Within the Sixties and ’70s, the US firearms market noticed an inflow of cheaply-made, imported handguns. Legislators focused the proliferation of those cheap and steadily unreliable weapons, ostensibly as a result of they had been believed to pose a danger to their homeowners and facilitate criminality. This was not a difficulty distinctive to the US or to that point interval, in fact; within the UK, the place handguns are actually strictly regulated, criminals usually resort to reactivated, and even home-made or vintage, firearms.
Regardless of ‘junk weapons’ usually being inaccurate and susceptible to malfunction, buying or creating them does have benefits for a would-be prison. Such weapons are unlikely to be on regulation enforcement’s radar, and will be troublesome to hint. They are typically low-cost, reducing the price of entry to illicit possession and utilization. And so they can usually be made or obtained while not having entry to in depth prison networks.
Throughout a current investigation into a number of underground cybercrime boards – significantly these frequented by lower-skilled risk actors – Sophos X-Ops found one thing fascinating: a ransomware equal to junk weapons.
We discovered a number of examples of independently produced, cheap, and crudely-constructed ransomware, principally offered as a one-time buy moderately than typical affiliate-based Ransomware-as-a-Service (RaaS) fashions (and not one of the ‘junk-gun ransomware’ we discovered seems on the ransomwatch group index as of this writing). This seems to be a comparatively new phenomenon (though, in fact, risk actors have been creating and promoting low-cost, low-quality RATs and different malware for many years). We additionally noticed different risk actors, a rung or two down the talents ladder, categorical curiosity in growing new ransomware – swapping recommendations on languages, evasion strategies, targets, and licencing fashions.
At first look, the prospect of people making and promoting junk-gun ransomware doesn’t appear to pose a big risk; it’s a far cry from the infamous, well-organized ransomware teams that normally come to thoughts. Right here, there aren’t any leak websites; no preliminary entry brokers (IABs); no associates; no corporate-like hierarchies; no multi-million greenback ransom calls for; no publicity stunts; no high-profile targets; no subtle malware meant to defeat superior EDR merchandise; no in search of headlines and media consideration; and little in-depth evaluation by researchers.
However as we dug deeper, we uncovered some regarding intelligence. Some people claimed to have used junk-gun ransomware in real-world assaults, finishing the complete assault chain by themselves, with out IABs. Others advocated utilizing it to assault small companies and people – targets that the likes of Cl0p and ALPHV/BlackCat would most likely not contemplate worthwhile, however which may however generate important revenue for a person risk actor. Some customers claimed to favor standalone ransomware as a result of they don’t should profit-share – as in lots of RaaS fashions – or depend on infrastructure developed and operated by others.
Away from the complicated infrastructure of recent ransomware, junk-gun ransomware permits criminals to get in on the motion cheaply, simply, and independently. They’ll goal small corporations and people, who’re unlikely to have the sources to defend themselves or reply successfully to incidents, with out giving anybody else a minimize.
After all, junk-gun ransomware could sometimes blow up in risk actors’ faces – it might be faulty, set off alerts, or be backdoored as a part of a rip-off – or their very own lack of expertise could lead to failure or detection. Of their minds, nonetheless, these are probably acceptable dangers – not least as a result of utilizing junk-gun ransomware could ultimately result in extra profitable employment alternatives with outstanding ransomware gangs.
