Authored by Fernando Ruiz
McAfee Cellular Analysis Staff recognized an Android backdoor applied with Xamarin, an open-source framework that permits constructing Android and iOS apps with .NET and C#. Dubbed Android/Xamalicious it tries to achieve accessibility privileges with social engineering after which it communicates with the command-and-control server to judge whether or not or to not obtain a second-stage payload that’s dynamically injected as an meeting DLL at runtime stage to take full management of the system and doubtlessly carry out fraudulent actions corresponding to clicking on advertisements, putting in apps amongst different actions financially motivated with out person consent.
The second stage payload can take full management of the contaminated system as a result of highly effective accessibility companies that have been already granted in the course of the first stage which additionally incorporates features to self-update the principle APK which signifies that it has the potential to carry out any sort of exercise like a spyware and adware or banking trojan with out person interplay. Nevertheless, we recognized a hyperlink between Xamalicious and the ad-fraud app “Money Magnet” which routinely clicks advertisements, installs apps, and different actions to fraudulently generate income whereas customers that put in it could earn factors which might be purported to be redeemable as a retail reward card. Which means that the builders behind these threats are financially motivated and drive ad-fraud due to this fact this is perhaps one of many fundamental payloads of Xamalicious.
The utilization of the Xamarin framework allowed malware authors to remain lively and with out detection for a very long time, profiting from the construct course of for APK recordsdata that labored as a packer to cover the malicious code. As well as, malware authors additionally applied completely different obfuscation methods and customized encryption to exfiltrate information and talk with the command-and-control server.
We’ve recognized about 25 completely different malicious apps that carry this risk. Some variants have been distributed on Google Play since mid-2020. The apps recognized on this report have been proactively eliminated by Google from Google Play forward of our reporting. McAfee is a member of the App Protection Alliance and an lively companion within the malware mitigation program, which goals to shortly discover Probably Dangerous Purposes (PHAs) and cease them earlier than they ever make it onto Google Play. Android customers are protected by Google Play Shield, which may warn customers of recognized malicious apps on Android gadgets. McAfee Cellular Safety detects this risk as Android/Xamalicious.
