The lately uncovered cyber espionage marketing campaign concentrating on perimeter community gadgets from a number of distributors, together with Cisco, could have been the work of China-linked actors, in accordance with new findings from assault floor administration agency Censys.
Dubbed ArcaneDoor, the exercise is claimed to have commenced round July 2023, with the primary confirmed assault in opposition to an unnamed sufferer detected in early January 2024.
The focused assaults, orchestrated by a beforehand undocumented suspected refined state-sponsored actor tracked as UAT4356 (aka Storm-1849), entailed the deployment of two customized malware dubbed Line Runner and Line Dancer.
The preliminary entry pathway used to facilitate the intrusions has but to be found, though the adversary has been noticed leveraging two now-patched flaws in Cisco Adaptive Safety Home equipment (CVE-2024-20353 and CVE-2024-20359) to persist Line Runner.
Telemetry knowledge gathered as a part of the investigation has revealed the risk actor’s curiosity in Microsoft Change servers and community gadgets from different distributors, Talos mentioned final month.
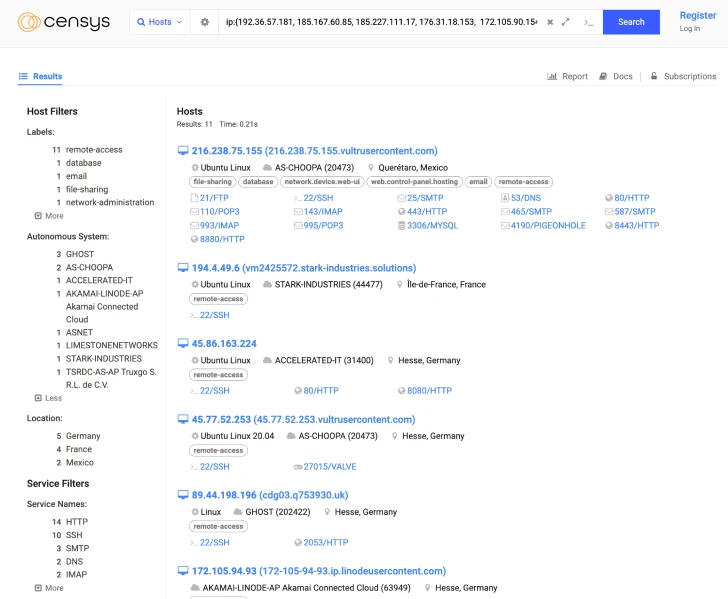
Censys, which additional examined the actor-controlled IP addresses, mentioned the assaults level to the potential involvement of a risk actor primarily based in China.
That is primarily based on the truth that 4 of the 5 on-line hosts presenting the SSL certificates recognized as related to the attackers’ infrastructure are related to Tencent and ChinaNet autonomous techniques (AS).
As well as, among the many risk actor-managed IP addresses is a Paris-based host (212.193.2[.]48) with the topic and issuer set as “Gozargah,” which is probably going a reference to a GitHub account that hosts an anti-censorship device named Marzban.
The software program, in flip, is “powered” by one other open-source challenge dubbed Xray that has a web site written in Chinese language.
This means that “a few of these hosts had been operating providers related to anti-censorship software program possible meant to avoid The Nice Firewall,” and that “a major variety of these hosts are primarily based in distinguished Chinese language networks,” suggesting that ArcaneDoor might be the work of a Chinese language actor, Censys theorized.
Nation-state actors affiliated with China have more and more focused edge home equipment in recent times, leveraging zero-day flaws in Barracuda Networks, Fortinet, Ivanti, and VMware to infiltrate targets of curiosity and deploy malware for persistent covert entry.
The event comes as French cybersecurity agency Sekoia mentioned it efficiently sinkholed a command-and-control (C2) server linked to the PlugX trojan in September 2023 by spending $7 to accumulate the IP handle tied to a variant of the malware with capabilities to propagate in a worm-like trend through compromised flash drives.
A better monitoring of the sinkholed IP handle (45.142.166[.]112) has revealed the worm’s presence in additional than 170 international locations spanning 2.49 million distinctive IP addresses over a six-month interval. A majority of the infections have been detected in Nigeria, India, China, Iran, Indonesia, the U.Ok., Iraq, the U.S., Pakistan, and Ethiopia.
“Many countries, excluding India, are members in China’s Belt and Highway Initiative and have, for many of them, coastlines the place Chinese language infrastructure investments are important,” Sekoia mentioned. “Quite a few affected international locations are positioned in areas of strategic significance for the safety of the Belt and Highway Initiative.”
“This worm was developed to gather intelligence in varied international locations concerning the strategic and safety considerations related to the Belt and Highway Initiative, totally on its maritime and financial facets.”