On this article we’ll reveal our findings, share particulars of the junk-gun ransomware we discovered, and talk about the implications for organizations, the broader public, and the safety neighborhood.
We noticed 19 junk-gun ransomware varieties both provided on the market or cited as being below improvement, throughout 4 boards, between June 2023 and February 2024. Our findings are summarized within the desk under.
| Identify | Date posted | Standing | Value | Language | Utilized in assaults | Detection | Options |
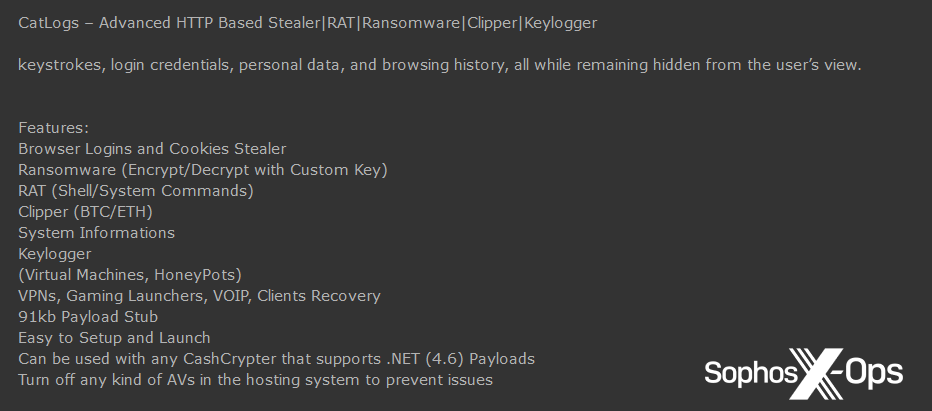
| CatLogs | December 2023 | On the market | Unknown | .NET | Unknown | Unknown | Stealer, RAT, ransomware, clipper, keylogger |
| Unnamed console app | November 2023 | In improvement | N/A | C# | N/A | Defender, 2/70 VT | Loops over desktop, paperwork, photos, music, movies |
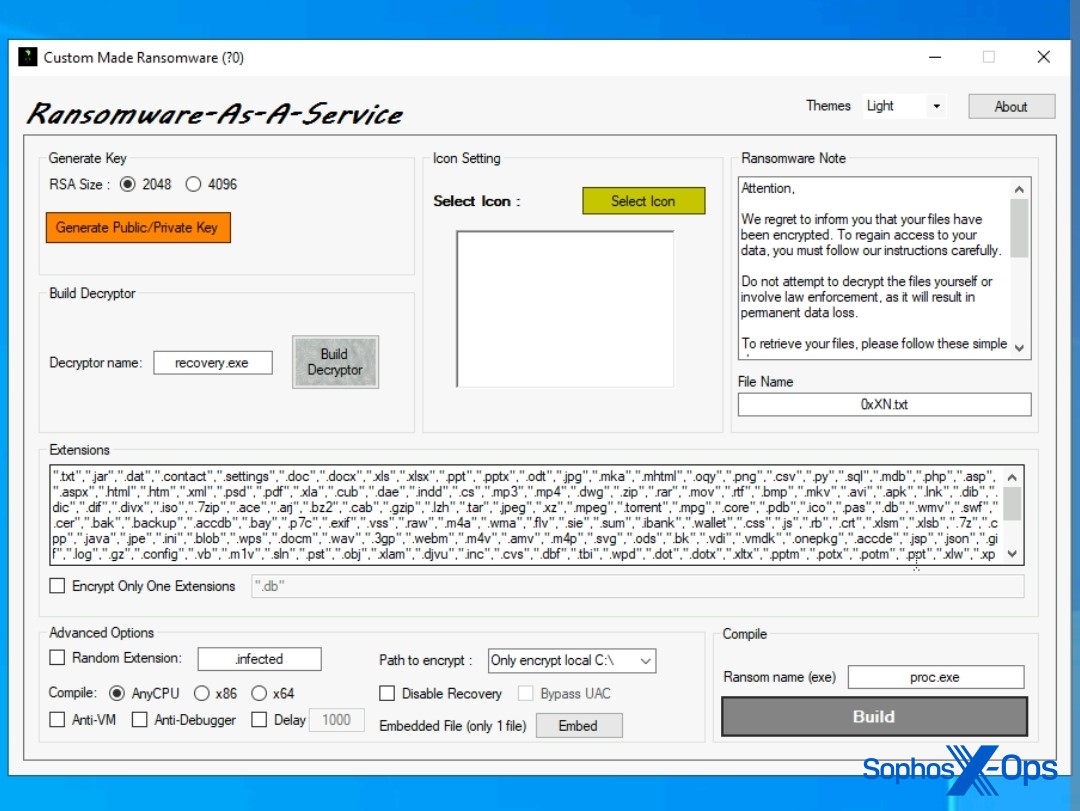
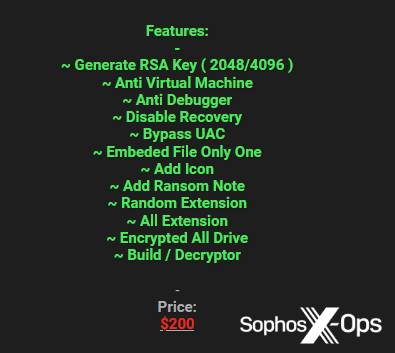
| Customized RaaS | July 2023 | On the market | $200 | Unknown | Unknown | Unknown | RSA 2048/4096, anti-VM and debugger, UAC bypass, random extensions |
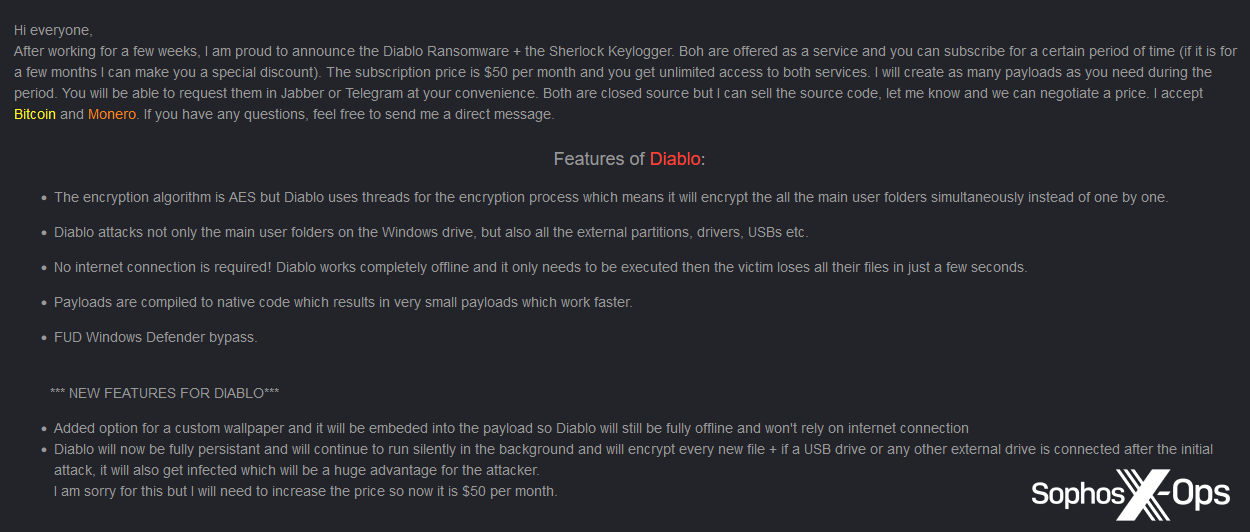
| Diablo | January 2024 | On the market | $50 monthly | Unknown | Unknown | Defender | AES, threaded, exterior drives, offline mode, Defender bypass, persistence |
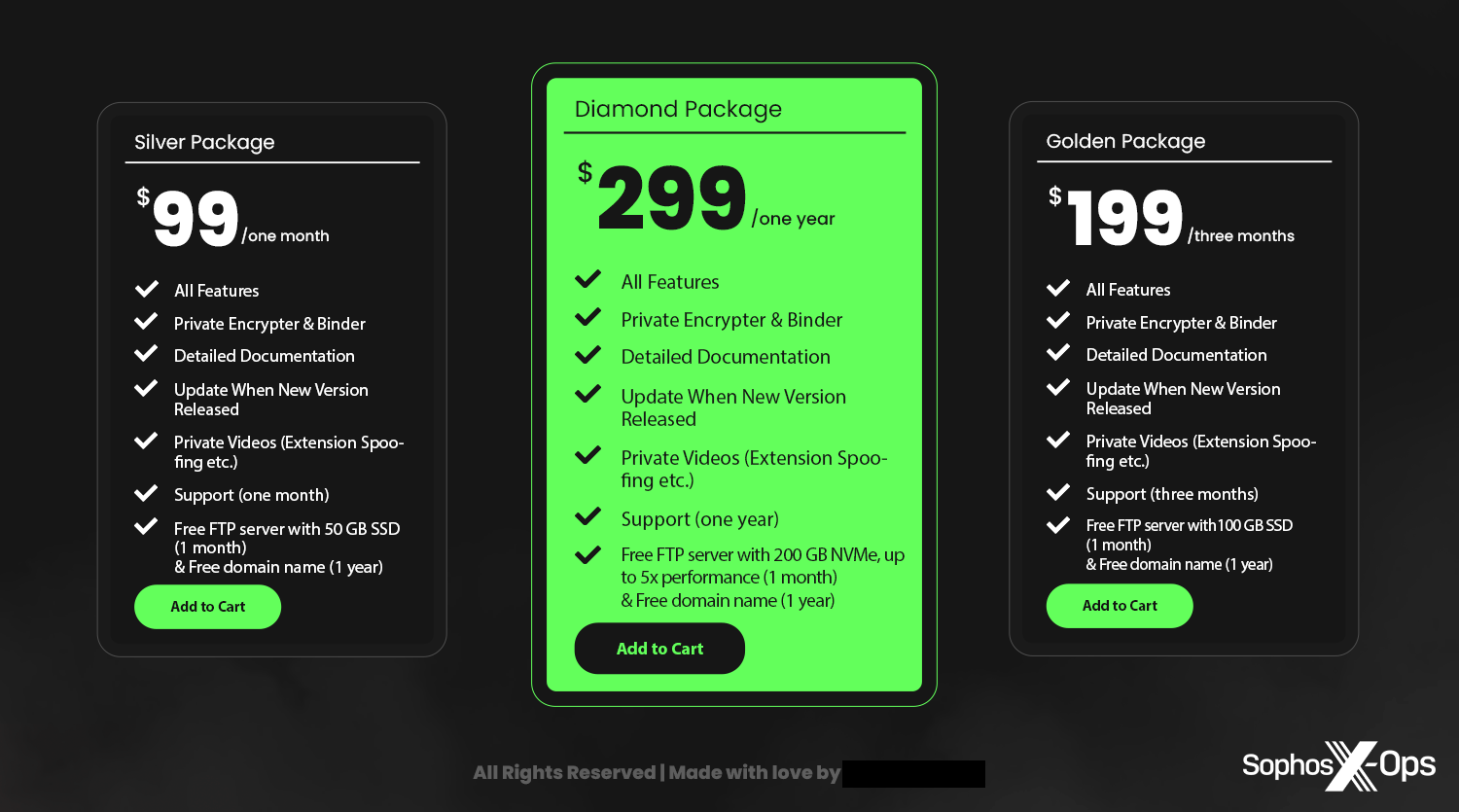
| Evil Extractor | December 2023 | On the market | $99 – $199 monthly | Unknown | Sure | Unknown | Stealer, RAT, ransomware, FTP server, crypter, persistence, self-destruct, anti-VM |
| HardShield | September 2023 | Open supply | Free | C++ | Unknown | Unknown | CBC AES128+RSA 2048, delete shadow copies, threaded, self-deletion |
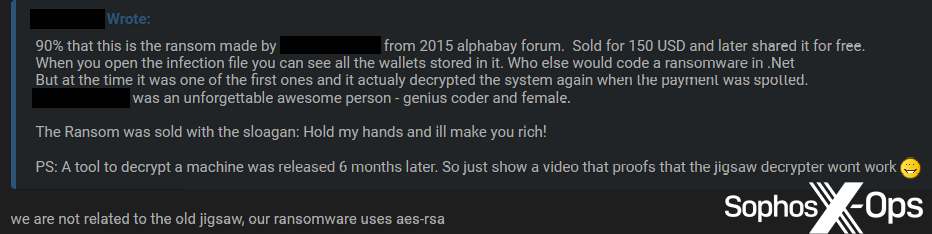
| Jigsaw | June 2023 | On the market | $500 | .NET | Unknown | A number of | Offline encryption, AES-RSA, threaded |
| Kryptina | December 2023 | On the market | $20 for single construct / $800 for supply code / free | C | Unknown | Unknown | Targets Linux, threaded, offline, AES-256 CBC |
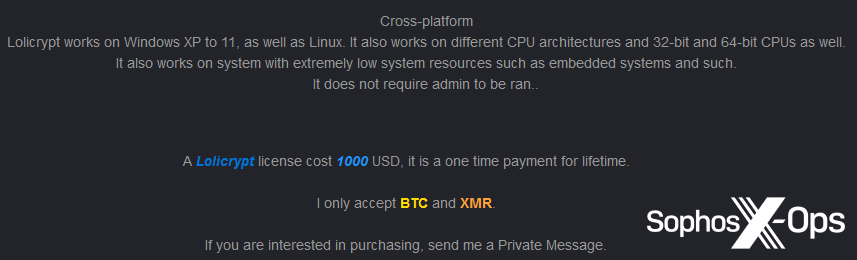
| Lolicrypt | August 2023 | On the market | $1000 | Unknown | Sure | Unknown | Intermittent encryption, chacha20, cross-platform |
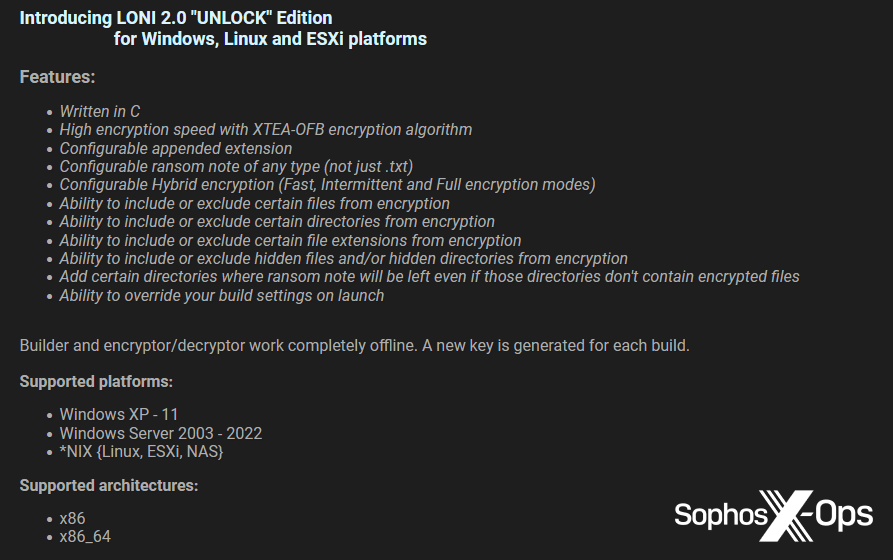
| Loni | July 2023 | On the market | $999 monthly / $9999 lifetime | C | Unknown | Unknown | Distant, delete shadow copies, self-destruct, XTEA, intermittent encryption |
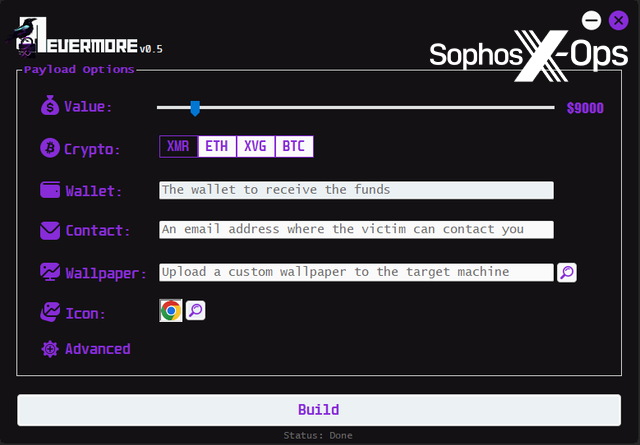
| Nevermore | October 2023 | On the market | $250 | C# | Unknown | Defender | AES-256, threaded, stealer, distinctive payloads, |
| RansomTuga | June 2023 | Open supply | Free | C++ | Unknown | A number of | Stealer |
| Yasmha | February 2024 | On the market | $500 | C# | Unknown | A number of | N/A |
| Ergon | September 2023 | On the market | 0.5 BTC per compile, 2.5 BTC for supply code | Unknown | Sure | Unknown | Customized builds, help, RaaS mannequin |
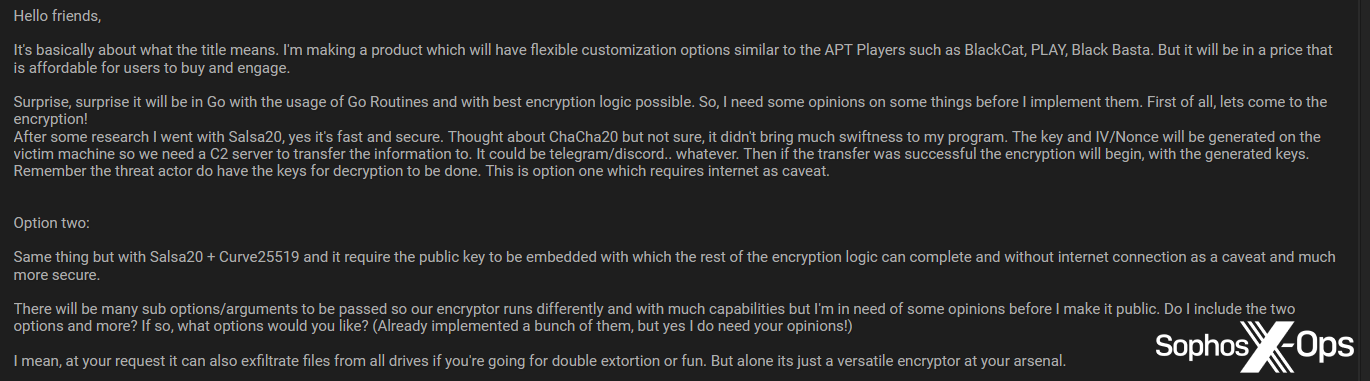
| Unnamed ransomware | September 2023 | In improvement | N/A | Go | N/A | Unknown | Salsa20 encryption |
| Unnamed ransomware | July 2023 | On the market | $1000 | C++ | Unknown | Unknown | Threaded, delete shadow copies, self-delete, partial and full encryption |
| Unnamed ransomware | January 2024 | On the market | $60 | Unknown | Unknown | Unknown | Buyer offers RSA keys, ransom word, desktop background, and so forth |
| Unnamed ransomware | February 2024 | On the market | $50 | Python | Unknown | Unknown | Unknown |
| Unnamed ransomware | June 2023 | On the market | $500 | Unknown | Unknown | Unknown | No decryption key |
Desk 1: An outline of the off-the-shelf junk-gun ransomware varieties we noticed on 4 prison boards, between June 2023 and February 2024
Low-cost and cheerless
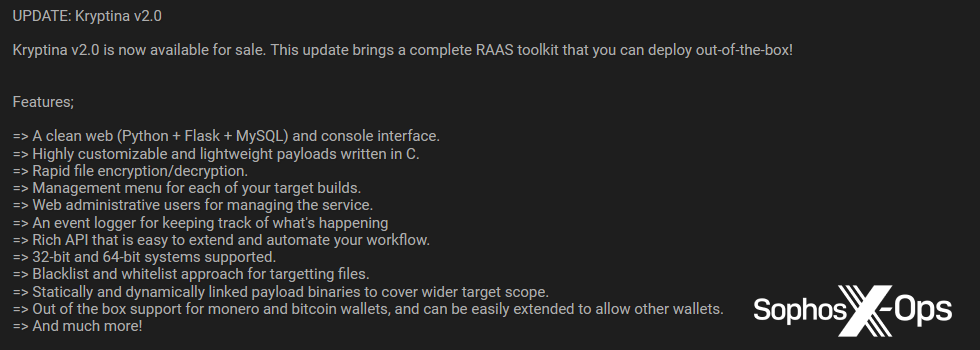
Of the 19 varieties we discovered, one had no value listed, two had been open-source, and two had been below lively improvement and due to this fact had no value listed. Costs for the remaining 14 ranged from $20 (for a single construct of Kryptina; we later famous that the Kryptina developer launched their ransomware at no cost after struggling to make gross sales) to 0.5 BTC, or roughly $13,000 on the time of the posting.
