It’s taking much less time for organisations to detect attackers of their setting, a report by Mandiant Consulting, part of Google Cloud, has discovered. This means that corporations are strengthening their safety posture.
The M-Developments 2024 report additionally highlighted that the highest focused industries of 2023 had been monetary providers, enterprise {and professional} providers, tech, retail and hospitality, healthcare and authorities. This aligns with the truth that 52% of attackers had been primarily motivated by monetary achieve, as these sectors typically possess a wealth of delicate — and due to this fact precious — data.
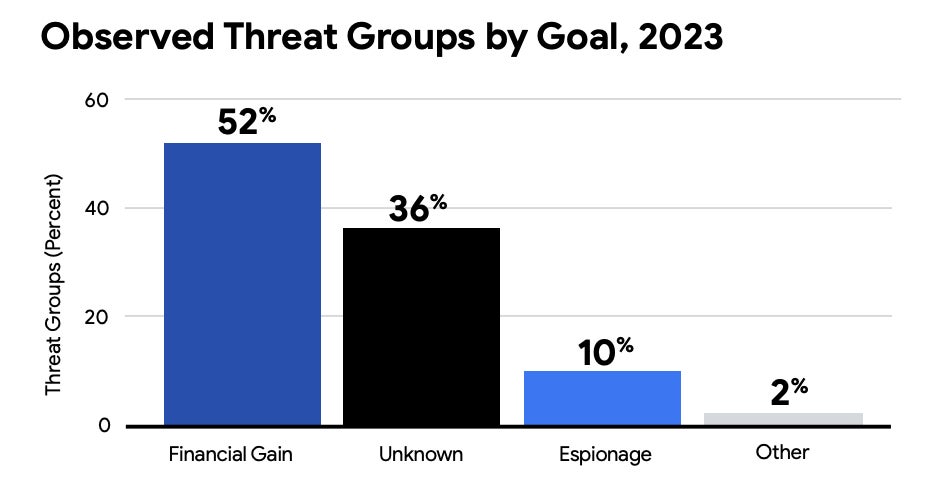
Financially-motivated exercise was discovered to have gone up by 8% since 2022, which is partially defined by the parallel rise in ransomware and extortion instances. The most typical ways in which menace actors gained entry to a goal community had been by means of exploits, phishing, prior compromise and stolen credentials.
Dr Jamie Collier, Mandiant Risk Intelligence Advisor Lead for Europe, advised TechRepublic in an e mail: “Regardless of the give attention to ransomware and extortion operations inside the safety group, these assaults stay efficient throughout a spread of sectors and areas. Extortion campaigns due to this fact stay extremely worthwhile for cyber criminals.
“Because of this, many financially-motivated teams conducting different types of cyber crime have transitioned to extortion operations within the final 5 years.”
TechRepublic takes a deeper look into the highest 5 cyber safety tendencies of 2023 and knowledgeable suggestions highlighted by the fifteenth annual M-Developments report:
- International organisations are enhancing their cyber defences.
- Cyber criminals have an elevated give attention to evasion.
- Cloud environments are being focused extra typically.
- Cyber criminals are altering ways to bypass MFA.
- Crimson groups are utilizing AI and enormous language fashions.
1. International organisations are enhancing their cyber defences
In line with the M-Developments report, the median dwell time of worldwide organisations decreased from 16 days in 2022 to 10 days in 2023 and is now at its lowest level in additional than a decade. The dwell time is the period of time attackers stay undetected inside a goal setting and signifies the power of a enterprise’s cyber posture. This determine means that corporations are making significant enhancements to their cyber safety.
Nonetheless, there could possibly be one other contributing issue; the typical proportion of assaults as a result of ransomware elevated to 23% in 2023 over 18% in 2022.
Dr. Collier defined to TechRepublic: “The impression of extortion operations is straight away apparent. Within the occasion when ransomware is deployed, a sufferer’s programs might be encrypted and rendered unusable. Alternatively, if knowledge is stolen, a cyber prison will shortly be in contact to extort a sufferer.”
SEE: High 7 Cybersecurity Threats for 2024
Organisations within the Asia-Pacific area noticed the most important discount in median dwell time, with it reducing by 24 days over the past yr. Mandiant analysts hyperlink this to the truth that nearly all of assaults detected had been ransomware-related, and this majority was greater than some other area. In the meantime, corporations in Europe, the Center East and Africa noticed the typical dwell time enhance by two days. That is regarded as because of the regional knowledge normalising following a concerted defensive effort by Mandiant in Ukraine in 2022.