Based mostly on the variety of installations these apps might have compromised no less than 327,000 gadgets from Google Play plus the installations coming from third-party markets that frequently produce new infections primarily based on the detection telemetry of McAfee shoppers all over the world. This risk stays very lively.
Determine 1. “Rely Straightforward Calorie Calculator” was out there on Google Play on August 2022 and carries Android/Xamalicious
Android/Xamalicious trojans are apps associated to well being, video games, horoscope, and productiveness. Most of those apps are nonetheless out there for obtain in third-party marketplaces.
Beforehand we detected malware abusing Xamarin framework such because the open-sourced AndroSpy and forked variations of it, however Xamalicious is applied in another way. Technical particulars about Xamarin structure are nicely documented and element how .NET code is interpreted by Android utilizing Mono.
Acquiring Accessibility Companies
Let’s use the app “Numerology: Private horoscope & Quantity predictions” for instance. As soon as began it instantly requests the sufferer to allow accessibility companies for “right work” and offers instructions to activate this permission:
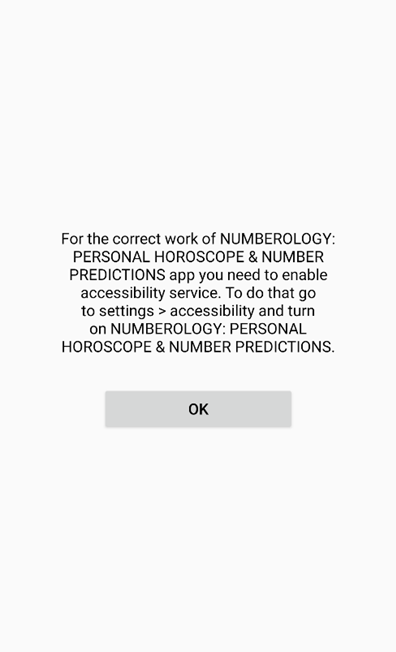
Determine 2. Tricking customers into granting accessibility companies permission
Customers must manually activate the accessibility companies after a number of OS warnings corresponding to the next on the accessibility choices:
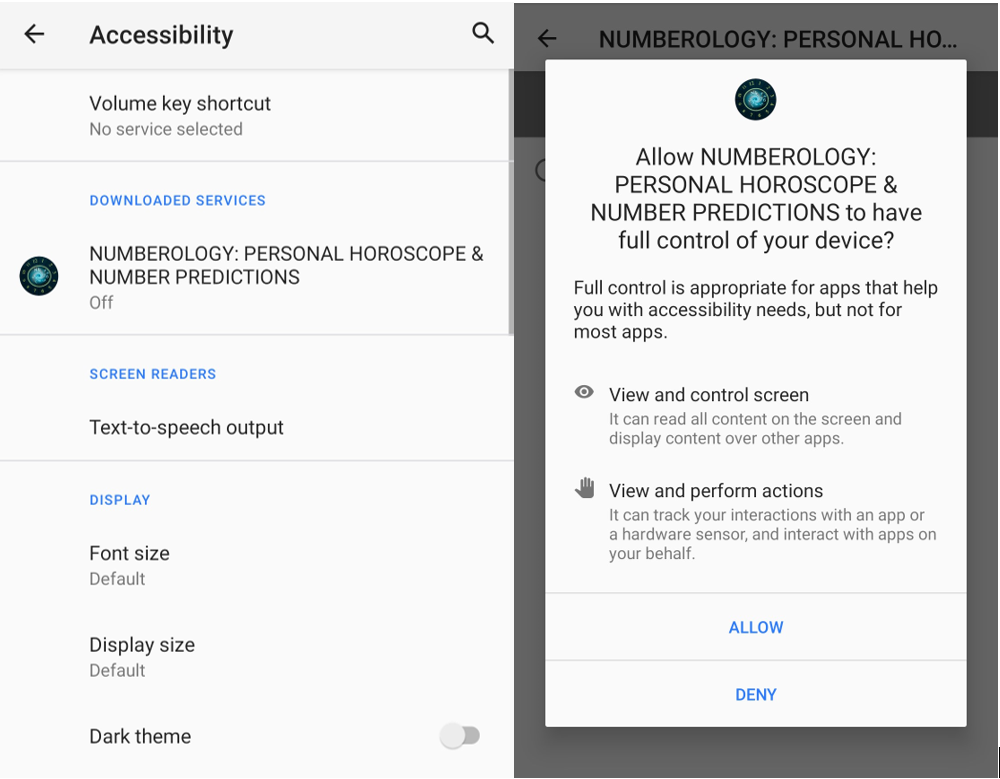
Determine 3. Accessibility companies configuration immediate highlights the dangers of this permission.
The place is the malicious code?
This isn’t the normal Java code or native ELF Android software, the malware module was written initially in .NET and compiled right into a dynamic hyperlink library (DLL). Then it’s LZ4 compressed, and it is perhaps embedded right into a BLOB file, or straight out there within the /assemblies listing on the APK construction. This code is loaded then by a local library (ELF) or by the DEX file at runtime stage. In easy phrases, because of this in some samples the reversing of the DLL assemblies is easy whereas in others it requires further steps to unpack them.
The malicious code is normally out there in two completely different meeting recordsdata within the /assemblies listing on the apk. Normally, file names are core.dll and a <package-specific>.dll.
Some malware variants has obfuscated the DLL assemblies to keep away from evaluation and reversing of the malicious code whereas others hold the unique code out there.
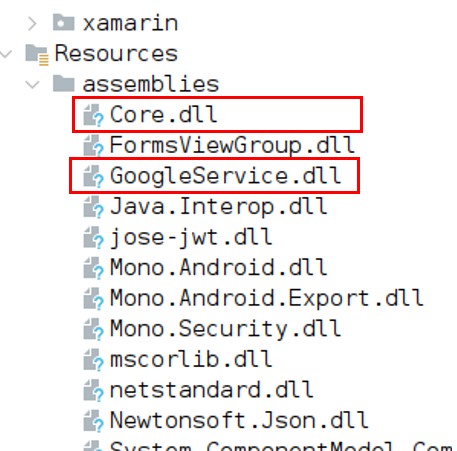
Determine 4. Core.dll and GoogleService.dll comprise malicious code.
Communication with the command-and-control server
As soon as accessibility permissions are granted the malware initiates communication with the malicious server to dynamically load a second-stage payload.