Determine 1: One of many adverts for Kryptina
Determine 2: A screenshot exhibiting a construct of Kryptina, offered by the vendor as a part of their promotional supplies
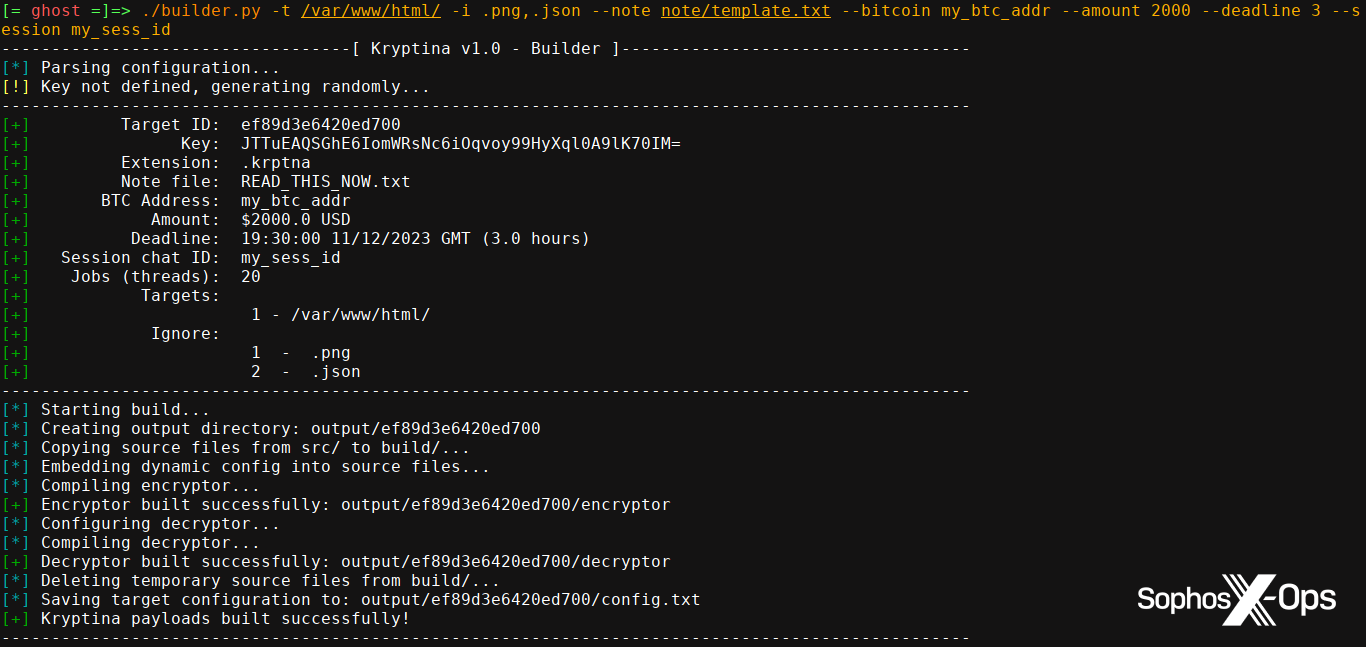
Determine 3: An advert for an unnamed junk-gun ransomware written in C++, provided on the market on a prison discussion board
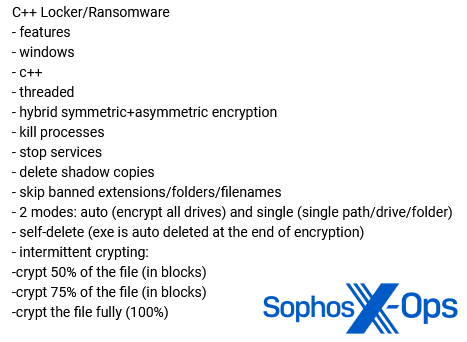
That 0.5 BTC value (for a single construct of Ergon) seems to be one thing of an outlier, nonetheless. The median common value throughout all varieties was $375, and the mode was $500. The imply common was $1,302 together with Ergon, however $402.15 with out. That’s notably low-cost, on condition that some RaaS associates reportedly pay as much as 1000’s of {dollars} for entry to kits (though word that some kits price a lot much less).
Determine 4: A publish selling the Ergon ransomware. Be aware the declare that Ergon “has been utilized in a number of assaults with extremly [sic] excessive success price [emphasis in original].” We’ll cowl in-the-wild junk-gun ransomware assaults shortly
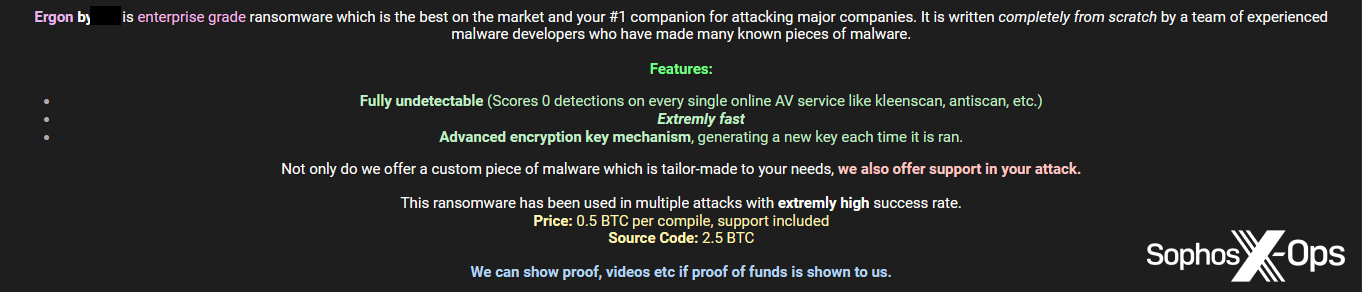
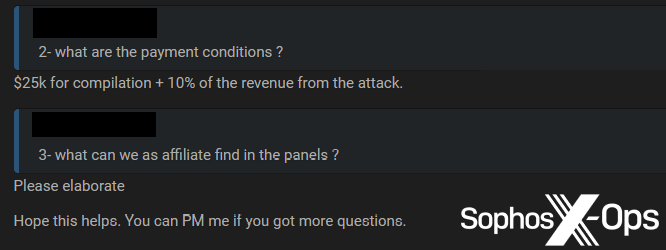
Determine 5: In addition to its excessive value, Ergon was additionally an outlier in that its developer(s) requested for 10% of any income from assaults; we didn’t see this type of stipulation wherever else throughout our analysis
Most junk-gun ransomware was accessible for a single, one-off value. Solely three adopted any type of subscription mannequin (Diablo, with licences at $50 monthly; Evil Extractor, at $99 – $199 monthly relying on the chosen ‘plan’; and Loni, at $999 monthly or $9,999 for a lifetime licence). Each Kryptina and Ergon additionally provided supply code at a premium price, relative to the worth of a single construct ($800 for Kryptina, and a couple of.5BTC, or about $39,000, for Ergon).
Determine 6: A publish promoting the Diablo ransomware, with a subscription value of $50 monthly
Determine 7: The accessible ‘packages’ for Evil Extractor
Curiously, a minimum of two examples of junk-gun ransomware – Diablo and Jigsaw – use names related to historic ransomware households. Diablo was a variant of Locky in 2017, and Jigsaw (beforehand BitcoinBlackmailer) was launched in 2016. This can be a coincidence, and neither vendor said that their ransomware was linked to those earlier households. That didn’t cease some customers questioning if there was a connection, significantly within the case of Jigsaw – though the vendor denied this.
Determine 8: The Jigsaw vendor/developer denies being related to “the outdated jigsaw” ransomware
It’s potential that these risk actors are intentionally utilizing the names of earlier, well-known ransomware to profit from ‘model recognition’ and provides their junk gun variants an air of ‘legitimacy’ – even if they could be counterfeits.
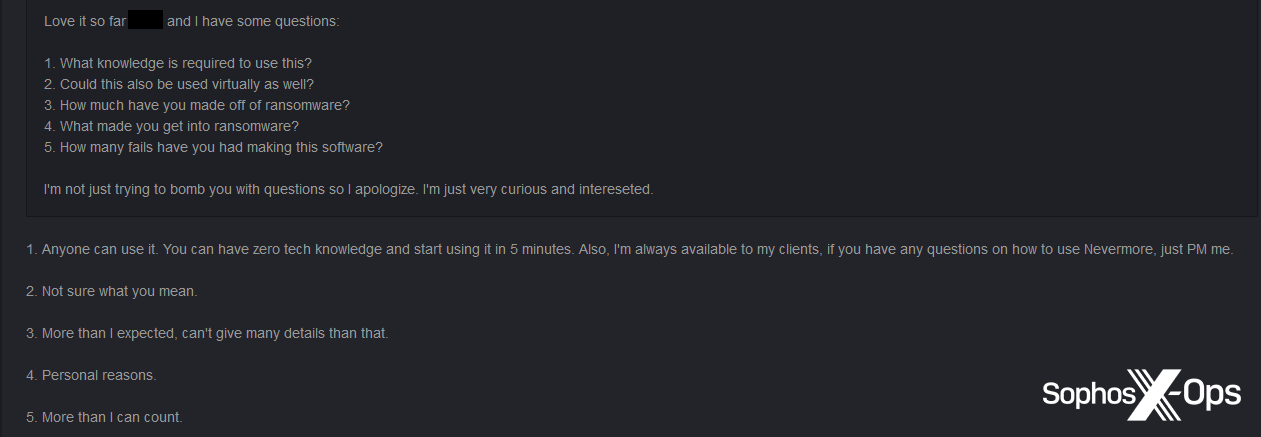
In any case, it seems that a minimum of some junk-gun ransomware builders are getting cash from their merchandise. Whereas the Kryptina developer admitted that that they had struggled to show a revenue, the Nevermore developer stated that that they had made “greater than I anticipated” from ransomware.
Determine 9: The Nevermore developer solutions some questions from a discussion board consumer, together with how a lot cash they’ve comprised of ransomware
It’s value noting at this juncture that some junk-gun ransomware could be a rip-off. We’ve beforehand reported on criminals defrauding and hacking one another in a wide range of methods on marketplaces – together with ‘rip and run’ scams and backdoored malware – and it’s fully potential that a few of the variants we talk about listed below are schemes on this vein. We solely discovered one allegation of this nature, nonetheless.
Determine 10: A screenshot of an unnamed junk-gun ransomware, posted to a discussion board as a part of an inventory. Regardless of the window title of “Ransomware-As-A-Service”, we didn’t observe any indication of any widespread RaaS-type income fashions or options with this product, and it was provided at a standalone value of $200
Determine 11: A consumer alleges that this ransomware is a rip-off and that they had been defrauded to the tune of $149 USDT (Tether)
Nonetheless, even associates of outstanding ransomware households, working below widespread RaaS fashions, run the chance of being scammed by RaaS operators. Standalone junk-gun ransomware could due to this fact be the lesser of two evils within the minds of some less-experienced risk actors, as it might probably present them with extra independence and management.