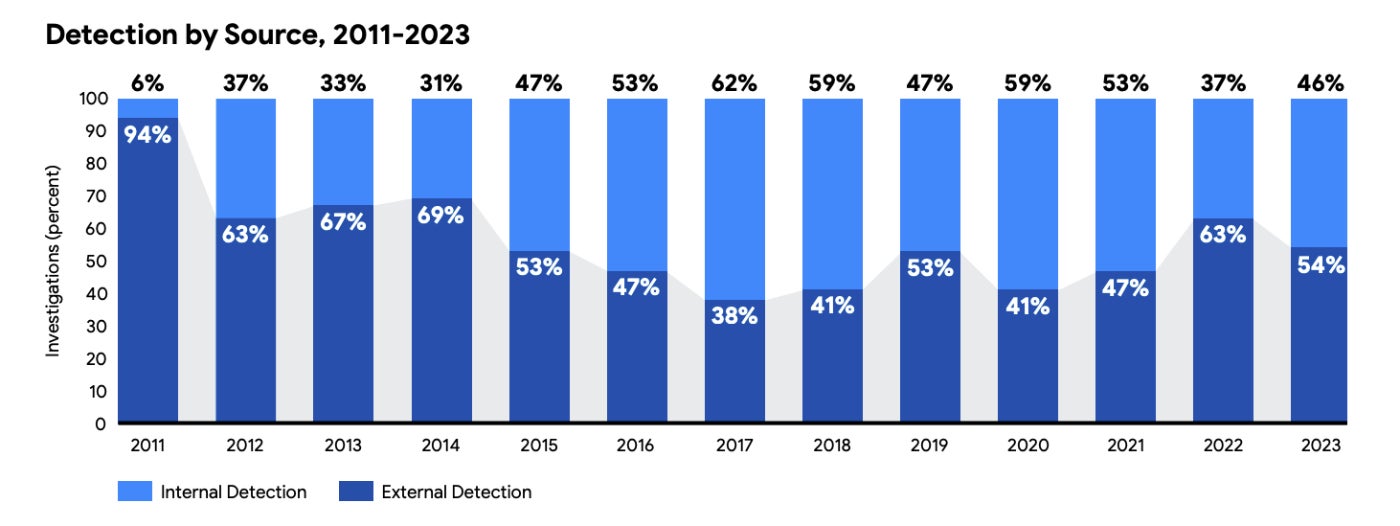
One other proof that companies are getting higher at detecting cyber threats is that Mandiant discovered that 46% of compromised organisations first recognized proof of compromise internally quite than by an outdoor entity like a legislation enforcement company or cyber safety firm, up from 37% in 2022.
2. Cyber criminals have an elevated give attention to evasion
Cyber criminals are more and more focusing on edge units, utilizing “residing off the land” strategies, and deploying zero-day exploits, suggesting a renewed give attention to sustaining persistence on networks for so long as doable.
Dr. Collier advised TechRepublic: “With community defenders more and more looking out for extortion campaigns, evasive ways enhance the probabilities of a profitable operation. Ransomware operations are far simpler when cyber criminals can attain essentially the most delicate and important areas of a goal’s community and evasive ways assist them to attain this.”
Concentrating on edge units
Edge units usually lack endpoint detection and response (EDR) capabilities, so they’re strong targets for cyber criminals seeking to go beneath the radar. In 2023, Mandiant investigators discovered that the primary and third most focused vulnerabilities had been associated to edge units. These had been:
- CVE-2023-34362: A SQL injection vulnerability within the MOVEit file switch software.
- CVE-2023-2868: A command injection vulnerability in bodily Barracuda E mail Safety Gateway home equipment.
The report authors wrote: “Mandiant expects that we are going to proceed to see focusing on of edge units and platforms that historically lack EDR and different safety options because of the challenges related to discovery and investigation of compromise. Exploitation of those units will proceed to be a beautiful preliminary entry vector for Chinese language espionage teams to stay undetected and keep persistence into goal environments.”
SEE: Q&A on how Dell sees safety on the edge
Distant administrator instruments and “residing off the land” strategies
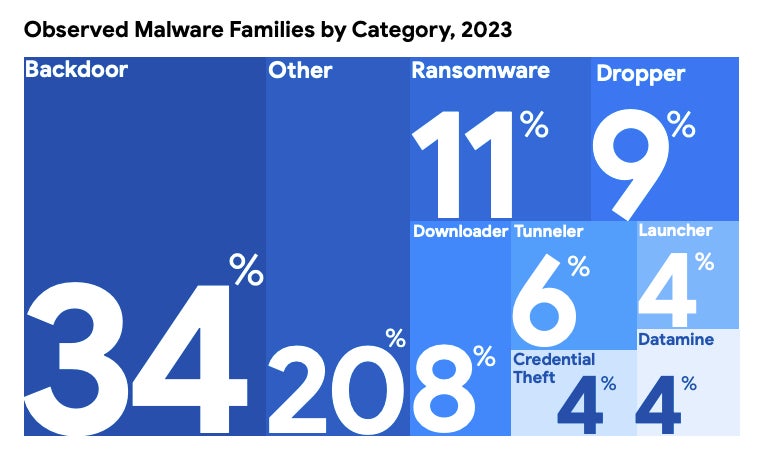
About 20% of malware households detected by Mandiant in 2023 didn’t match right into a typical class, which is the next proportion than earlier years. Moreover, 8% of assaults on this “different” class concerned the usage of distant administration instruments and different utilities. These are much less prone to be flagged by default by EDR, or different safety instruments, which may preserve the attacker undetected, and are sometimes coupled with “residing off the land” strategies.