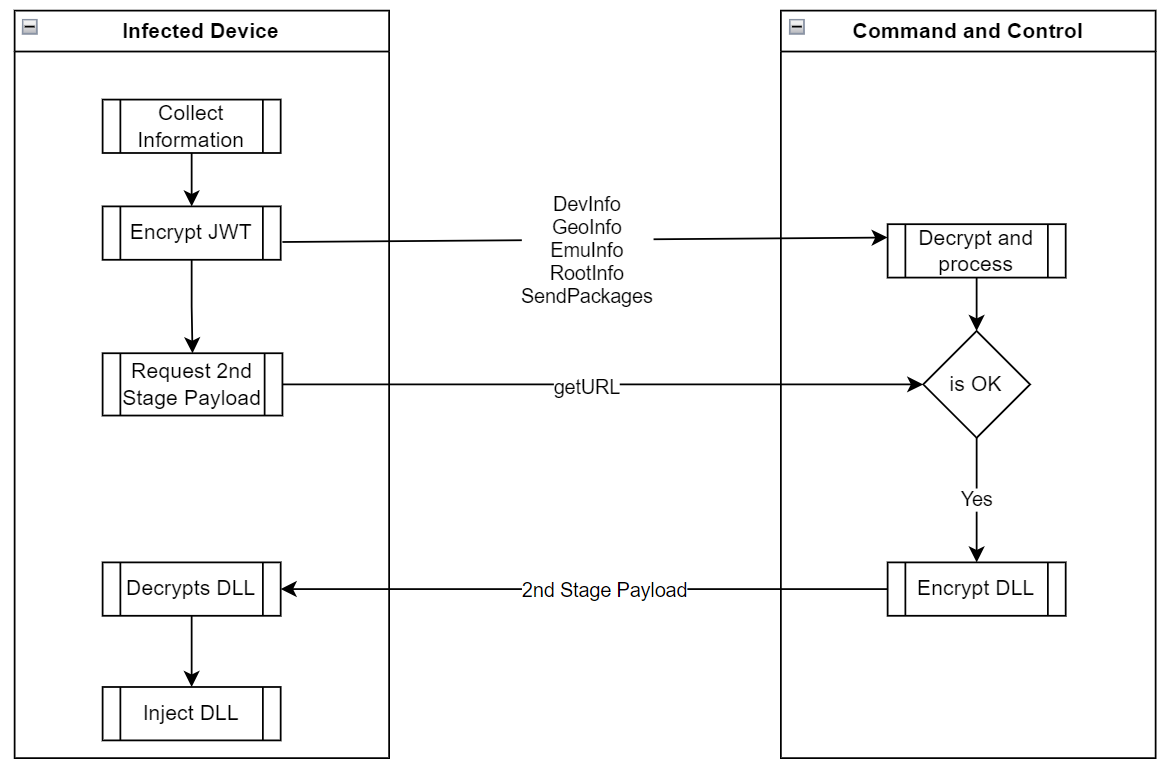
Determine 5. App execution and communication with the malicious server
Accumulate Machine Info
Android/Xamalicious collects a number of system information together with the checklist of put in functions obtained through system instructions to find out if the contaminated sufferer is an effective goal for the second stage payload. The malware can accumulate location, service, and community info amongst system rooting standing, adb connectivity configuration, as an example, if the system is linked through ADB or is rooted, the C2 won’t present a second-stage payload DLL for obtain.
| Technique/Command | Description |
| DevInfo | {Hardware} and system info that features:
|
| GeoInfo | Location of the system primarily based on IP handle, the malware contacts companies corresponding to api.myip.com to confirm the system location and ISP information.
FraudScore: Self-protection to establish if the system just isn’t an actual person |
| EmuInfo | It lists all adbProperties that in an actual system are round 640 properties. This checklist is encoded as a string param in URL encoded format.