Languages
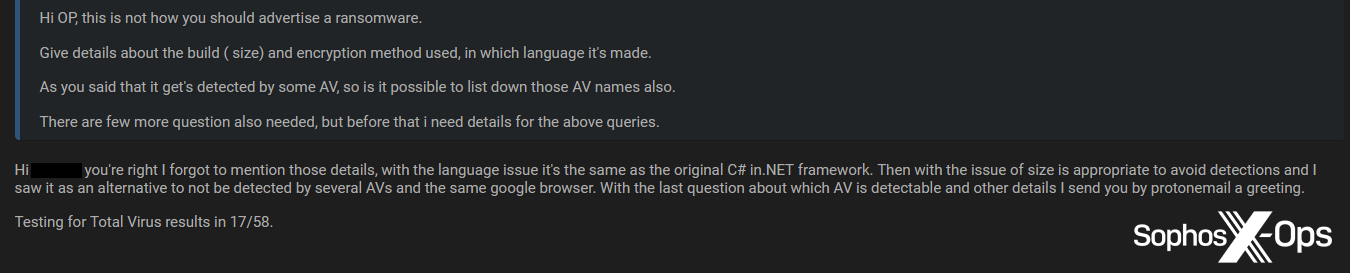
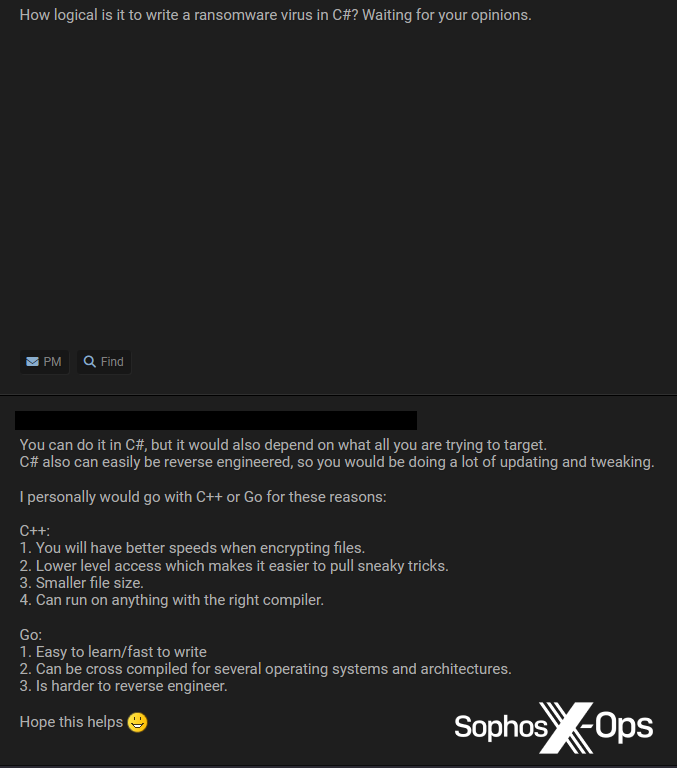
12 of the 19 adverts included particulars in regards to the improvement language and/or framework, both within the preliminary publish or in subsequent discussions. Curiously, .NET/C# was the preferred (5 variants), with C++ accounting for 3, two in C, and Python and Go one every.
Determine 12: A consumer solicits improvement recommendation for an ongoing ransomware venture written in Go. Be aware the aspiration to make the ransomware “just like the APT Gamers corresponding to BlackCat, PLAY, Black Basta”
Determine 13: Most junk-gun ransomware we noticed, nonetheless, appeared to have been written in C#/.NET
This is able to appear to be at odds with ‘conventional’ malware and ransomware (usually written in C or C++), and extra fashionable strains (a number of ransomware households, together with BlackCat and Hive, shifted to Rust and Go). It’s not fully shocking, nonetheless; C# and .NET are inclined to have a shallower studying curve than many programming languages and frameworks, and will due to this fact be extra enticing to much less skilled builders.
Maybe consistent with this, nearly all of the junk-gun ransomware we noticed – except for Evil Extractor – lacked the slick graphics and branding related to extra outstanding ransomware. Within the majority of instances, logos and interfaces had been crude and amateurish (and a few varieties had been intentionally unbranded and unnamed, and so had no logos in any respect).
Determine 14: The Lolicrypt brand
Options
The marketed capabilities of junk-gun ransomware diverse extensively. We noticed a variety of cited encryption strategies, though AES-256 and/or RSA-2048 had been, unsurprisingly given their ubiquity, the preferred, showing in seven of the ten listings by which risk actors offered this element. Nonetheless, we additionally noticed some comparatively uncommon algorithms, together with Chacha20, XTEA, and Salsa20.
Determine 15: A promotional publish for Loni, referring to the usage of the XTEA cipher. Loni was notable for the quantity of technical info offered about its options
4 varieties (Evil Extractor; CatLogs; Nevermore; and RansomTuga) bundled different capabilities, corresponding to infostealing and/or keylogging, together with ransomware performance. With reference to ransomware-related options, solely three varieties referred to deletion of quantity shadow copies (a well known ransomware tactic), which was considerably shocking – though six talked about multi-threaded encryption (one other quite common tactic, which will increase the pace of encryption).
Determine 16: A publish promoting the CatLogs junk-gun ransomware, which bundles a number of different options
Just one selection, Kryptina, was described as particularly focusing on Linux working techniques, though each the Lolicrypt and Loni builders said that that they had launched cross-platform capabilities or Linux-specific variants.
Determine 17: The Lolicrypt developer claims that their ransomware has cross-platform capabilities
Going in opposition to the grain, solely Loni claimed to have distant encryption capabilities. This maybe illustrates how low-quality and crude most junk-gun ransomware is, being restricted to native encryption, whereas many main ransomware households are able to distant encryption.
Simply two adverts (an unnamed selection, and Evil Extractor) talked about any form of anti-VM or anti-debugger options.
Determine 18: A function listing for an unnamed junk-gun ransomware consists of references to “Anti Digital Machine” and “Anti Debugger” capabilities
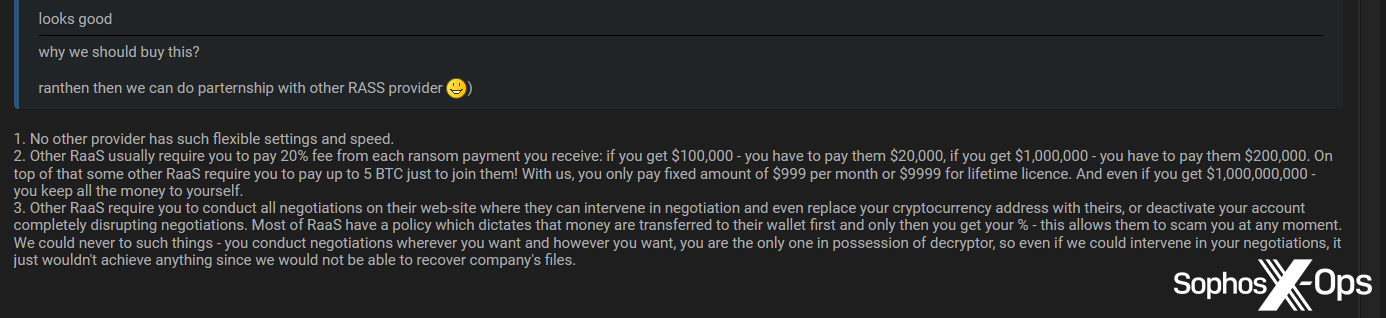
We did word that some junk-gun ransomware builders seem to have ambitions to ultimately evolve their tasks into extra complicated choices. The Loni developer, for instance, argued that their ransomware is superior to RaaS schemes as a result of there’s no have to profit-share, pay affiliate becoming a member of charges, or run the chance of RaaS operators interfering with negotiations and funds.
Determine 19: The Loni developer makes an argument for his or her product versus RaaS schemes. Be aware the reference to RaaS operators scamming associates, which we alluded to earlier
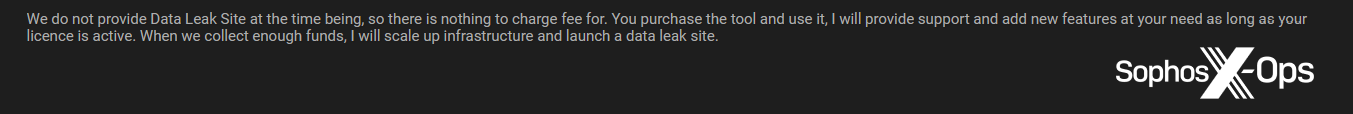
Nonetheless, the developer later talked about that after they have collected sufficient funds, they are going to “scale up infrastructure and launch a knowledge leak website” – thereby making a type of hybrid of a traditional RaaS infrastructure and junk-gun ransomware.
Determine 20: The Loni developer reveals ambitions to later launch a knowledge leak website, in addition to promising consumers “help and…new options”
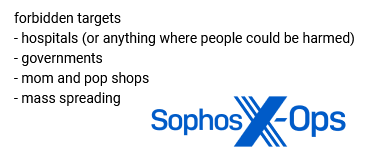
We additionally noticed an advert which appeared to imitate a few of the ‘affiliate guidelines’ stipulated by outstanding ransomware households. In a single publish, for an unnamed junk-gun ransomware, the developer listed “forbidden targets”, together with hospitals and governments. Nonetheless, this advert seemed to be for standalone ransomware, so it’s unclear how these guidelines can be enforced.
Determine 21: A junk-gun ransomware advert specifies “forbidden targets”
Within the wild?
It’s troublesome to evaluate the extent to which most junk-gun ransomware has been utilized in real-world assaults. Considered one of its main promoting factors is that little or no supporting infrastructure is required, and this consists of leak websites – so there is no such thing as a central supply of data for researchers and investigators to watch. Furthermore, if consumers are focusing on small companies and people, such incidents are unlikely to be publicized to the identical extent as these involving higher-profile organizations.
Menace actors are additionally unlikely to debate assaults on ‘public’ boards, significantly in the event that they had been straight concerned in these assaults. And it’s troublesome to acquire technical info, corresponding to hashes and different IOCs, with out both buying the ransomware or investigating identified incidents – so it’s laborious to find out if we’ve seen any of those varieties earlier than, below totally different names or identities.
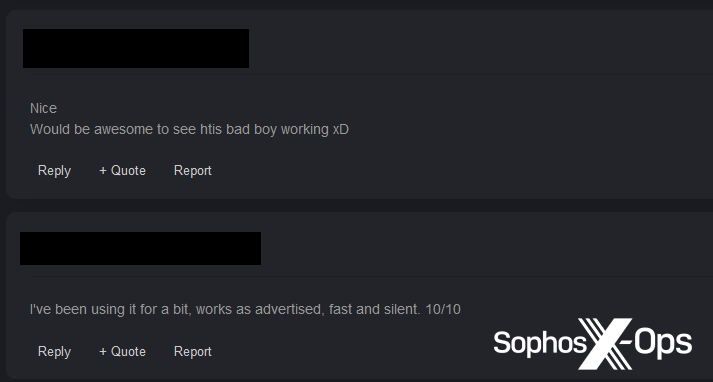
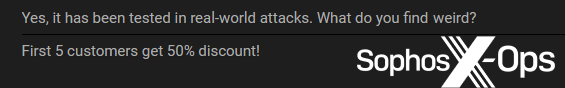
Nonetheless, we do know that risk actors have used Evil Extractor – to our data, the one instance that has obtained any in-depth protection – in real-world assaults. We additionally noticed claims – two from sellers, one from a purchaser – that three variants (Ergon, Loni, and Lolicrypt) have been used within the wild, however we had been unable to acquire any additional info.
