web site with Full Automation and Orchestration: Mobilize, Transfer, and Recuperate with Automated Processes
As you may see, Zerto has some distinctive and thrilling capabilities relating to ransomware resilience.
To summarize:
- Zerto means that you can recuperate in minutes to simply seconds earlier than an assault, from information and folders to hundreds of VMs creating complicated purposes.
- Actual-time, in-line encryption detection helps determine anomalous exercise, restrict blast radius, and supply the earliest warning sign that an assault could also be occurring.
- A full, built-in automation and orchestration suite means there is not any want for added instruments to make sure your large-scale recoveries are as easy and quick as potential.
Do not watch for an assault to occur! Defend your group and acquire confidence with Zerto. Strive Zerto free for 14 days!