Residing off the land is the usage of reputable, pre-installed instruments and software program inside a goal setting throughout a cyber assault to assist evade detection. This may scale back the general complexity of the malware by permitting the attacker to weaponize current options which have already been safety examined by the organisation. It’s significantly efficient with edge units as a result of they’re usually not monitored by community defenders, permitting them to stay on the community for longer.
A latest instance the Mandiant researchers noticed is a backdoor named THINCRUST, which was appended into the online framework information that had been liable for offering the API interface for FortiAnalyzer and FortiManager units. The menace actors had been in a position to harness the native API implementation to entry and ship instructions to THINCRUST by merely interacting with a brand new endpoint URL that they had added.
Zero-day exploits
In 2023, Mandiant researchers tracked 97 distinctive zero-day vulnerabilities exploited within the wild, representing a greater than 50% progress in zero-day utilization over 2022. The zero-days had been exploited by espionage teams and financially-motivated attackers seeking to steal precious knowledge to show a revenue.
The report’s authors anticipate the variety of recognized zero-day vulnerabilities and exploits that concentrate on them will proceed to develop within the coming years as a result of quite a lot of components, together with:
- Rise of zero-day exploitation by ransomware and knowledge extortion teams: In 2023, zero-day exploits in MOVEit, GoAnywhere, Citrix and PaperCut had been focused considerably because of leak website posts.
- Continued state-sponsored exploitation assaults: A Microsoft report discovered situations of nation-state cyber espionage rose final yr.
- Development of “turnkey” exploit kits: Turnkey exploit kits are off-the-shelf instruments that may be bought from business surveillance distributors. A report by HP Wolf Safety famous a surge in Excel information with DLLs contaminated with a budget Parallax distant entry Trojan in 2023.
Suggestions from the M-Developments report
- Preserve patch administration of edge units to forestall exploitation of recognized vulnerabilities.
- Take a “defence-in-depth” method to help in detecting proof of zero-day exploitation.
- Carry out investigations and community searching actions if there’s suspicion of compromise and, if there may be, goal to find how attackers entered and maintained entry.
- Observe safety distributors’ steerage for hardening structure to reinforce defences.
- Guarantee you will have an incident response plan and conduct broad environmental monitoring.
- Layer community segmentation and logging with superior EDR options.
- Consider distributors’ safety practices and community necessities earlier than deploying new {hardware} or software program to determine a baseline for regular use.
3. Cloud environments are being focused extra typically
Cloud adoption is repeatedly rising — Gartner predicts greater than 50% of enterprises will use trade cloud platforms by 2028 — and, due to this fact, extra attackers are turning their consideration to those environments. In line with CrowdStrike, there was a 75% enhance in cloud intrusions in 2023 over 2022.
Mandiant analysts say attackers are focusing on weakly applied identification administration practices and credential storage to acquire reputable credentials and circumvent multifactor authentication (MFA).
SEE: UK’s NCSC Points Warning as SVR Hackers Goal Cloud Providers
Mandiant noticed situations the place attackers gained entry to cloud environments as a result of they occurred throughout credentials that weren’t saved securely. Credentials had been found on an internet-accessible server with default configurations or had been stolen or leaked in a earlier knowledge breach and never been modified since. Additionally they gained entry utilizing completely different strategies to bypass MFA, coated in additional element within the subsequent part.
As soon as contained in the cloud setting, the authors noticed dangerous actors performing quite a lot of ways to abuse the cloud providers, together with:
- Utilizing native instruments and providers to take care of entry, transfer laterally or steal knowledge: Exploiting pre-installed instruments like Azure Knowledge Manufacturing facility and Microsoft Entra ID meant the adversaries may lower their operational profile and evade detection for longer.
- Creating digital machines (VMs) to get unmonitored entry to the organisation’s cloud: When an attacker creates a VM that runs on the organisation’s cloud infrastructure, it is not going to have their mandated safety and logging software program put in on them. It could additionally enable for lateral motion to the on-premises community by way of VPN.
- Utilising the cloud’s processing energy for cryptomining.