Determine 22: A Lolicrypt purchaser claims that they’ve “been utilizing it for a bit, works as marketed”
Determine 23: The Loni developer states that Loni “has been examined in real-world assaults”
Detections
When risk actors promote malware on prison boards, they usually embrace detection charges from on-line scanners, both within the type of a quantity or a screenshot. Whereas these outcomes are virtually at all times associated to static, moderately than dynamic, detections, the prison neighborhood usually regards them as one thing of a high quality benchmark. Menace actors could use a zero-detection price (popularly often called ‘FUD’: ‘absolutely undetected’ or ‘absolutely undetectable’), for instance, as a promoting level, even when that determine doesn’t essentially imply a lot within the context of real-world assaults.
Six of the 19 adverts referred to some type of detection – three mentioning Home windows Defender particularly (both within the context of detections or bypasses), and three referring to detections by a number of safety merchandise in on-line scanners.
Determine 24: The Yasmha developer responds to criticism of their preliminary advert by together with particulars in regards to the language and detection price
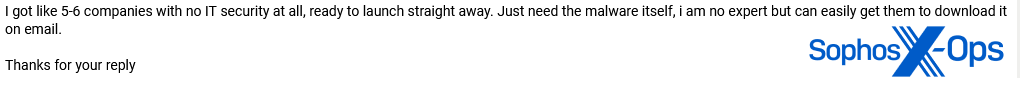
Nonetheless, as we famous earlier, even a comparatively excessive detection price isn’t essentially a dealbreaker in relation to junk-gun ransomware. Small companies and people could not at all times have safety merchandise, or could not have configured them accurately, or could not undertake finest apply when an alert is triggered – and plenty of risk actors know this.
Determine 25: A consumer claims to be focusing on “5-6 corporations with no IT safety in any respect”
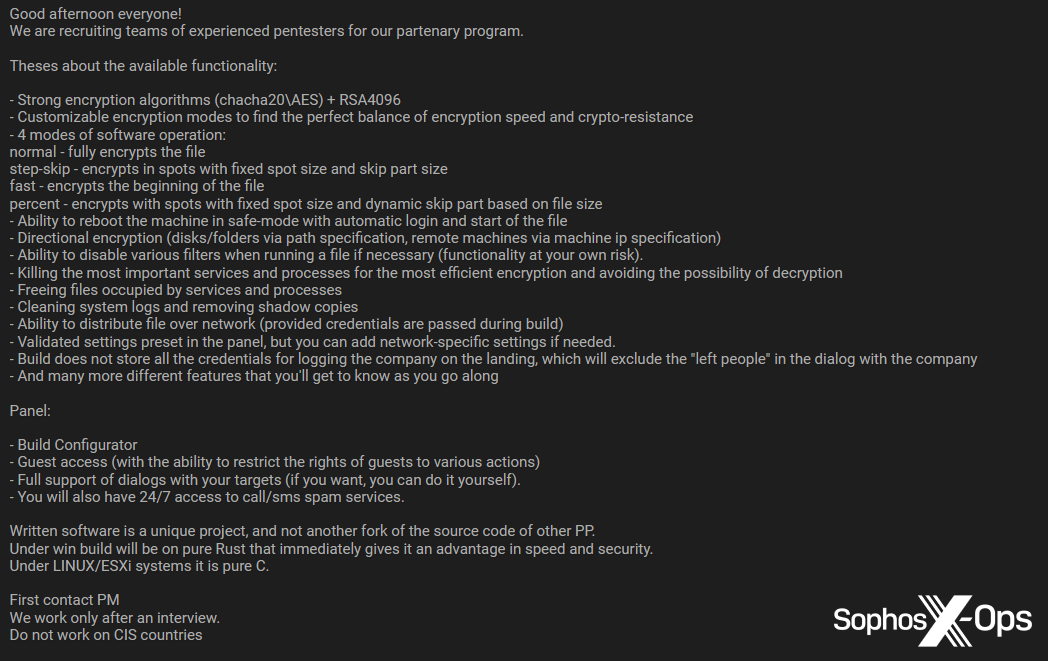
Along with comparatively unknown junk-gun ransomware, we additionally discovered better-known ransomware on the boards, albeit all comparatively new or lower-tier households. We grouped these examples into three classes: builders or supply code on the market or distribution; recruitment alternatives; and requests for help with improvement.
| Identify | Date posted | Kind | Value |
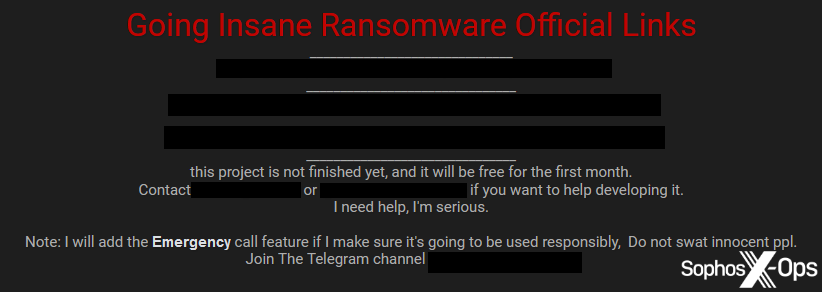
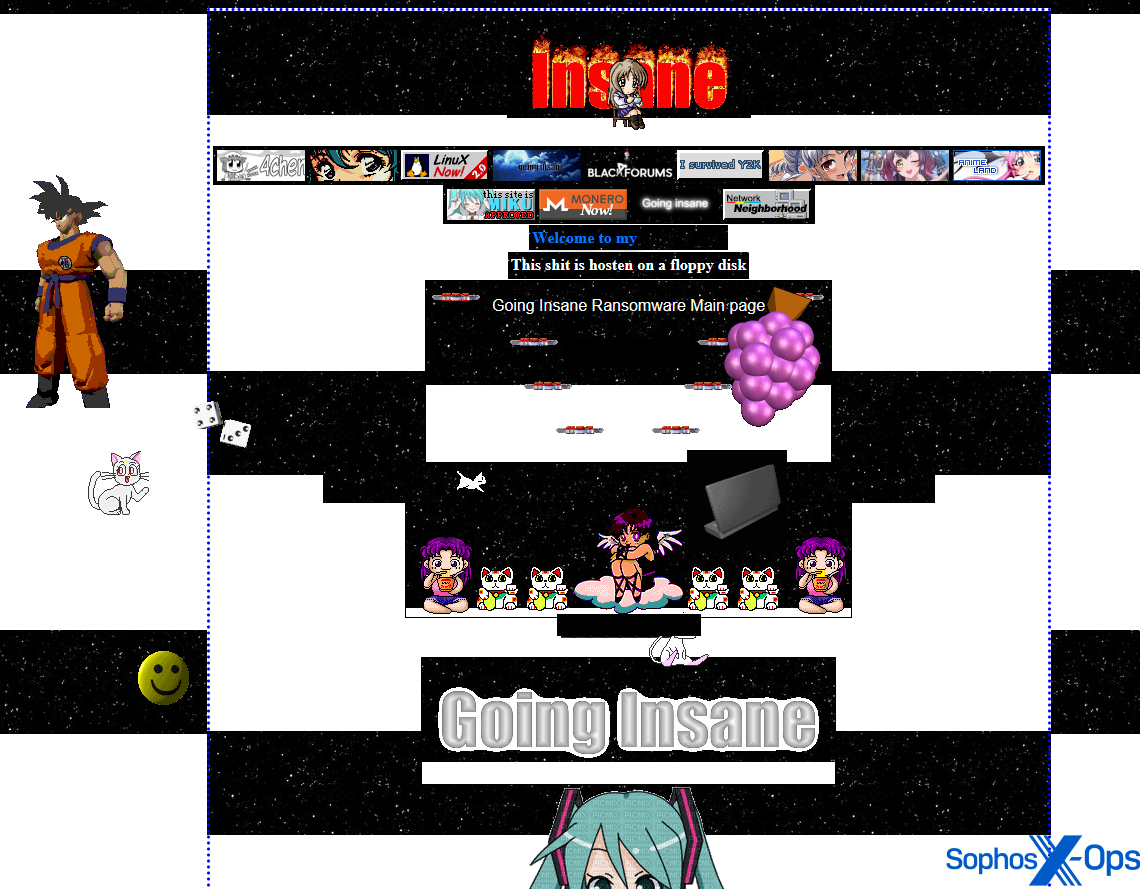
| Insane | January 2024 | Growth request / affiliate recruitment | N/A |
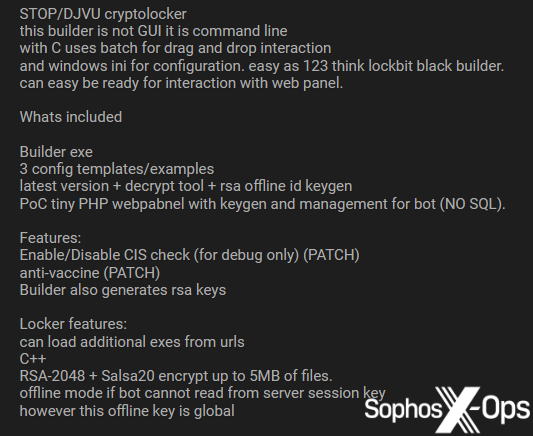
| DJVU | January 2024 | Builder on the market | Unknown |
| Zeppelin | January 2024 | Supply code | Unknown |
| Endurance | November 2023 | Affiliate recruitment / builder on the market | $850 |
| Chaos | June 2023 | Builder on the market | Unknown |
| Qilin | September 2023 | Affiliate recruitment | N/A |
| qBit | September 2023 | Builder on the market / improvement request | Unknown, launched at no cost December 2023 |
| Black Snake | June 2023 | Affiliate recruitment | N/A |
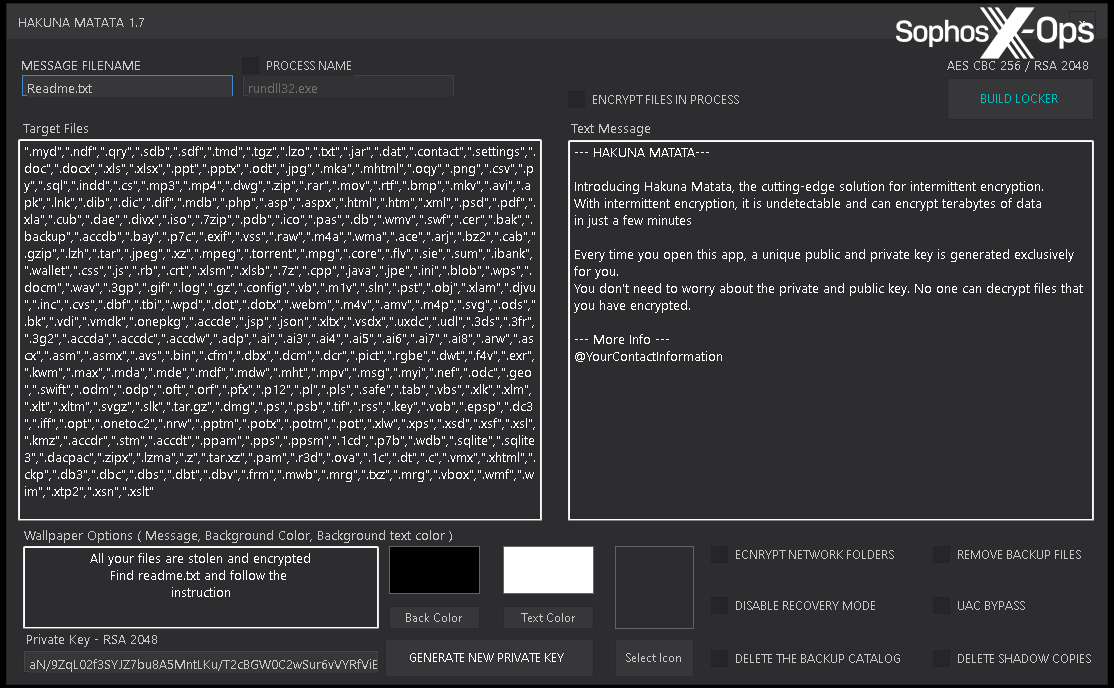
| Hakuna Matata | July 2023 | Builder on the market/distribution | Unknown |
| LMAO | June 2023 | Builder on the market/distribution | Unknown |
| Unknown | July 2023 | Affiliate recruitment | N/A |
Desk 2: Identified ransomware on the 4 prison boards we investigated
Be aware that we embrace ‘yasmha’ within the junk-gun ransomware part, moderately than this one, as a result of the poster explicitly said that it’s a variant of Yashma ransomware (the spelling mistake seems to be deliberate, or a minimum of constant throughout a number of posts). Conversely, the risk actors providing builders and supply code for DJVU (a variant of STOP), Zeppelin, Endurance, Chaos (the predecessor to Yashma), qBit, Hakuna Matata, and LMAO (a variant of Chaos) didn’t state that their merchandise are novel, personalized variants.