This information could also be used to determinate if the affected consumer is an actual system or emulator because it incorporates params corresponding to:
|
| RootInfo | After making an attempt to establish if the system is rooted or not with a number of methods the output is consolidated on this command |
| Packages | It makes use of the system instructions “pm checklist packages -s” and “pm checklist packages -3” to checklist system and put in apps on the system. |
| Accessibility | It offers the standing if accessibility companies permissions are granted or not |
| GetURL | This command solely offers the Android Id and it’s a request for the second-stage payload. The C2 evaluates the offered consumer request and returns a standing and an encrypted meeting DLL. |
Information Encryption in JWT
To evade evaluation and detection, malware authors encrypted all communication and information transmitted between the C2 and the contaminated system, not solely protected by HTTPS, it’s encrypted as a JSON Net Encryption (JWE) token utilizing RSA-OAEP with a 128CBC-HS256 algorithm nevertheless the RSA key values utilized by the Xamalicious are hardcoded within the decompiled malicious DLL so decryption of transmitted info is feasible if C2 infrastructure is offered in the course of the evaluation.
Within the Ship() perform Android/Xamalicious first prepares the acquired object, normally a JSON construction calling the perform encrypt() which creates the JWT utilizing a hardcoded RSA key. So the info is exfiltrated totally encrypted to the malware host pointing to the trail “/Updater” through HTTP POST technique.
Then it waits for the C2 response and passes it to the decrypt() perform which has a hardcoded RSA non-public key to correctly decrypt the acquired command which could comprise a second stage payload for the “getURL” command.
Encrypt Technique:
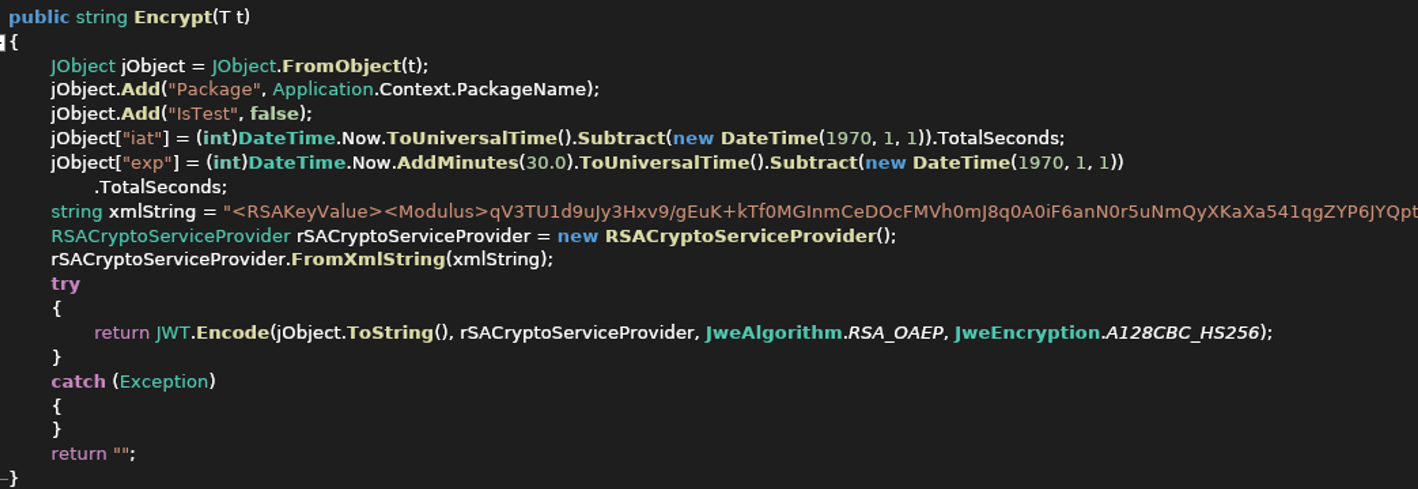
Determine 6. Encrypt perform with hardcoded RSA Key values as XML string
The decryption technique can also be hardcoded into malware which allowed the analysis crew to intercept and decrypt the communication from the C2 utilizing the RSA key values offered as XML string it’s doable to construct a certificates with the parameters to decrypt the JWE tokens content material.
C2 analysis
Collected information is transmitted to the C&C to find out if the system is a correct goal to obtain a second-stage payload. The self-protection mechanism of the malware authors goes past conventional emulation detection and nation code operator limitations as a result of on this case, the command-and-control server won’t ship the second stage payload if the system is rooted or linked as ADB through USB or doesn’t have a SIM card amongst a number of different surroundings validations.
