A safety vulnerability has been disclosed within the LiteSpeed Cache plugin for WordPress that might allow unauthenticated customers to escalate their privileges.
Tracked as CVE-2023-40000, the vulnerability was addressed in October 2023 in model 5.7.0.1.
“This plugin suffers from unauthenticated site-wide saved [cross-site scripting] vulnerability and will enable any unauthenticated person from stealing delicate info to, on this case, privilege escalation on the WordPress website by performing a single HTTP request,” Patchstack researcher Rafie Muhammad stated.
LiteSpeed Cache, which is used to enhance website efficiency, has greater than 5 million installations. The newest model of the plugin in 6.1, which was launched on February 5, 2024.
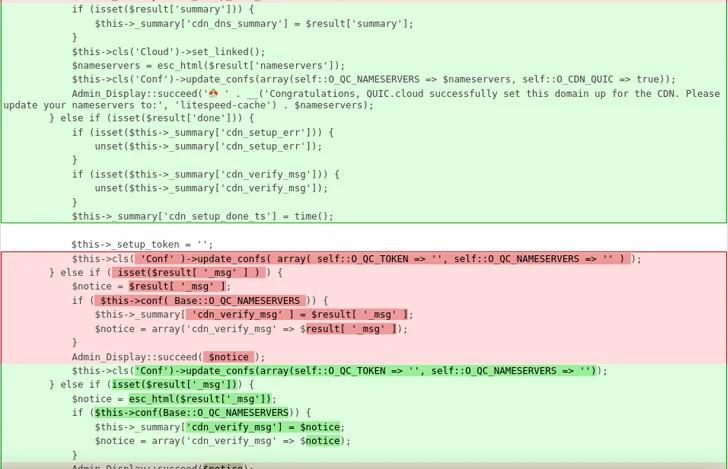
The WordPress safety firm stated CVE-2023-40000 is the results of an absence of person enter sanitization and escaping output. The vulnerability is rooted in a perform named update_cdn_status() and may be reproduced in a default set up.
“For the reason that XSS payload is positioned as an admin discover and the admin discover could possibly be displayed on any wp-admin endpoint, this vulnerability additionally could possibly be simply triggered by any person that has entry to the wp-admin space,” Muhammad stated.
The disclosure arrives 4 months after Wordfence revealed one other XSS flaw in the identical plugin (CVE-2023-4372, CVSS rating: 6.4) resulting from inadequate enter sanitization and output escaping on person equipped attributes. It was addressed in model 5.7.
“This makes it doable for authenticated attackers with contributor-level and above permissions to inject arbitrary internet scripts in pages that can execute each time a person accesses an injected web page,” István Márton stated.