- Utilizing open-source offensive safety toolsets to survey the setting.
Suggestions from the M-Developments report
- Replace worker authentication insurance policies.
- Use phishing-resistant MFA corresponding to certificate-based authentication and FIDO2 safety keys by way of SMS as an alternative of cellphone calls and one-time passwords.
- Implement controls that prohibit entry to cloud sources to solely trusted units.
4. Cyber criminals are altering ways to bypass MFA
Now that multifactor authentication has turn out to be a normal safety observe in lots of organisations, attackers are exploring new, inventive ways to bypass it. In line with Mandiant, the variety of compromises towards cloud-based identities configured with MFA is rising.
In 2023, the agency noticed a rise of adversary-in-the-middle (AiTM) phishing pages that steal post-authentication session tokens and permit dangerous actors to avoid MFA. In an AiTM marketing campaign, attackers arrange a proxy server that captures a consumer’s credentials, MFA codes and session tokens issued by the logon portal whereas relaying the connection to the reputable server.
SEE: New phishing and enterprise e mail compromise campaigns enhance in complexity, bypass MFA
The vast majority of enterprise e mail compromise instances Mandiant responded to in 2023 concerned the menace actor circumventing the consumer’s MFA by way of AiTM. Previously, the relative complexity of organising AiTM phishing infrastructure in comparison with conventional credential harvesting kinds could have saved the variety of these assaults low. Nonetheless, there are actually quite a lot of AiTM kits and phishing-as-a-service choices marketed within the cybercriminal underground, in accordance with Mandiant. These merchandise considerably decrease the barrier to entry for AiTM phishing, leading to an uptick.
Different strategies the Mandiant researchers noticed attackers utilizing to bypass MFA embody:
- Social engineering assaults: For instance, spear phishing emails the place the goal is coerced into revealing their login particulars on a spoofed website. The attacker then makes use of them to sign up on the reputable website, which sends an MFA notification to the consumer who accepts. The organisation’s assist desk can also be focused with an instruction to reset a password or MFA gadget.
- SIM-swapping: This entails transferring a goal’s cellphone quantity to a SIM card managed by an attacker, to allow them to settle for the MFA notification and take over an account. Mandiant noticed a rise in SIM-swapping assaults in 2023.
- Password-guessing: Attackers guess the passwords to dormant or service accounts that should not have MFA arrange to allow them to enrol their very own gadget.
Suggestions from the M-Developments report
- Implement AiTM-resistant MFA strategies and entry insurance policies that block logons based mostly on, for instance, organisation-defined places, gadget administration standing or historic logon properties.
- Monitor authentication logs for IP addresses related to phishing infrastructure, authentication with a stolen token or geographically infeasible logins.
5. Crimson groups are utilizing AI and enormous language fashions
Crimson groups include cyber safety analysts who plan and execute assaults towards organisations for the needs of figuring out weaknesses. In 2023, Mandiant consultants used generative AI instruments to hurry up sure actions in pink group assessments, together with:
- The creation of preliminary drafts of malicious emails and touchdown pages for fake social engineering assaults.
- The event of customized tooling for when analysts encounter unusual or new functions and programs.
- The analysis and creation of tooling in instances the place environments don’t match the operational norm that can be utilized repeatedly.
Dr. Collier advised TechRepublic: “The position of AI in pink teaming is very iterative with numerous backwards and forwards between massive language fashions (LLMs) and a human knowledgeable. This highlights the distinctive contribution of each.
“AI is usually nicely suited to repetitive duties or fetching data. But, having pink group consultants that perceive the commerce craft and possess the talents to use context supplied by LLMs in sensible conditions is much more vital.”
AI was additionally utilized in Mandiant’s purple group engagements, the place analysts should turn out to be acquainted with a consumer’s setting from the attitude of an attacker and defender to foster collaboration between pink and blue groups. Generative AI was used to assist them perceive the shopper’s platform and its safety extra shortly.
SEE: HackerOne: How Synthetic Intelligence Is Altering Cyber Threats and Moral Hacking
Within the report, the authors speculated on how cyber safety analysts may use AI sooner or later. Crimson groups generate a considerable quantity of knowledge that could possibly be used to coach fashions tuned to assist safe buyer environments. Nonetheless, AI builders may also have to seek out novel methods to make sure fashions have applicable guardrails in place whereas concurrently permitting for the reputable use of malicious exercise by pink groups.
“The mix of pink group experience and highly effective AI leads may lead to a future the place pink groups are significantly simpler, and organisations are higher in a position to keep forward of the danger posed by motivated attackers,” the authors wrote.
Methodology
The metrics reported in M-Developments 2024 are based mostly on Mandiant Consulting investigations of focused assault exercise carried out between January 1, 2023 and December 31, 2023.