DLL Customized Encryption
With the getURL command, the contaminated consumer requests the malicious payload, if the C&C Server determines that the system is “Okay” to obtain the malicious library it would encrypt a DLL with Superior encryption commonplace (AES) in Cipher block chaining (CBC) utilizing a customized key for the consumer that requested it primarily based on the system id and different parameters defined beneath to decrypt the code because it’s a symmetric encryption technique, the identical key works for encryption and decryption of the payload.
Delivers the Payload in JWT
The encrypted DLL is inserted as a part of the HTTP response within the encrypted JSON Net Token “JWT”. Then the consumer will obtain the token, decrypt it, after which decrypt the ‘url’ parm with AES CBC and a customized key.
The AES key used to decrypt the meeting is exclusive per contaminated system and its string of 32 chars of size incorporates appended the system ID, model, mannequin, and a hardcoded padding of “1” as much as 32 chars of size.
For example, if the system ID is 0123456ABCDEF010 and the affected system is a Pixel 5, then the AES secret is: “0123456ABCDEF010googlePixel 5111”
Which means that the DLL has a number of layers of encryption.
- It’s a HTTPS protected.
- It’s encrypted as a JWE Token utilizing RSA-OAEP with a 128CBC-HS256 algorithm.
- URL parameter that incorporates the DLL is encrypted with AES and encoded as base64
All these efforts are associated to hiding the payload and making an attempt to remain beneath the radar the place this risk had relative success since some variants may need been lively years in the past with out AV detections.
DLL Injected
Xamalicious will title this DLL “cache.bin” and retailer it within the native system to lastly dynamically load it utilizing the Meeting.Load technique.
As soon as the second stage payload has been loaded the system will be totally compromised as a result of as soon as accessibility permissions are granted, it will probably obverse and work together with any exercise opening a backdoor to any sort of malicious exercise.
Through the evaluation, the downloaded second stage payload contained a DLL with the category “MegaSDKXE” which was obfuscated and incomplete in all probability as a result of the C2 didn’t obtain the anticipated params to offer the entire malicious second stage that is perhaps restricted to a particular service, language, app put in, location, time zone or unknown circumstances of the affected system, nevertheless, we will guarantee that this can be a high-risk backdoor that leaves the likelihood to dynamically execute any command on the affected system not restricted to spying, impersonation or as a financially motivated malware.
Money Magnet Advert-Fraud and Xamalicious
One of many Xamalicious samples detected by McAfee Cellular generic signatures was “LetterLink” (com.regaliusgames.llinkgame) which was out there on Google Play on the finish of 2020, with a ebook icon. It was poorly described as a hidden model of “Money Magnet”: An app that performs ad-fraud with automated clicker exercise, apps downloads, and different duties that result in monetization for affiliate internet marketing. This software presents customers factors which might be purported to be redeemable by retail reward playing cards or cryptocurrency.
Determine 8a. LetterLink login web page after operating the app for the primary time.
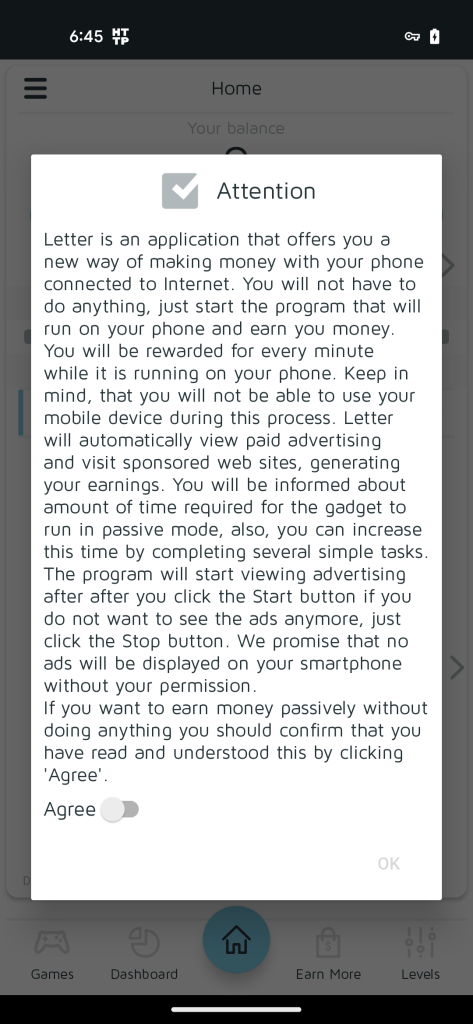
Determine 8b. LetterLink settlement for Money Magnet
Initially printed in 2019 on Google Play, “Money Magnet” (com.uicashmagnet) was described as a passive revenue software providing customers to earn as much as $30 USD monthly operating automated advertisements. Because it was eliminated by Google the authors then infiltrated LetterLink and extra just lately “Dots: One Line Connector” (com.orlovst.dots) that are hidden variations of the identical ad-fraud scheme.