Determine 26: An advert for DJVU ransomware on a prison discussion board
Determine 27: A screenshot of the Hakuna Matata ransomware builder, which was provided on the market/distribution on a discussion board
Determine 28: A promotional publish for Insane ransomware, together with a request for improvement help
Determine 29: Insane’s leak website, with a notably garish old-school aesthetic
Determine 30: A recruitment advert by the Qilin ransomware gang. Be aware the usage of the time period “pentesters”, which risk actors usually use as a euphemism for associates and/or IABs on prison boards
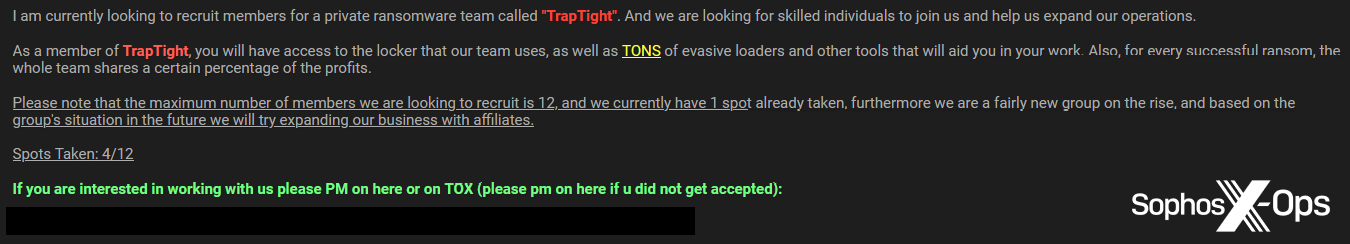
Lastly, we additionally noticed a recruitment marketing campaign by an as-yet-unknown ransomware household, TrapTight.
Determine 31: A recruitment marketing campaign by a brand new ‘start-up’ ransomware household, TrapTight
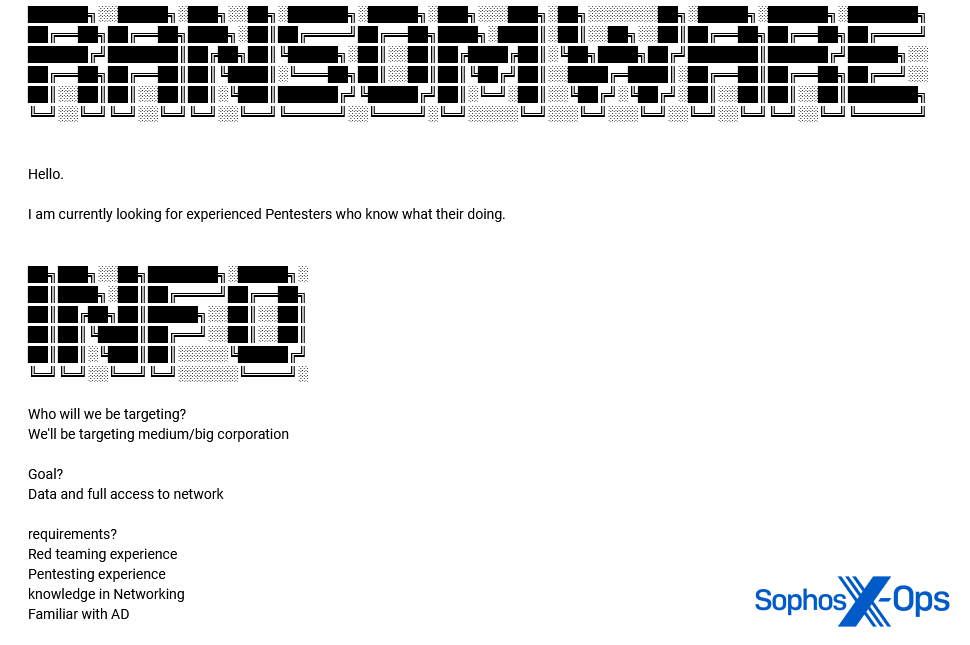
And one other by an unnamed ransomware gang:
Determine 32: An unnamed ransomware household seeks “pentesters” to focus on “medium/massive company” [sic]
Menace actors on lower-tier prison boards due to this fact appear to have a number of choices in relation to getting concerned in ransomware. The most cost effective, commonest, and most easy route seems to be the ‘self-starter’ method: buying junk-gun ransomware for a one-off value, and deploying it as they see match. Alternatively, risk actors may buy a builder for a better-known ransomware variant – one thing that has been tried and examined already in real-world assaults.
Then again, if a risk actor is trying to develop ransomware themselves, or to hitch an affiliate scheme, however is just not expert or skilled sufficient to use to the large leagues, they will search employment with identified secondary ransomware households, probably as a precursor to becoming a member of better-known schemes. Or, if that’s an excessive amount of of a stretch, they might apply to hitch a brand-new household like TrapTight.
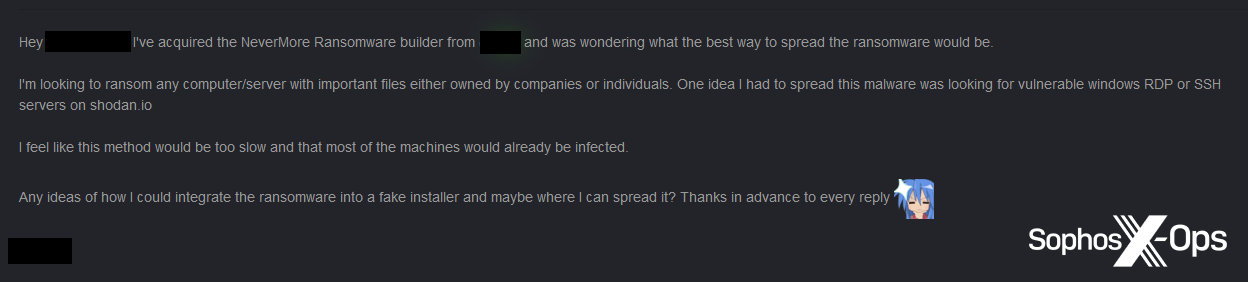
Whereas it’s usually troublesome to establish if risk actors have used junk-gun ransomware within the wild, it’s clear that some have ambitions to take action. For example, one particular person claimed to have purchased the Nevermore builder, and was trying to “ransom any laptop/server with essential information both owned by corporations or people.” The risk actor went on to say that they had been contemplating trying on Shodan – a search engine which indexes service banners, permitting customers to seek out specified sorts of units and providers – to determine weak RDP and SSH servers, an method just like that an IAB would possibly take.
Determine 33: A consumer seeks to unfold the Nevermore ransomware
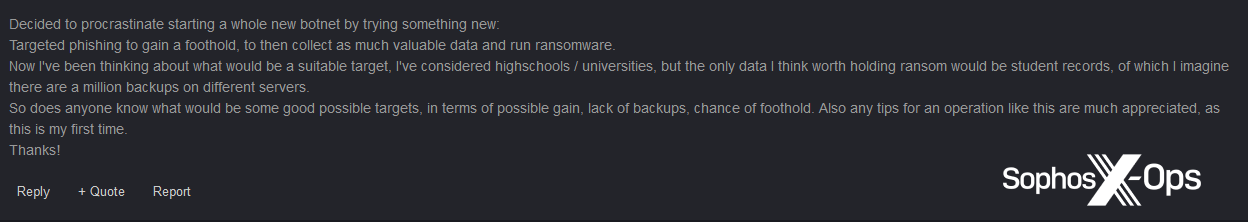
This curiosity in goal choice is one thing we noticed elsewhere, too; one consumer sought recommendation on how you can determine “an acceptable goal…I’ve thought of highschools [sic] / universities” and requested for recommendations on “potential targets, when it comes to potential achieve, lack of backups, likelihood of foothold.”
Determine 34: A discussion board consumer asks for recommendations on figuring out targets
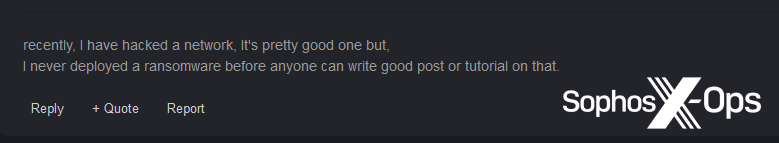
One other consumer stated that that they had already compromised a community, however had “by no means deployed a ransomware [sic] earlier than” and requested different discussion board customers for recommendation or a “tutorial.”
Determine 35: After compromising a community, a consumer confesses that they don’t know how you can deploy ransomware
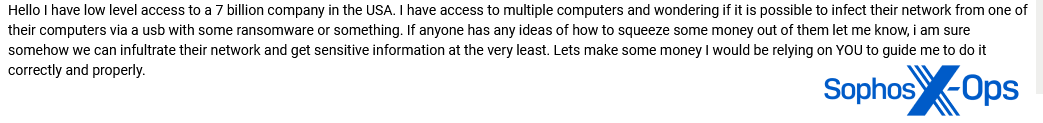
A consumer on one other discussion board had an identical difficulty:
Determine 36: A consumer claims to have entry to an organization, however asks for help on distributing ransomware
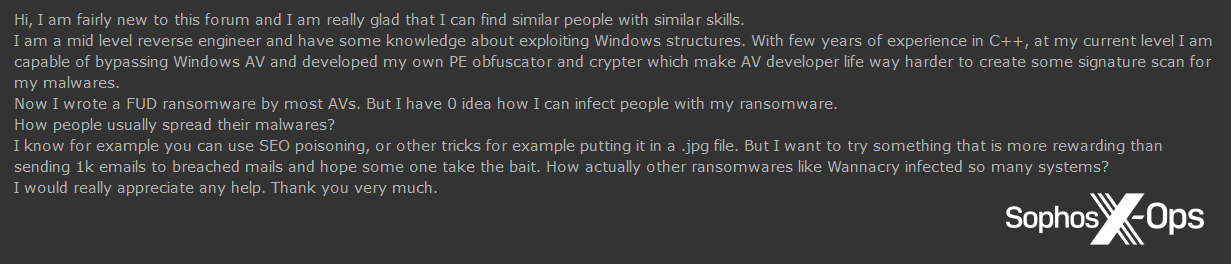
Determine 37: A consumer (who claims to be comparatively educated) asks for assistance on how you can “infect individuals with my ransomware”
With regards to steering, we noticed a number of customers requesting and sharing copies of so-called “ransomware manuals”, together with guides written by Bassterlord, a outstanding ransomware operator and IAB, and the “Conti manuals”, leaked in 2021. Evidently, such customers are in search of to be taught from, and emulate, outstanding ransomware actors.
