The financially motivated menace actor generally known as FIN7 has been noticed leveraging malicious Google adverts spoofing respectable manufacturers as a method to ship MSIX installers that culminate within the deployment of NetSupport RAT.
“The menace actors used malicious web sites to impersonate well-known manufacturers, together with AnyDesk, WinSCP, BlackRock, Asana, Concur, The Wall Road Journal, Workable, and Google Meet,” cybersecurity agency eSentire mentioned in a report revealed earlier this week.
FIN7 (aka Carbon Spider and Sangria Tempest) is a persistent e-crime group that is been energetic since 2013, initially dabbling in assaults focusing on point-of-sale (PoS) gadgets to steal cost knowledge, earlier than pivoting to breaching massive corporations by way of ransomware campaigns.
Over time, the menace actor has refined its ways and malware arsenal, adopting varied customized malware households reminiscent of BIRDWATCH, Carbanak, DICELOADER (aka Lizar and Tirion), POWERPLANT, POWERTRASH, and TERMITE, amongst others.
FIN7 malware is usually deployed by means of spear-phishing campaigns as an entry to the goal community or host, though in latest months the group has utilized malvertising strategies to provoke the assault chains.
In December 2023, Microsoft mentioned it noticed the attackers counting on Google adverts to lure customers into downloading malicious MSIX software packages, which finally led to the execution of POWERTRASH, a PowerShell-based in-memory dropper that is used to load NetSupport RAT and Gracewire.
“Sangria Tempest […] is a financially motivated cybercriminal group presently specializing in conducting intrusions that usually result in knowledge theft, adopted by focused extortion or ransomware deployment reminiscent of Clop ransomware,” the tech large famous on the time.
The abuse of MSIX as a malware distribution vector by a number of menace actors — doubtless owing to its capacity to bypass safety mechanisms like Microsoft Defender SmartScreen — has since prompted Microsoft to disable the protocol handler by default.
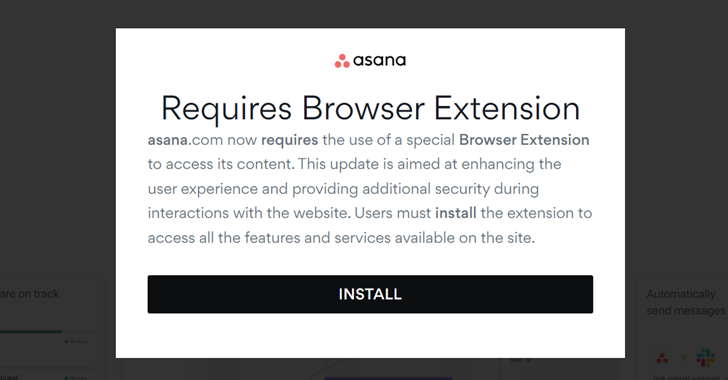
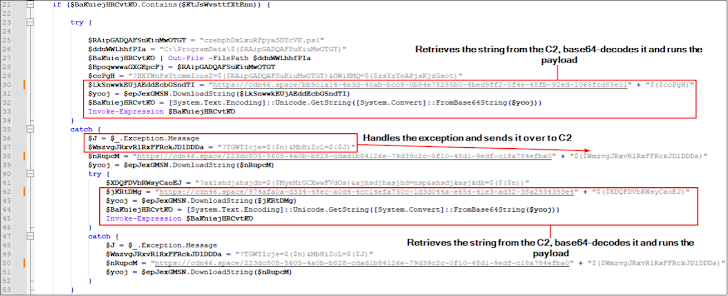
Within the assaults noticed by eSentire in April 2024, customers who go to the bogus websites by way of Google adverts are displayed a pop-up message urging them to obtain a phony browser extension, which is an MSIX file containing a PowerShell script that, in flip, gathers system data and contacts a distant server to fetch one other encoded PowerShell script.
The second PowerShell payload is used to obtain and execute the NetSupport RAT from an actor-controlled server.
The Canadian cybersecurity firm mentioned it additionally detected the distant entry trojan getting used to ship further malware, which incorporates DICELOADER by way of a Python script.
“The incidents of FIN7 exploiting trusted model names and utilizing misleading internet adverts to distribute NetSupport RAT adopted by DICELOADER spotlight the continuing menace, significantly with the abuse of signed MSIX information by these actors, which has confirmed efficient of their schemes,” eSentire mentioned.
Comparable findings have been independently reported by Malwarebytes, which characterised the exercise as singling out company customers by way of malicious adverts and modals by mimicking high-profile manufacturers like Asana, BlackRock, CNN, Google Meet, SAP, and The Wall Road Journal. It, nevertheless, didn’t attribute the marketing campaign to FIN7.
Information of FIN7’s malvertising schemes coincides with a SocGholish (aka FakeUpdates) an infection wave that is designed to focus on enterprise companions.
“Attackers used living-off-the-land strategies to gather delicate credentials, and notably, configured internet beacons in each electronic mail signatures and community shares to map out native and business-to-business relationships,” eSentire mentioned. “This conduct would counsel an curiosity in exploiting these relationships to focus on enterprise friends of curiosity.”
It additionally follows the invention of a malware marketing campaign focusing on Home windows and Microsoft Workplace customers to propagate RATs and cryptocurrency miners by way of cracks for fashionable software program.
“The malware, as soon as put in, typically registers instructions within the activity scheduler to take care of persistence, enabling steady set up of recent malware even after elimination,” Broadcom-owned Symantec mentioned.