Determine 9. LetterLink Icon that hides Money Magnet
“LetterLink” performs a number of Xamalicious actions because it incorporates the “core.dll” library, it connects to the identical C2 server, and it makes use of the identical hardcoded non-public RSA certificates to construct the JWE encrypted tokens which offer a non-repudiation proof that the builders of Money Magnet are behind Xamalicious.
Determine 10. Money Magnet infiltrated the app as a Sport, out there till the tip of 2023
“Dots: One Line Connector” app just isn’t a sport, the screenshot printed by Google Play doesn’t correspond to the appliance conduct as a result of as soon as it’s began it simply asks for authentication credentials with none emblem or reference to Money Magnet. “Dots” doesn’t comprise the identical DLLs as its predecessor, nevertheless the communication with the C2 is analogous utilizing the identical RSA key parameters. We reported this app to Google they usually promptly eliminated it from Google Play.
Affected Customers
Based mostly on our telemetry we noticed that extra affected customers are within the American continent with probably the most exercise within the USA, Brazil, and Argentina. In Europe, shoppers additionally reported the an infection, particularly within the UK, Spain, and Germany.

Determine 11. McAfee detections Android/Xamalicious all over the world
Conclusion
Android functions written in non-java code with frameworks corresponding to Flutter, react native and Xamarin can present an extra layer of obfuscation to malware authors that deliberately decide these instruments to keep away from detection and attempt to keep beneath the radar of safety distributors and hold their presence on apps markets.
Keep away from utilizing apps that require accessibility companies except there’s a real want to be used. If a brand new app tries to persuade you to activate accessibility companies claiming that it’s required and not using a actual and affordable motive and requesting to disregard the operative system warning, then it’s a purple flag.
The second stage payload would possibly take management of the system as a result of accessibility permissions are granted so every other permission or motion can then be carried out by the malware if these directions are offered within the injected code.
As a result of it’s tough for customers to actively take care of all these threats, we strongly advocate that customers set up safety software program on their gadgets and all the time hold updated. By utilizing McAfee Cellular Safety merchandise, customers can additional safeguard their gadgets and mitigate the dangers linked with these sorts of malware, offering a safer and safer expertise.
Android/Xamalicious Samples Distributed on Google Play:
| Bundle Identify | App Identify | Installs |
| com.anomenforyou.essentialhoroscope | Important Horoscope for Android | 100,000 |
| com.littleray.skineditorforpeminecraft | 3D Pores and skin Editor for PE Minecraft | 100,000 |
| com.vyblystudio.dotslinkpuzzles | Emblem Maker Professional | 100,000 |
| com.autoclickrepeater.free | Auto Click on Repeater | 10,000 |
| com.lakhinstudio.counteasycaloriecalculator | Rely Straightforward Calorie Calculator | 10,000 |
| com.muranogames.easyworkoutsathome | Sound Quantity Extender | 5,000 |
| com.regaliusgames.llinkgame | LetterLink | 1,000 |
| com.Ushak.NPHOROSCOPENUMBER | NUMEROLOGY: PERSONAL HOROSCOPE &NUMBER PREDICTIONS | 1,000 |
| com.browgames.stepkeepereasymeter | Step Keeper: Straightforward Pedometer | 500 |
| com.shvetsStudio.trackYourSleep | Monitor Your Sleep | 500 |
| com.devapps.soundvolumebooster | Sound Quantity Booster | 100 |
| com.Osinko.HoroscopeTaro | Astrological Navigator: Each day Horoscope & Tarot | 100 |
| com.Potap64.universalcalculator | Common Calculator | 100 |
Indicators of Compromise
|