Determine 38: A consumer shares a duplicate of one in every of Bassterlord’s manuals
Determine 39: A consumer confesses to being “confused” about how you can configure ransomware and asks for a handbook
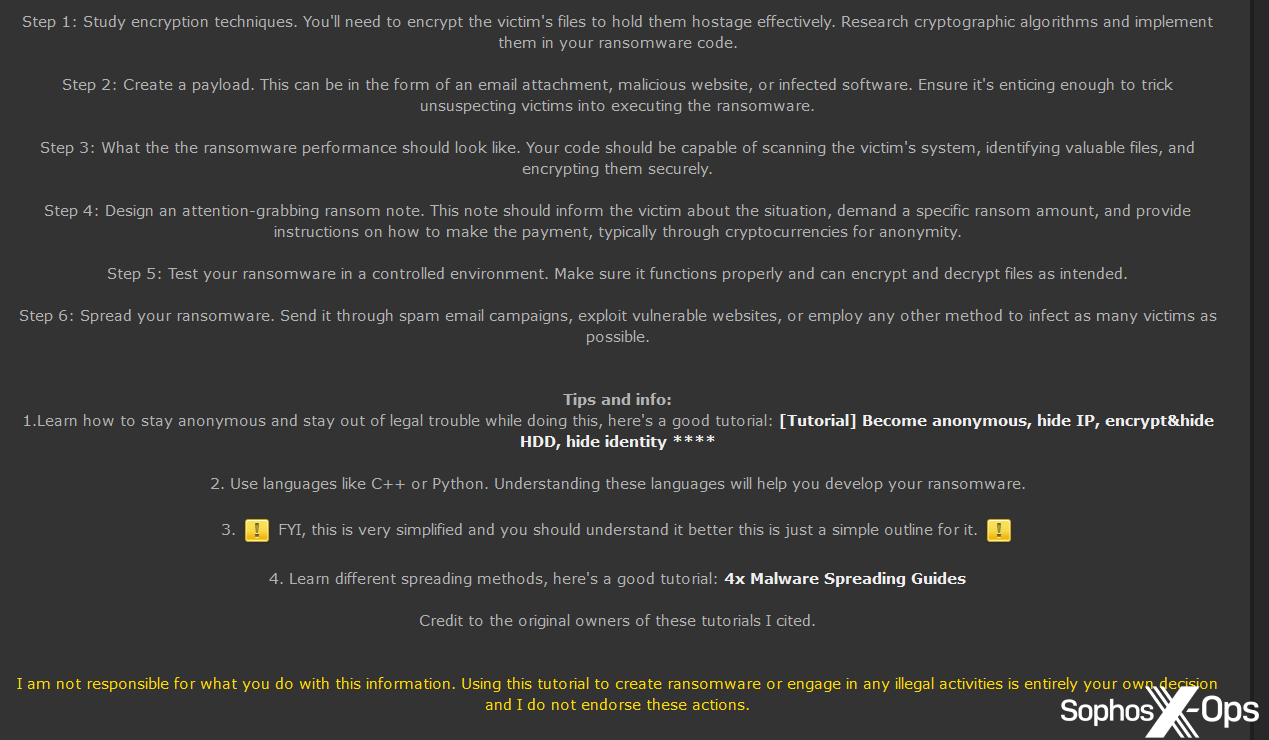
In different instances, customers created and shared their very own guides:
Determine 40: A consumer shares their very own information on growing and spreading ransomware
Some customers explicitly advocated focusing on small companies and people, and sought recommendations on how you can contact them after ransomware deployment; how a lot cash to ask for and in what cryptocurrency; and how you can launder the proceeds.
Determine 41: A consumer seeks recommendation on how you can goal small companies
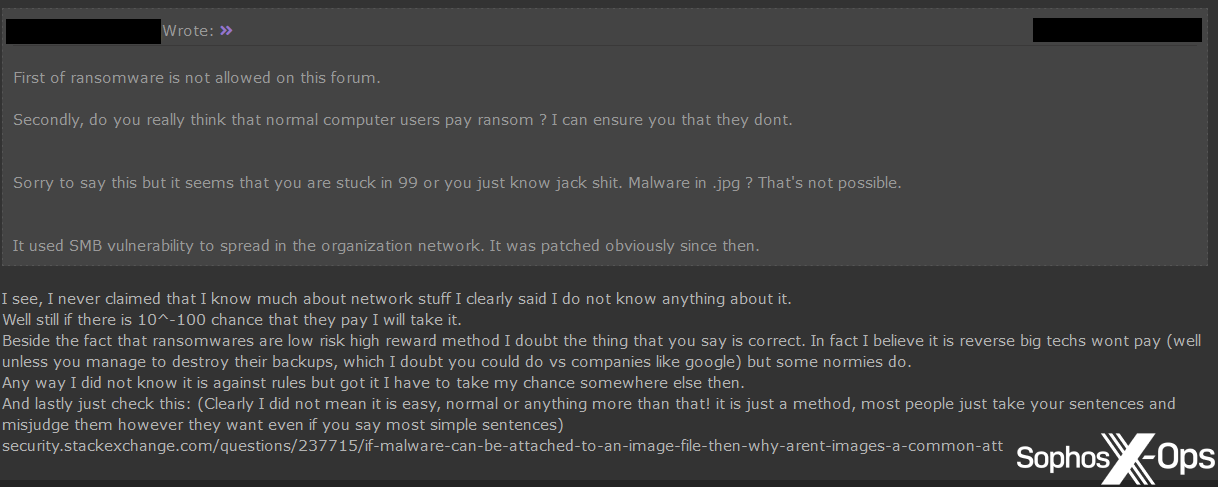
One other consumer, in response to a peer contending that “regular laptop customers” wouldn’t pay ransoms, argued: “I consider it’s reverse [sic]…massive techs wont [sic] pay…however some normies do.”
Determine 42: As a part of a spirited debate on a prison discussion board, a consumer argues that “massive techs wont [sic] pay…however some normies do”
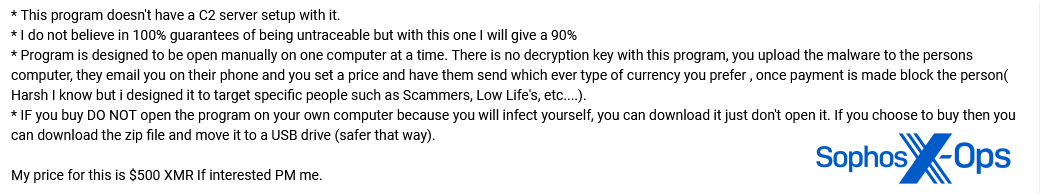
One ransomware developer took a extra aggressive method. Of their advert, they famous that “there is no such thing as a decryption key…as soon as fee is made block the particular person.” They go on to say that this ransomware is “designed…to focus on particular individuals corresponding to Scammers, Low Life’s [sic], and so forth…”
Determine 43: A junk-gun ransomware developer notes that their product consists of no risk of decryption – in different phrases, victims pays, however won’t be able to get well their information
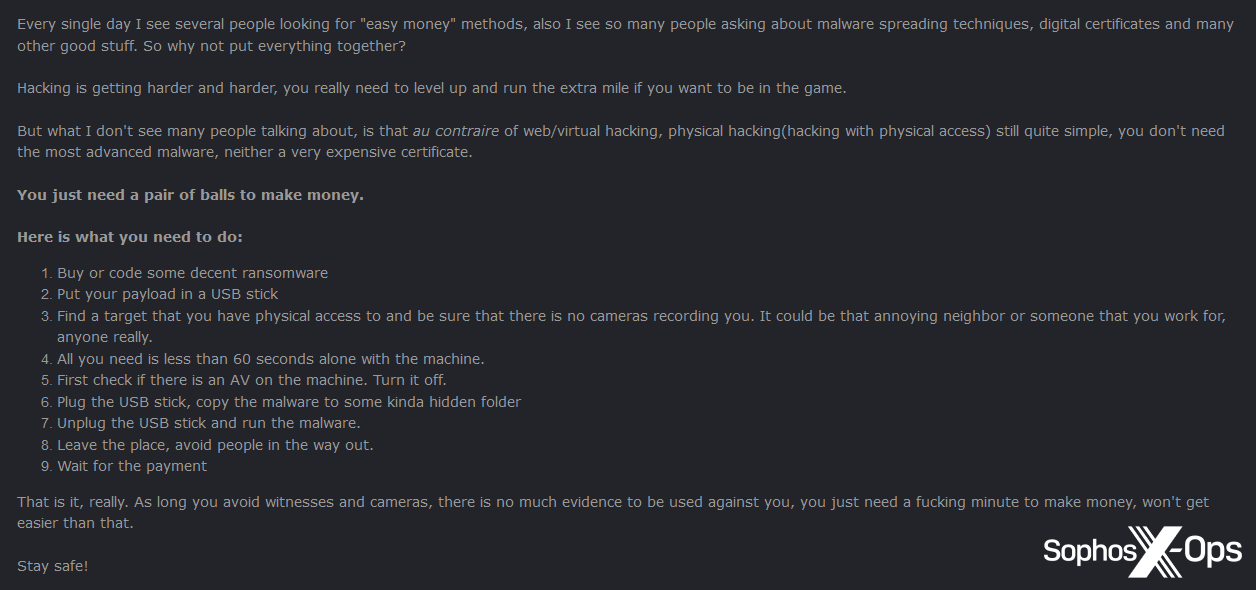
In one other significantly fascinating publish, the developer behind Nevermore prompt another method to orthodox an infection methods: bodily entry. They advocated placing ransomware on a USB stick; acquiring entry to a tool (“it could possibly be that annoying neighbor or somebody that you simply work for”); turning off any safety merchandise; after which executing the ransomware. “So long as you keep away from witnesses and cameras”, the risk actor went on to say, “there is no such thing as a [sic] a lot proof for use in opposition to you.”
Determine 44: The Nevermore developer suggests combining bodily entry with ransomware for “straightforward cash”
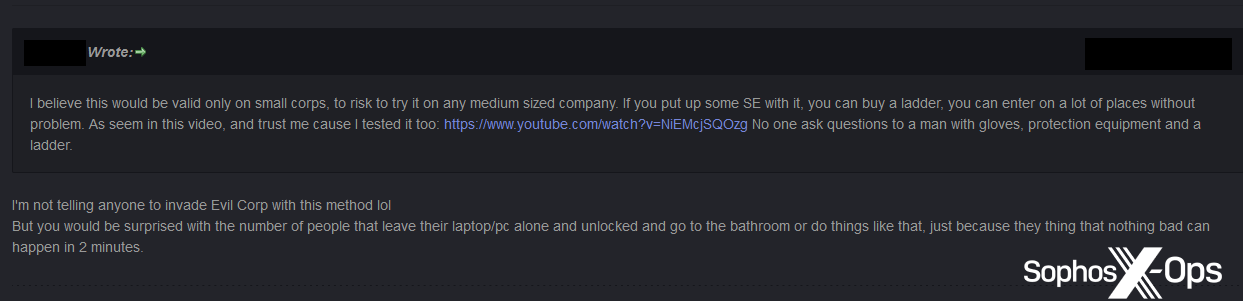
A consumer commented that this method “can be legitimate solely on small corps, [too risky] to strive it on any medium sized firm”, and prompt combining this tactic with social engineering to achieve entry to premises.
The Nevermore developer agreed, including that “you’d be stunned with [sic] the variety of those that depart their laptop computer/computer alone and unlocked and go to the toilet.”
Determine 45: Discussion board customers talk about potential approaches for ‘bodily entry ransomware’
Whereas the boards we investigated for this analysis are frequented by lower-tier risk actors, we noticed an fascinating nuance. Under the consumers and sellers of junk-gun ransomware, there may be a good decrease tier – those that are nonetheless not but on the stage of growing their very own ransomware, however aspire to take action.
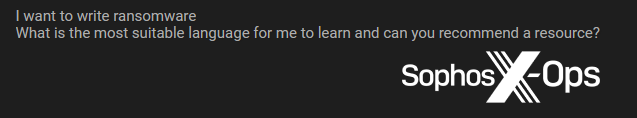
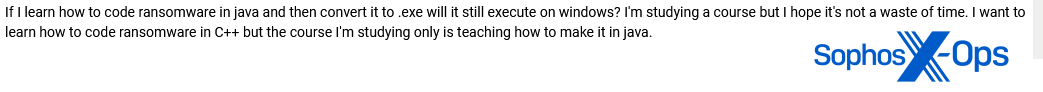
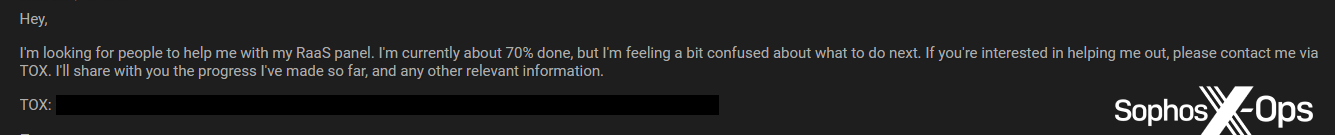
We famous a number of cases of customers soliciting recommendations on which languages to make use of, or individuals who had begun coding ransomware tasks however, as in one of many examples under, had been “confused about what to do subsequent.”
Determine 46: A consumer seeks recommendation on “essentially the most appropriate language” for growing ransomware
Determine 47: A consumer wonders if writing ransomware in Java is worth it
Determine 48: Customers debate the relative deserves of writing ransomware in C#. Curiously, we additionally noticed some customers advising others to make use of Python, though the reception to that suggestion was combined
Determine 49: A consumer asks for assist with growing their “RaaS panel”
In a number of cases we additionally noticed customers who had an concept for various tasks, however weren’t positive in the event that they had been possible.
Determine 50: A consumer solicits opinions on worm-based ransomware
In different instances, customers who had presumably overcome these hurdles to create working code had been nonetheless at a loss as to the following stage. These customers requested for recommendation on how you can licence their malware, how a lot to promote it for – and even how to promote it within the first place.
Determine 51: A consumer asks for assist in understanding how malware licencing works. One response, curiously, attracts parallels with outstanding tech corporations
Determine 52: A consumer wonders “how you can set a value for…malware”
Determine 53: This consumer was confused about how you can begin promoting their malware, not to mention set a value or determine a licencing mannequin
Whereas it’s no shock that there are ‘script kiddies’ on prison boards, this sub-tier of would-be ransomware actors remains to be noteworthy. On higher-profile, Russian-language cybercrime boards – these frequented by outstanding and prolific IABs, malware builders, and ransomware associates – the questions proven above can be at finest ignored, and at worst ridiculed. (And would possibly, in fact, fall foul of the ban on industrial ransomware posts on some main boards following the 2021 Colonial Pipeline assault – though many customers have circumvented the ban, and the extent to which it’s noticed and enforced seems to differ).
However on the boards we’ve mentioned right here, customers are much less apprehensive about revealing their ignorance, as a result of these websites cater virtually completely to less-skilled risk actors. There’s a tacit understanding that these will not be gatherings of the elite, and even of pros, however are as an alternative meant for people who aspire to develop their talents, to the purpose the place they will purchase a chunk of the pie for themselves.
Whereas a lot prison market analysis focuses, not unreasonably, on higher-tier Russian-language websites (a subject for one more article, however Russian – particularly fenya – is arguably the status language within the cybercrime underground), there’s additionally a profit to monitoring lower-tier, English-language boards. Websites like this may occasionally properly produce the following technology of risk actors. The comparatively low-quality concepts and tasks featured on them now may evolve into extra subtle threats over time, as risk actors’ capabilities and confidence develop.
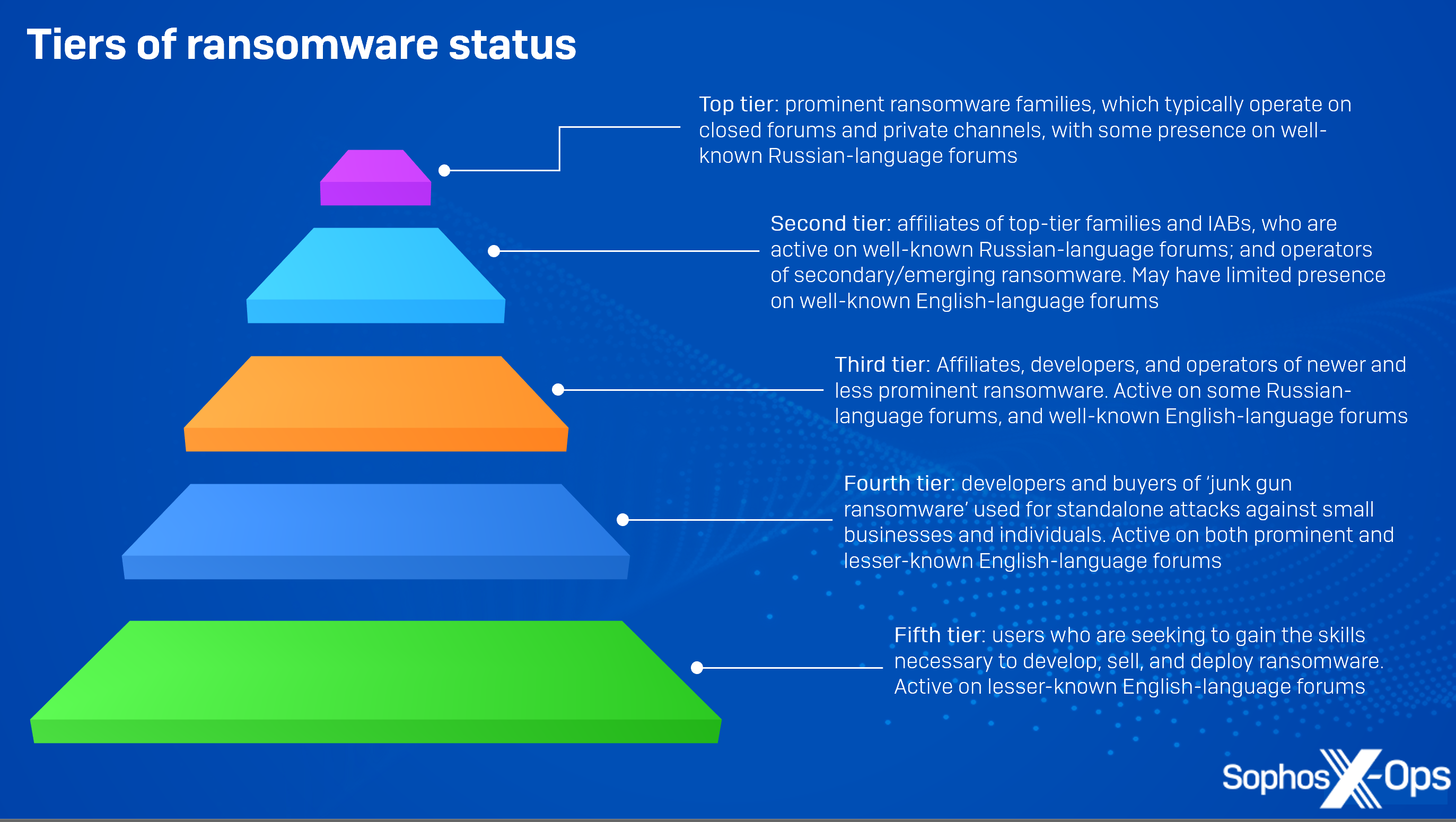
There’s additionally an argument that lower-tier English-language boards could function step one of a profession improvement path for some risk actors. The graphic under illustrates the tiers we noticed in our investigation, and the way a risk actor would possibly advance via them. Customers start by asking fundamental questions, and making an attempt to code rudimentary ransomware and malware themselves. They might then graduate to purchasing junk-gun ransomware, or growing, sharing, and promoting it – maybe, as we noticed with Loni, with ambitions to ultimately flip their tasks into extra complicated schemes.
Determine 54: An illustration of the assorted tiers of functionality, ambition, and potential profession improvement for ransomware actors
Above that tier are recruitment and improvement alternatives with rising and secondary ransomware households – which have organized RaaS schemes; tried-and-tested malware; pre-existing infrastructure; and a confirmed monitor report of real-world assaults. After which, on the apex, are the outstanding, household-name ransomware teams – the tier to which risk actors can aspire as soon as they’ve paid their dues, gained expertise, and made a reputation for themselves.
It’s due to this fact essential to view junk-gun ransomware not simply as an fascinating phenomenon in and of itself, however as a part of the broader ransomware ecosystem, and as a possible route to larger and higher alternatives for its creators, consumers, and customers. As such, it’s worthwhile monitoring junk-gun ransomware and the people concerned with it. Not solely do they pose a risk to small companies and people now, however as time goes on, a minimum of a few of them will probably turn into more and more able to inflicting harm on a bigger scale.
As a result of junk-gun ransomware appears to be a nascent improvement, we’ll be maintaining a tally of it. It might sign a transfer in the direction of an extra fracturing of the ransomware market, and maybe even impending market saturation. Or it might be that ransomware continues to shift into a number of distinct tiers: high-profile teams goal high-profile organizations, whereas the ‘scraps’ – small companies and people – are left for lower-tier risk actors. These lower-tier actors, who’re at present making and promoting junk-gun ransomware, could in time ‘transfer up the ranks’ and be recruited as builders or associates by bigger, extra skilled outfits.
To some extent, junk-gun ransomware is probably going additionally merely a mirrored image of capitalism in motion. Like some other market, provide will broaden to satisfy demand, and would-be profiteers will flock to no matter providers and merchandise are producing essentially the most cash – and carve out niches for themselves as they accomplish that. Whereas we targeted on ransomware for this analysis, it’s probably the identical story for infostealers, RATs, and cryptominers: lower-quality merchandise and actors on the backside of the pile, hoping to ultimately filter via to the highest.
What is evident, nonetheless, is that junk-gun ransomware poses distinctive challenges to small companies, the broader public, and the safety neighborhood. We noticed risk actors explicitly referring to assaults in opposition to smaller corporations and people – at the same time as they tried to find out which varieties of firm to focus on, and the way a lot ransom to demand – as a result of such targets are sometimes much less well-defended, much less knowledgeable, and fewer ready.
In the meantime, junk-gun ransomware presents the safety trade with a number of issues. It’s troublesome to acquire samples of junk-gun ransomware; to find out the extent to which it has been used within the wild; and to trace new variants. Menace actors may even typically undertake the ‘model names’ of identified ransomware households, probably to use their reputations – one thing which may trigger confusion amongst researchers. Crucially, there’s additionally much less risk intelligence about junk-gun ransomware, as a result of the boards on which it proliferates will not be at all times closely monitored by researchers – leading to an intelligence hole. After all, each companies and safety researchers should dedicate time and sources to monitoring quite a few threats, some larger precedence than others, and which differ in line with danger profiles, sectors, geography, and different components – so there’s a stability to be struck.
Nonetheless, monitoring junk-gun ransomware, and people who are, a minimum of at present, on the periphery of the ransomware ecosystem, can present priceless insights into each particular person threats, and potential future developments within the wider risk panorama. Monitoring particular ransomware variants may help to guard small companies and people now, whereas monitoring sellers, consumers, and capabilities can present perception into the event of threats and risk actors over time.